Preconfirmation (Pre-confirm)
Preconfirmation (Pre-confirm): Faster Transaction Guarantees
Preconfirmations provide early guarantees that transactions will be included in upcoming blocks before final confirmation. It’s like getting a reservation confirmation before the restaurant officially opens.
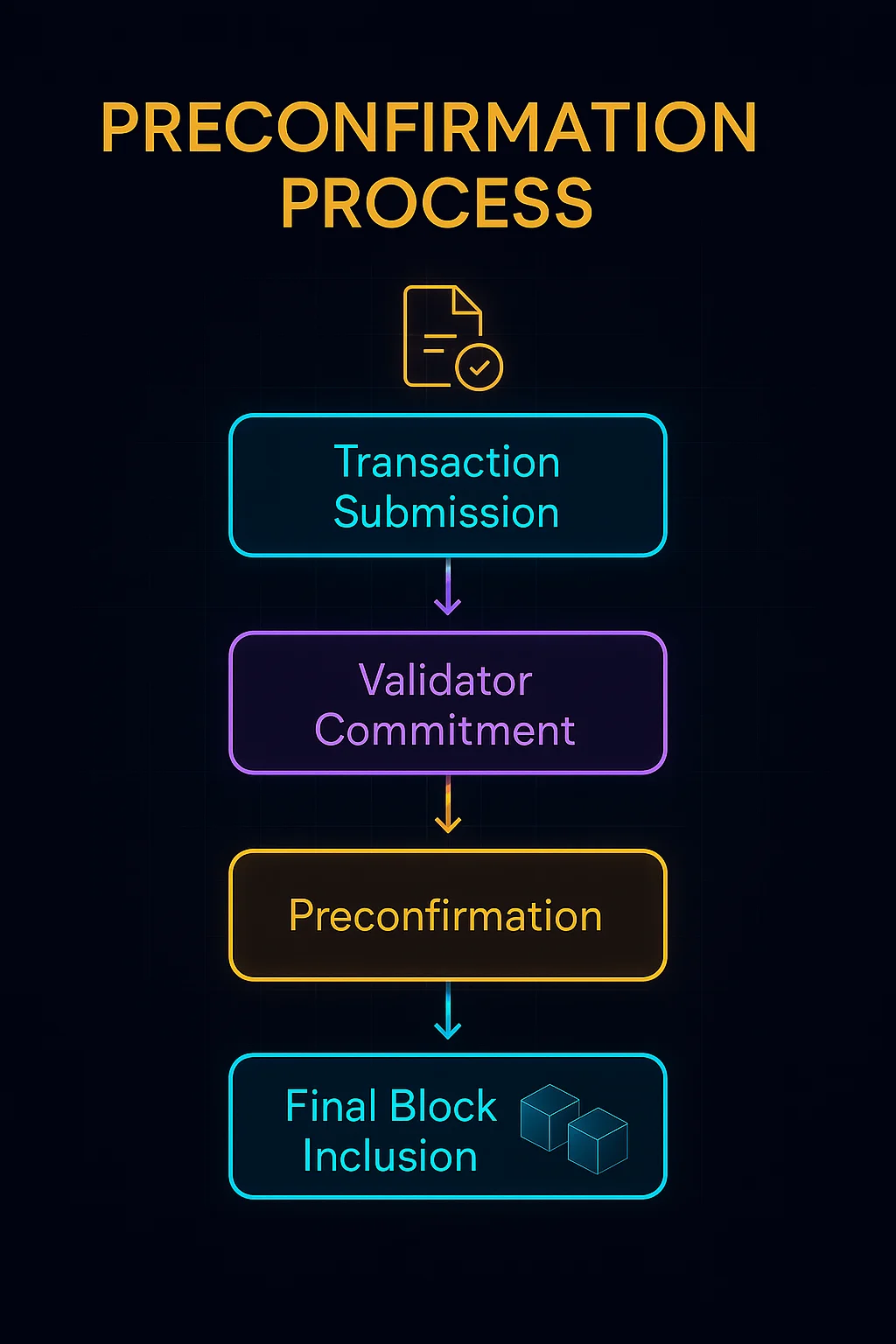
Preconfirmation is a mechanism where validators or sequencers provide early commitments to include specific transactions in future blocks. This reduces user-perceived latency by providing execution guarantees before final settlement.
How Preconfirmations Work
Early commitments from validators signal intent to include transactions in their next block, providing users with confidence about execution timing.
Economic bonds often back preconfirmation promises, with validators facing penalties if they fail to include preconfirmed transactions.
Reduced uncertainty enables applications to provide better user experiences by showing transaction status before final blockchain confirmation.
Real-World Examples
- Layer 2 sequencers provide preconfirmations for faster user feedback on rollup transactions
- MEV-Boost implementations experiment with preconfirmation mechanisms for Ethereum
- Application-specific chains often implement preconfirmations for improved user experience
Why Beginners Should Care
Faster feedback improves user experience by reducing perceived transaction latency even when final confirmation takes the same time.
Trust assumptions require believing that validators will honor their preconfirmation commitments rather than waiting for cryptographic finality.
Implementation complexity makes preconfirmations challenging to implement correctly without introducing new attack vectors or centralization risks.
Related Terms: Block Confirmation, Finality, Sequencer
