Rehypothecation
Rehypothecation: Reusing Collateral Multiple Times
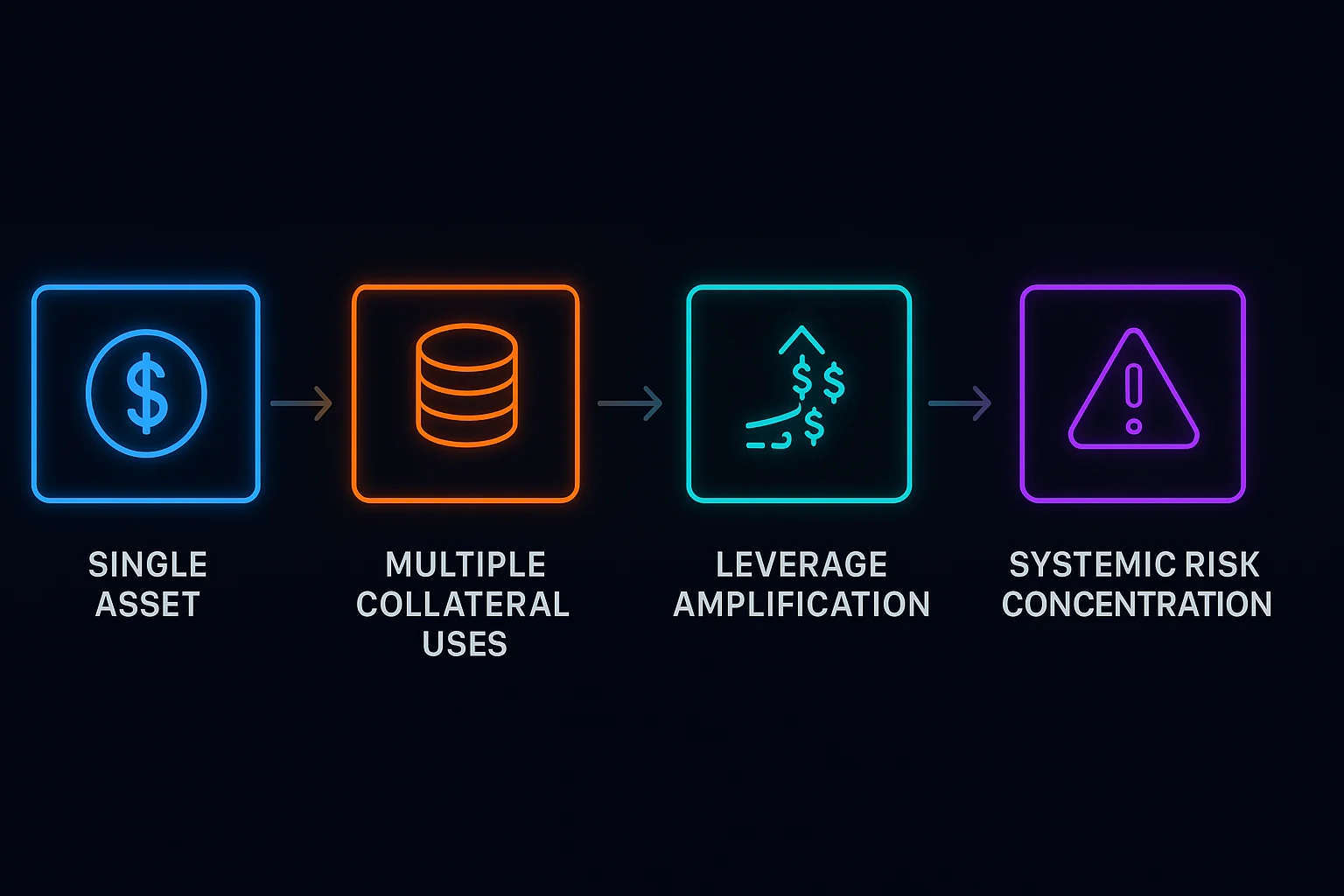
Rehypothecation involves using the same collateral to back multiple obligations simultaneously. It’s like using your house as collateral for three different loans at the same time.
Rehypothecation is the practice of using customer assets as collateral for the institution’s own borrowing or trading activities. In DeFi, this creates leverage and capital efficiency but increases systemic risk.
How Rehypothecation Works
Collateral reuse allows deposited assets to be lent out or used as backing for additional positions, creating multiple claims on the same underlying assets.
Leverage amplification enables institutions to take larger positions than their actual capital would normally allow through reusing customer deposits.
Chain reactions can occur when asset values decline, triggering margin calls across multiple positions backed by the same underlying collateral.
Real-World Examples
- Celsius allegedly rehypothecated customer deposits for high-risk trading activities before bankruptcy
- Traditional finance has used rehypothecation extensively, contributing to the 2008 financial crisis
- Some DeFi protocols enable rehypothecation-like mechanics through recursive borrowing
Why Beginners Should Care
Hidden leverage in the system that may not be apparent until market stress reveals the extent of rehypothecation.
Counterparty risk increases when your deposits are being used to back other people’s risky positions without your knowledge.
Regulatory attention as rehypothecation practices often violate customer protection laws in traditional finance.
Related Terms: Leverage, Counterparty Risk, Systemic Risk, Asset Rehypothecation
