Chain Abstraction
Chain Abstraction: Invisible Multi-Chain Experience
Chain abstraction hides blockchain complexity from users, making multi-chain interactions feel like using a single network. It’s like having universal currency that works everywhere without exchange rates.
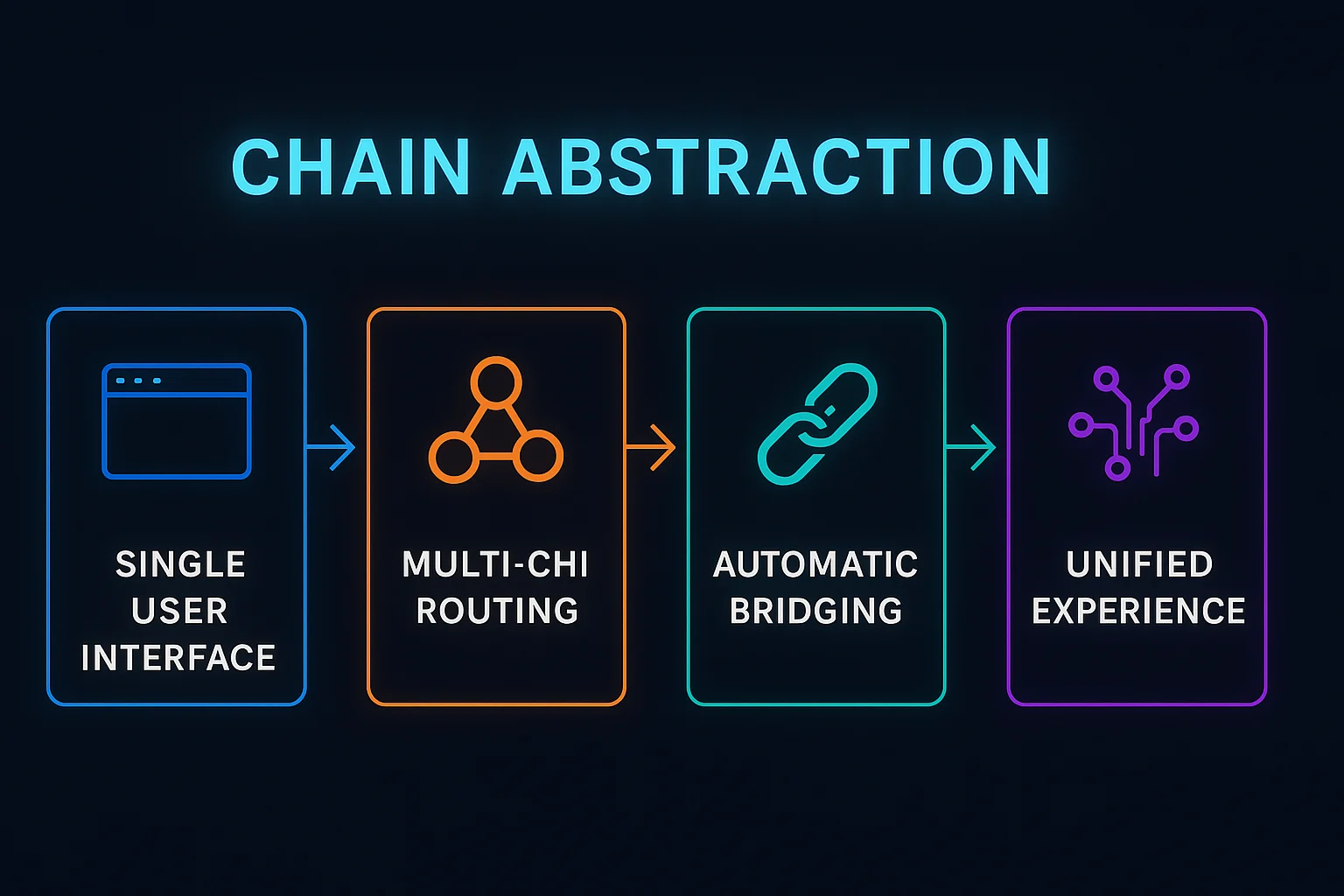
Chain abstraction creates user experiences where interactions with multiple blockchains happen seamlessly without users needing to understand or manage different networks, tokens, or bridges. Applications handle all cross-chain complexity behind the scenes.
How Chain Abstraction Works
Unified interfaces present single user experiences while automatically routing transactions across multiple chains based on cost, speed, or liquidity optimization.
Automatic bridging handles cross-chain asset movement transparently, executing complex multi-step operations through simple user actions.
Gas abstraction enables paying transaction fees with any token while the system handles conversions and payments on the appropriate networks.
Real-World Examples
- Socket provides intent-based routing across chains for seamless user experiences
- Li.Fi aggregates bridges and chains to create unified cross-chain interactions
- Various wallet improvements that hide chain switching and bridging complexity
Why Beginners Should Care
Simplified onboarding eliminates the need to understand different networks, acquire gas tokens, or manage bridge operations manually.
Improved adoption potential as mainstream users can access multi-chain benefits without technical blockchain knowledge.
Hidden complexity may reduce user understanding of underlying risks like bridge security or network dependencies.
Related Terms: Cross-Chain, Intent-Based, Bridge Aggregator
