Synthetic Asset
Synthetic Asset: Creating Anything on Blockchain
Synthetic assets are blockchain tokens that track the value of real-world assets like stocks, commodities, or currencies. They’re like financial derivatives but programmable and globally accessible.
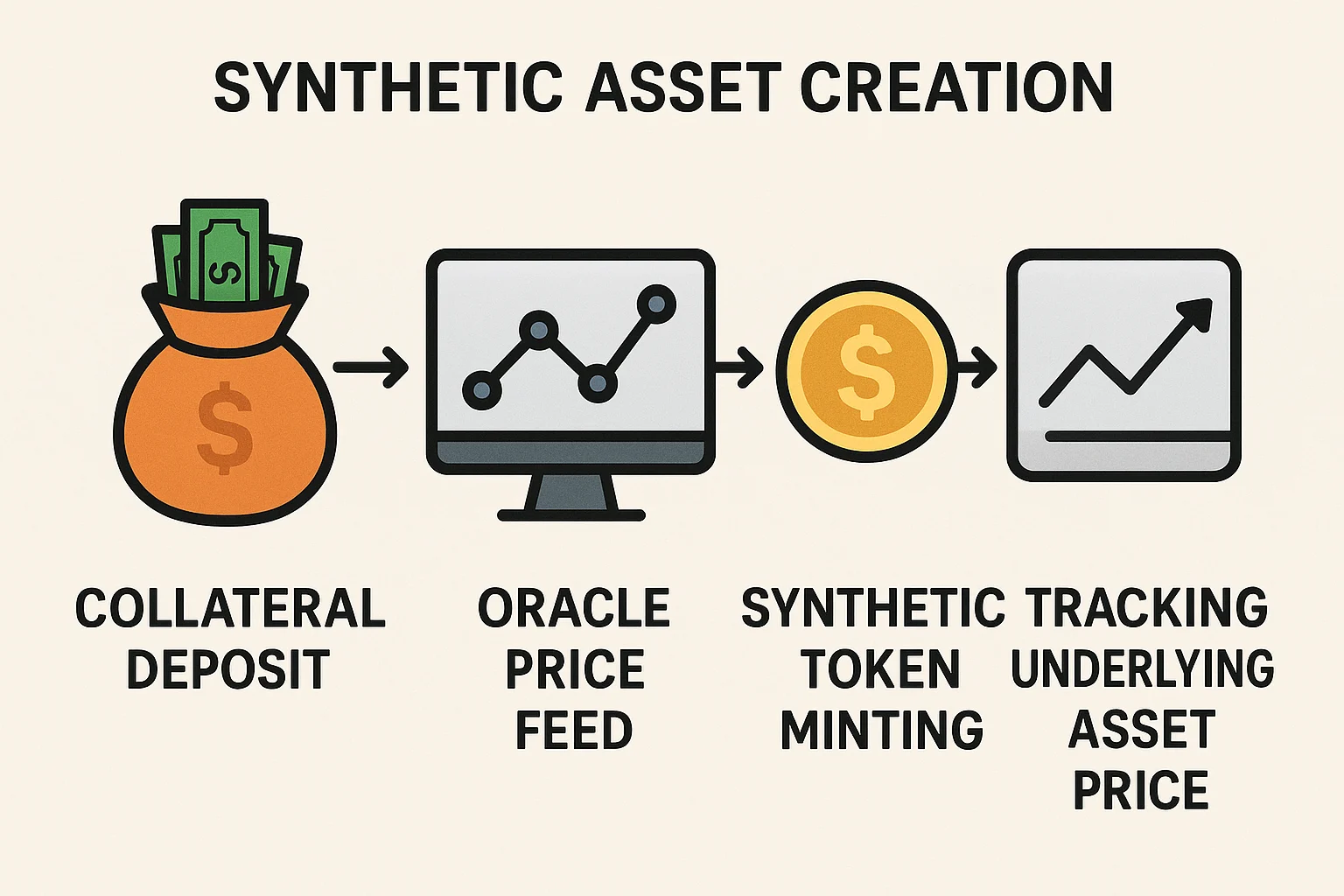
A synthetic asset is a tokenized derivative that tracks the price of an underlying asset without requiring direct ownership of that asset. Smart contracts use price feeds to maintain the synthetic’s value relative to its underlying reference.
How Synthetic Assets Work
Price oracles provide real-time data about underlying assets, enabling smart contracts to maintain accurate pegs between synthetics and their targets.
Collateralization backs synthetic assets with cryptocurrency deposits, often over-collateralized to account for price volatility and ensure redemption capability.
Liquidation mechanisms protect the system when collateral values fall too low, automatically selling collateral to maintain backing ratios.
Real-World Examples
- Synthetix creates synthetic stocks, commodities, and currencies backed by SNX token collateral
- Mirror Protocol offers synthetic U.S. stocks accessible globally without traditional brokerage accounts
- UMA enables creation of custom synthetic assets for any trackable data feed
Why Beginners Should Care
Global access to traditional assets through synthetics bypasses geographic restrictions and traditional financial gatekeepers that limit investment options.
24/7 trading of synthetic stocks and commodities provides constant market access unlike traditional markets with limited hours and holidays.
Regulatory uncertainty surrounds synthetic assets as they may be classified as securities in some jurisdictions, affecting their availability and legal status.
Related Terms: Oracle, Collateral, Price Feed, Derivatives
