Reentrancy Attack
Reentrancy Attack: Exploiting Function Recursion
Reentrancy attacks exploit smart contracts by repeatedly calling functions before previous executions complete. It’s like withdrawing money from an ATM that forgets to update your balance between transactions.
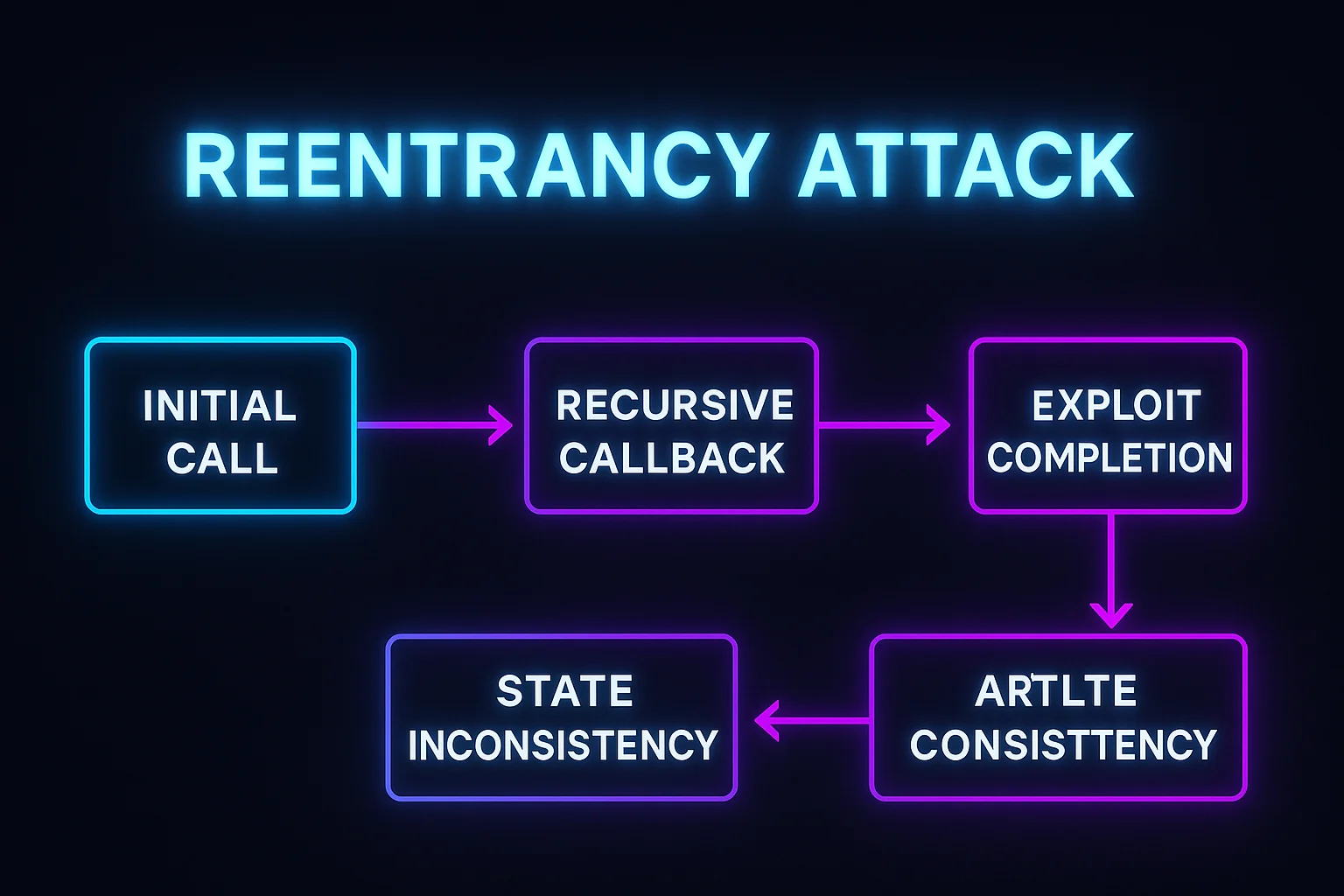
A reentrancy attack is a smart contract exploit where malicious contracts repeatedly call vulnerable functions before state changes are finalized, potentially draining funds or manipulating contract behavior. These attacks exploit the order of operations in smart contract execution.
How Reentrancy Attacks Work
Recursive calling involves malicious contracts that call back into vulnerable functions during the execution of those same functions, before state updates complete.
State manipulation occurs when contracts check balances or conditions that haven’t been updated yet, allowing attackers to perform actions multiple times.
Fund drainage happens when withdrawal functions can be called repeatedly before balance updates, enabling attackers to withdraw more than their actual holdings.
Real-World Examples
- The DAO hack in 2016 used reentrancy to drain $60 million, leading to Ethereum’s hard fork
- Various DeFi exploits have used reentrancy to steal millions from poorly secured protocols
- Cream Finance lost $37 million to a reentrancy attack combined with other vulnerabilities
Why Beginners Should Care
Smart contract risk understanding helps evaluate protocol security and the importance of professional audits before using new platforms.
Prevention awareness shows why established protocols with battle-tested code tend to be safer than new, unaudited projects.
Recovery impossibility since blockchain transactions can’t be reversed, making prevention the only protection against reentrancy exploits.
Related Terms: Smart Contract, Smart Contract Audit, DeFi Security, Exploit
