DeFi Composability
DeFi Composability: Building Block Finance
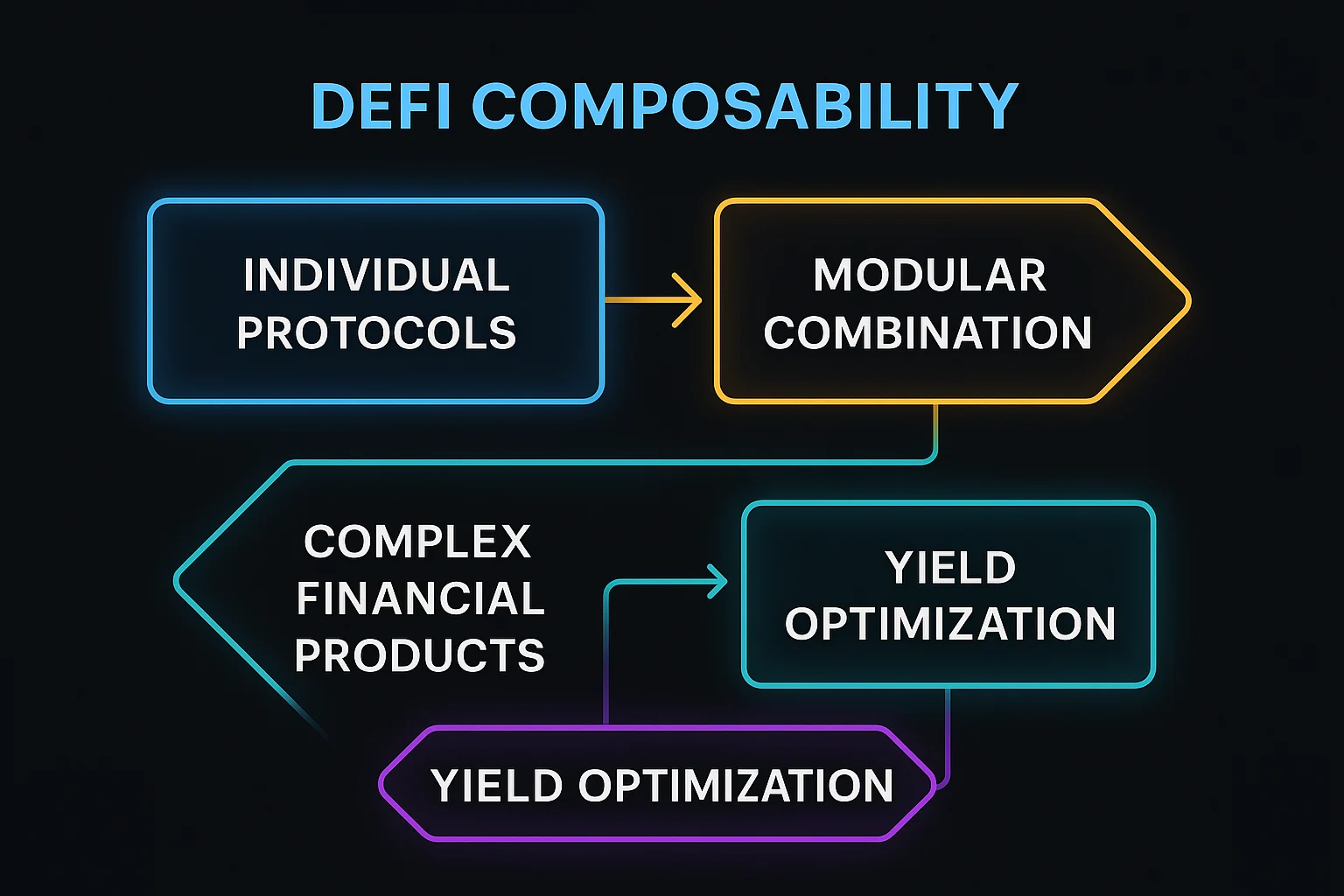
DeFi composability allows protocols to integrate seamlessly, creating complex financial products by combining simpler components. It’s like financial Lego blocks that snap together perfectly.
DeFi composability refers to the ability of decentralized finance protocols to interact and build upon each other, creating more complex financial products through modular integration. This enables innovation through combining existing building blocks.
How DeFi Composability Works
Standardized interfaces like ERC-20 tokens and common smart contract patterns enable protocols to interact without custom integration work.
Permissionless innovation allows anyone to build on existing protocols without asking permission, creating rapid ecosystem development.
Yield stacking combines multiple protocols to optimize returns, such as lending tokens that earn yield while being used as collateral elsewhere.
Real-World Examples
- Yearn Finance combines lending, farming, and trading protocols to optimize yields automatically
- Convex Finance builds on Curve to enhance liquidity mining rewards
- Index protocols create diversified portfolios using multiple DeFi primitives
Why Beginners Should Care
Innovation acceleration as new protocols can leverage existing infrastructure rather than rebuilding everything from scratch.
Systemic risks from interconnected protocols where failures can cascade across multiple applications and user positions.
Complexity management becomes crucial as composed strategies may be difficult to understand and evaluate for risk.
Related Terms: DeFi Primitives, Yield Stacking, Smart Contract
