Appchain
Appchain: Application-Specific Blockchains
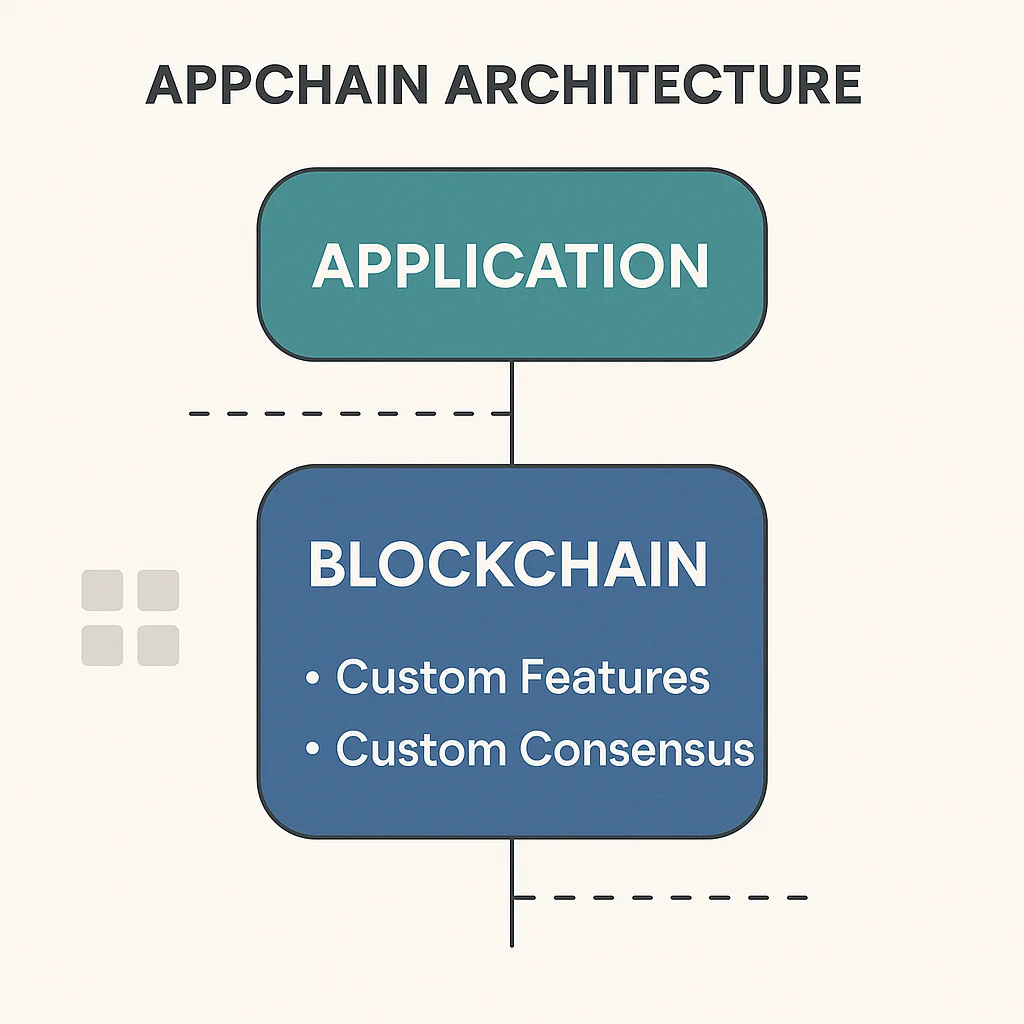
Appchains are blockchains designed for single applications or use cases rather than general-purpose smart contracts. They’re like having a dedicated highway for one type of vehicle instead of mixed traffic.
An appchain is a blockchain optimized for a specific application or use case rather than supporting general-purpose smart contracts. This specialization enables better performance, lower costs, and features tailored to specific needs.
How Appchains Work
Single-purpose optimization allows appchains to remove unnecessary features and optimize for specific use cases like gaming, payments, or social media.
Custom consensus mechanisms can be designed for specific application requirements rather than using generic blockchain consensus suitable for all applications.
Direct value capture enables applications to capture MEV and transaction fees directly rather than paying them to general-purpose blockchain validators.
Real-World Examples
- DYdX v4 runs on its own appchain optimized for derivatives trading
- Immutable X provides a gaming-focused chain with NFT-optimized features
- Cosmos ecosystem enables easy appchain creation through the Cosmos SDK
Why Beginners Should Care
Better performance from specialization can provide faster transactions, lower fees, and features impossible on general-purpose chains.
Sovereignty benefits give applications full control over their blockchain parameters, governance, and economic models.
Fragmentation concerns as appchains may reduce composability and liquidity compared to applications sharing common infrastructure.
Related Terms: Cosmos, Sovereignty, Application Layer,
