Tokenomics
Tokenomics: The Economics of Digital Assets
Tokenomics determines how cryptocurrencies create, distribute, and maintain value over time. It’s the difference between digital money and digital monopoly money.
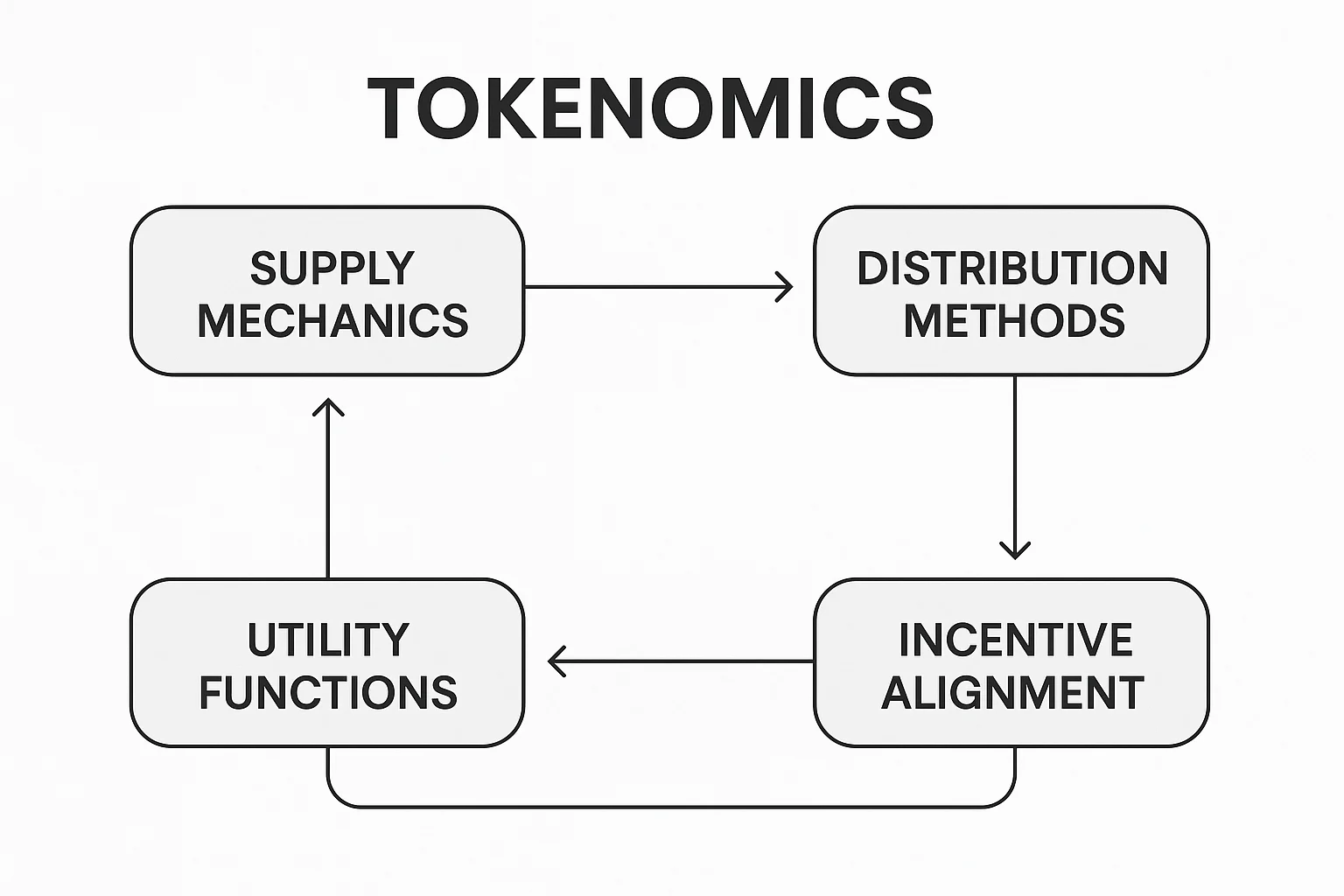
Tokenomics refers to the economic design and mechanics of a cryptocurrency token, including supply schedules, distribution methods, utility functions, and incentive structures. Good tokenomics align stakeholder interests while bad tokenomics create unsustainable systems that collapse.
How Tokenomics Work
Supply mechanics control how many tokens exist, how fast new ones are created, and whether the total supply is fixed, inflationary, or deflationary over time.
Distribution methods determine who gets tokens and when – through mining, staking, airdrops, team allocations, or public sales. Fair distribution prevents excessive concentration.
Utility design gives tokens practical uses beyond speculation, such as governance voting, fee payments, staking rewards, or access to platform features.
Real-World Examples
- Bitcoin’s fixed supply of 21 million creates scarcity and deflationary pressure
- Ethereum’s fee burning through EIP-1559 makes ETH deflationary during high usage
- Failed ICO tokens from 2017-2018 had poor tokenomics with no real utility
Why Beginners Should Care
Investment success depends heavily on tokenomics since tokens with sustainable economics tend to hold value better than those with flawed incentive structures.
Red flags include excessive team allocations, infinite inflation, no clear utility, or mechanics that only benefit early adopters at the expense of later participants.
Long-term viability requires tokenomics that encourage participation, reward value creation, and maintain network security as projects mature and market conditions change.
Related Terms: Token Supply, Inflation, Utility Token, Token Distribution
