Phishing Attack
Phishing Attack: How Scammers Steal Your Crypto
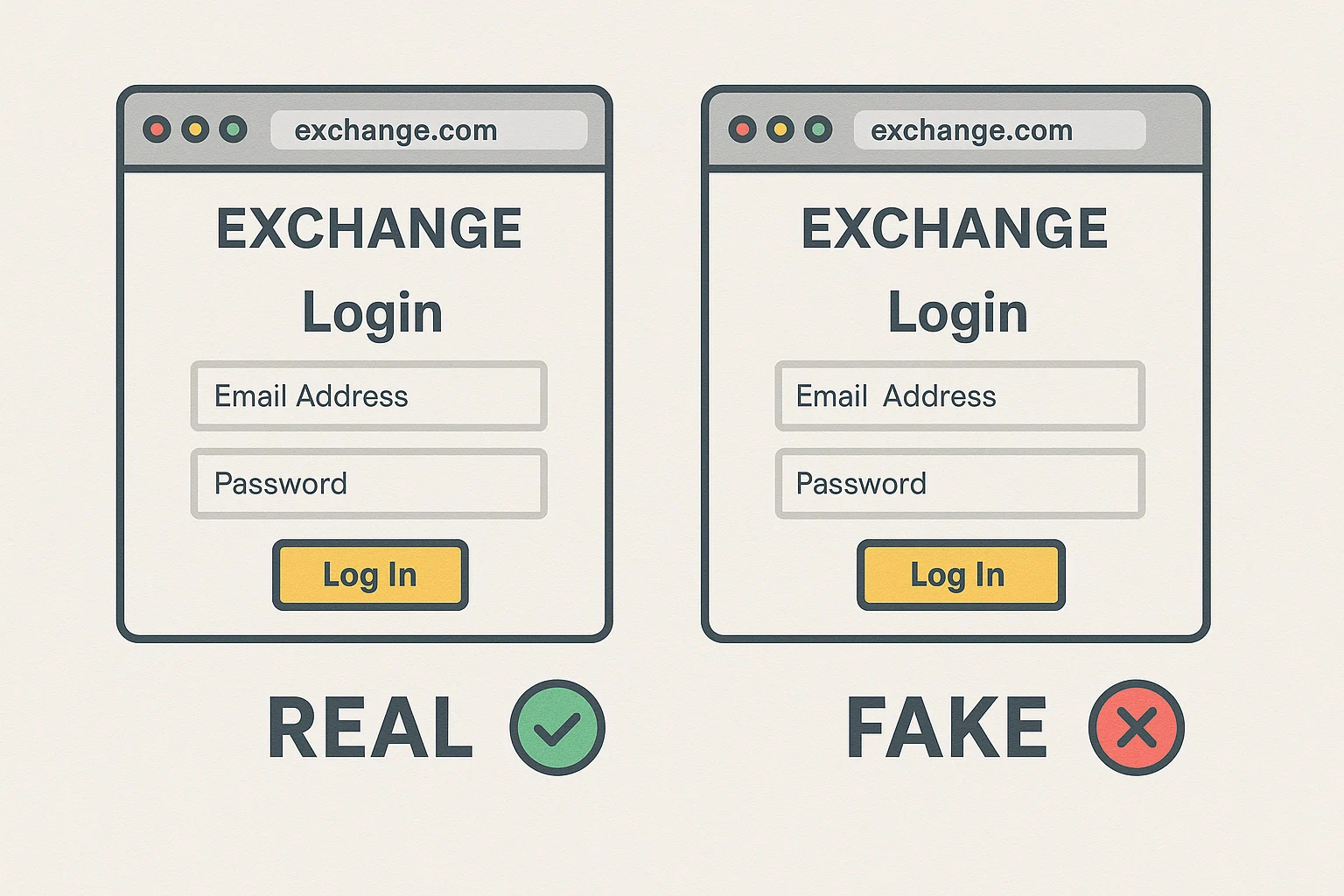
Phishing attacks are the #1 way people lose crypto. Scammers create fake websites that look identical to real ones, then steal your login credentials and private keys.
A phishing attack is a fraudulent attempt to obtain sensitive information by impersonating a trustworthy entity through fake websites, emails, or messages. In crypto, this usually means fake exchange login pages or wallet connection prompts that steal your credentials.
How Phishing Attacks Work
Fake websites that look identical to popular exchanges or DeFi platforms trick users into entering their passwords or connecting their wallets. The scammer captures this information and drains accounts immediately.
Social engineering often precedes the technical attack. Scammers send urgent emails about “account verification” or “security breaches” to create panic and rush victims into clicking malicious links.
Browser extensions and mobile apps can also be phishing tools, designed to capture wallet interactions and steal private keys when users think they’re using legitimate software.
Real-World Examples
- Fake MetaMask extensions in browser stores that steal wallet seeds
- Impersonator emails claiming to be from Coinbase requiring “immediate action”
- Fake DeFi platforms offering impossible yields to lure in victims
Why Beginners Should Care
Crypto transactions are irreversible. Once scammers have your private keys or drain your accounts, there’s no customer service to call, no bank to reverse charges.
Always verify URLs carefully – scammers use similar domains like “craken.com” instead of “kraken.com”. Bookmark legitimate sites and use those bookmarks instead of clicking email links.
Enable two-factor authentication and use hardware wallets to add extra security layers that make phishing attacks much harder to execute successfully.
Related Terms: Two-Factor Authentication, Hardware Wallet, Private Key, Rug Pull
