Liquidity Bootstrapping
Liquidity Bootstrapping: Fair Token Launch Mechanism
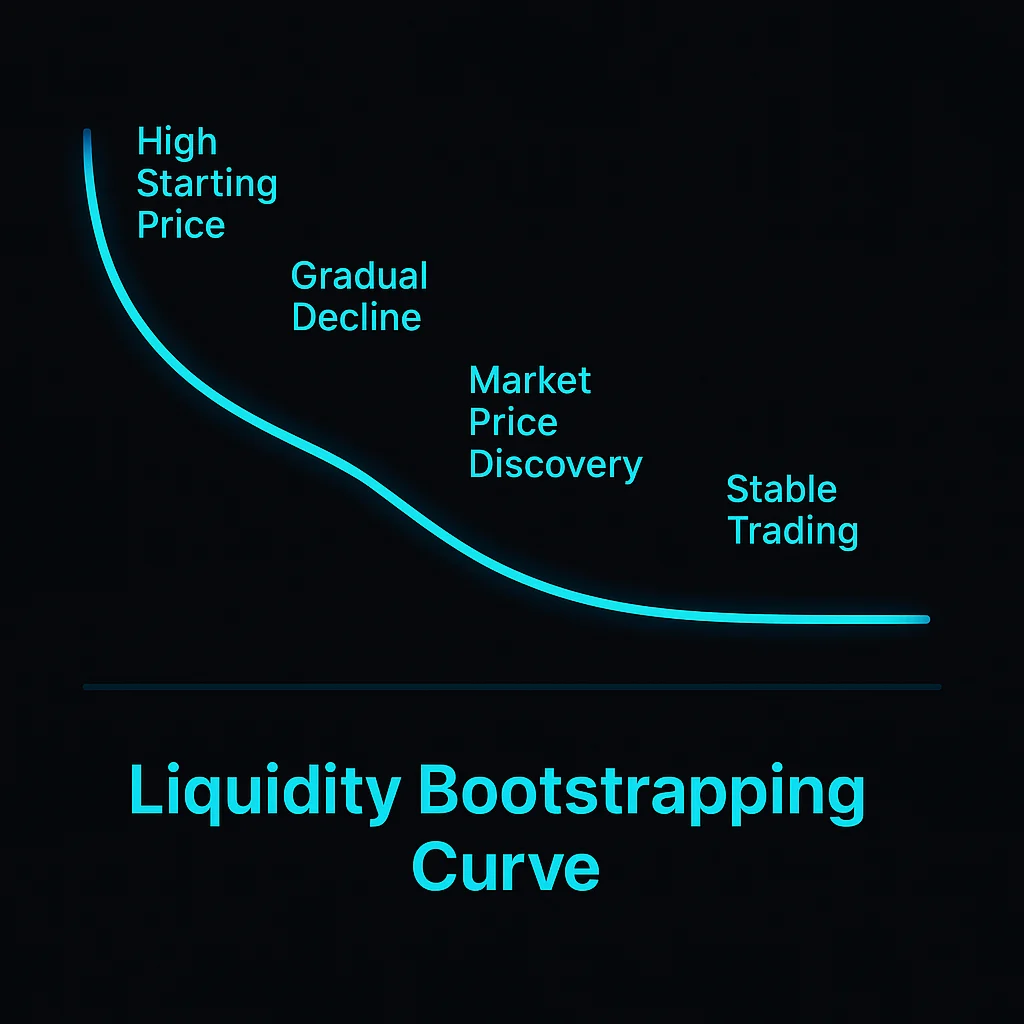
Liquidity bootstrapping uses gradually declining prices to enable fair token distribution while building trading liquidity. It’s like having a reverse auction that creates a fair market price.
Liquidity bootstrapping is a token launch mechanism that starts with high prices that gradually decrease over time, allowing market forces to discover fair value while building trading liquidity. This prevents bots from capturing all tokens at launch.
How Liquidity Bootstrapping Works
Descending price auctions start with high token prices that automatically decrease until market demand matches the declining price curve.
Automated market making provides continuous liquidity throughout the price discovery process rather than relying on order book matching.
Bot resistance through high initial prices and gradual decreases makes it unprofitable for bots to extract value from early price inefficiencies.
Real-World Examples
- Balancer LBPs have launched hundreds of projects with fair price discovery mechanisms
- Copper Launch provides liquidity bootstrapping infrastructure for new tokens
- Major DeFi projects use LBPs to avoid the problems of traditional fixed-price token sales
Why Beginners Should Care
Fairer distribution compared to fixed-price sales where bots often capture most tokens before regular users can participate.
Price discovery through market mechanisms rather than arbitrary pricing by project teams who may not understand market demand.
Participation timing flexibility allows users to buy at any point during the bootstrap period rather than competing for limited fixed-price allocations.
Related Terms: Token Launch, Price Discovery, Fair Distribution, Automated Market Maker
