Rug Detector
Rug Detector: Automated Scam Identification
Rug detectors are tools that analyze token contracts and trading patterns to identify potential rug pulls before they happen. They’re like having a fraud investigator built into your trading interface.
A rug detector is software that automatically analyzes cryptocurrency projects for red flags that indicate potential rug pulls or exit scams. These tools examine smart contract code, tokenomics, and trading patterns to warn users about suspicious projects.
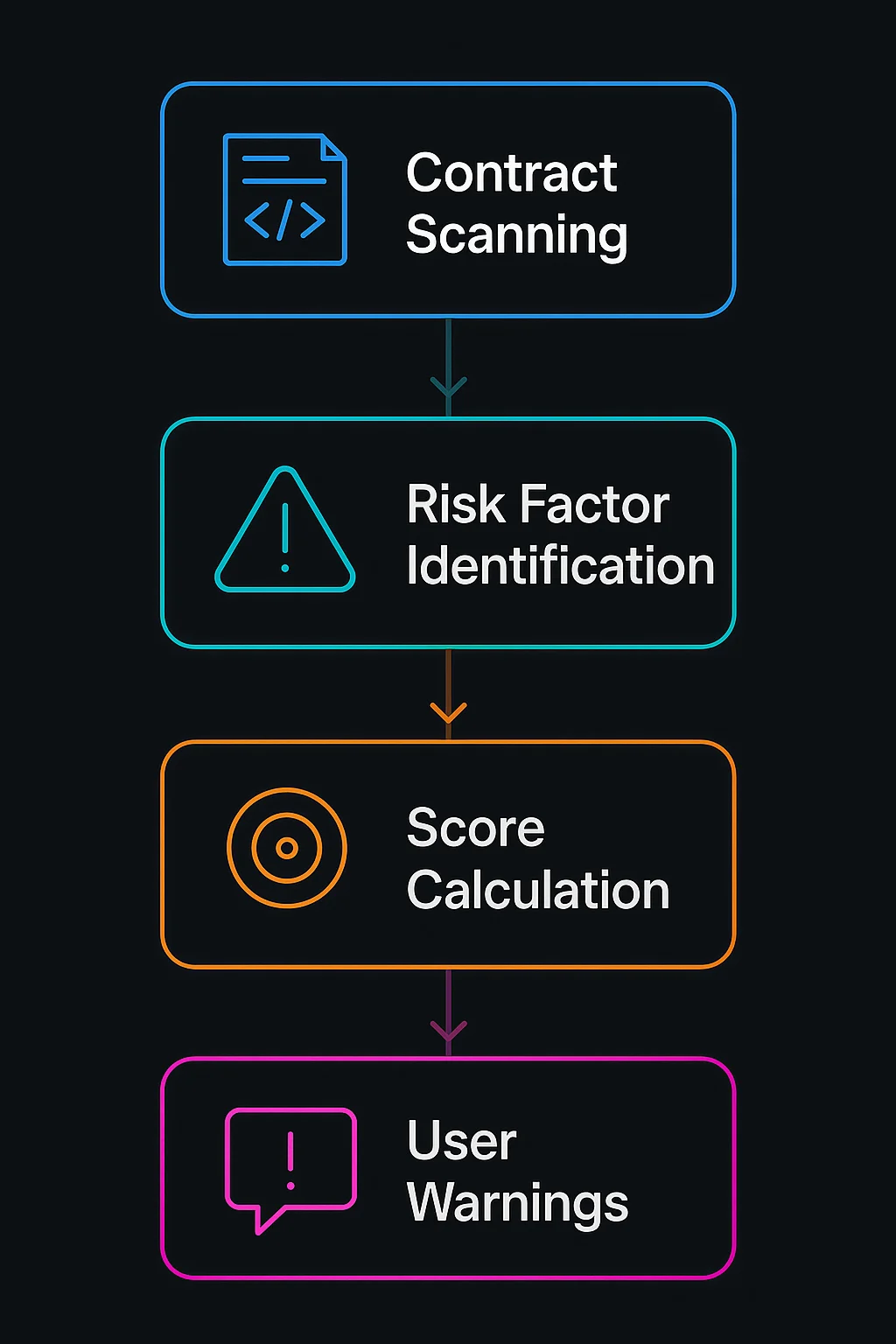
How Rug Detectors Work
Contract analysis examines smart contract code for hidden functions, unlimited minting capabilities, or liquidity extraction mechanisms that enable rug pulls.
Pattern recognition identifies suspicious trading activities like concentrated token ownership, locked liquidity timeframes, or unusual price movements.
Risk scoring combines multiple factors into overall risk assessments that help users make informed decisions about project legitimacy.
Real-World Examples
- Token Sniffer analyzes BSC and Ethereum tokens for rug pull indicators
- RugDoc provides detailed project audits and risk assessments
- DexTools integrates rug detection features into trading interfaces
Why Beginners Should Care
Early warning system for potentially fraudulent projects before significant community losses occur.
False positives can incorrectly flag legitimate projects, requiring users to understand analysis limitations and conduct additional research.
Evolving threats as scammers adapt to detection methods, requiring continuous updates to rug detection algorithms and risk factors.
Related Terms: Rug Pull, Smart Contract Analysis, Due Diligence, Risk Assessment
