Proof of Burn
Proof of Burn: Destroying Value for Consensus
Proof of Burn requires destroying cryptocurrency to participate in consensus or gain network benefits. It’s like burning money to prove you’re serious about network security.
Proof of Burn is a consensus mechanism where participants destroy cryptocurrency by sending it to unrecoverable addresses to gain mining rights or network privileges. The economic cost of burned tokens incentivizes honest behavior.
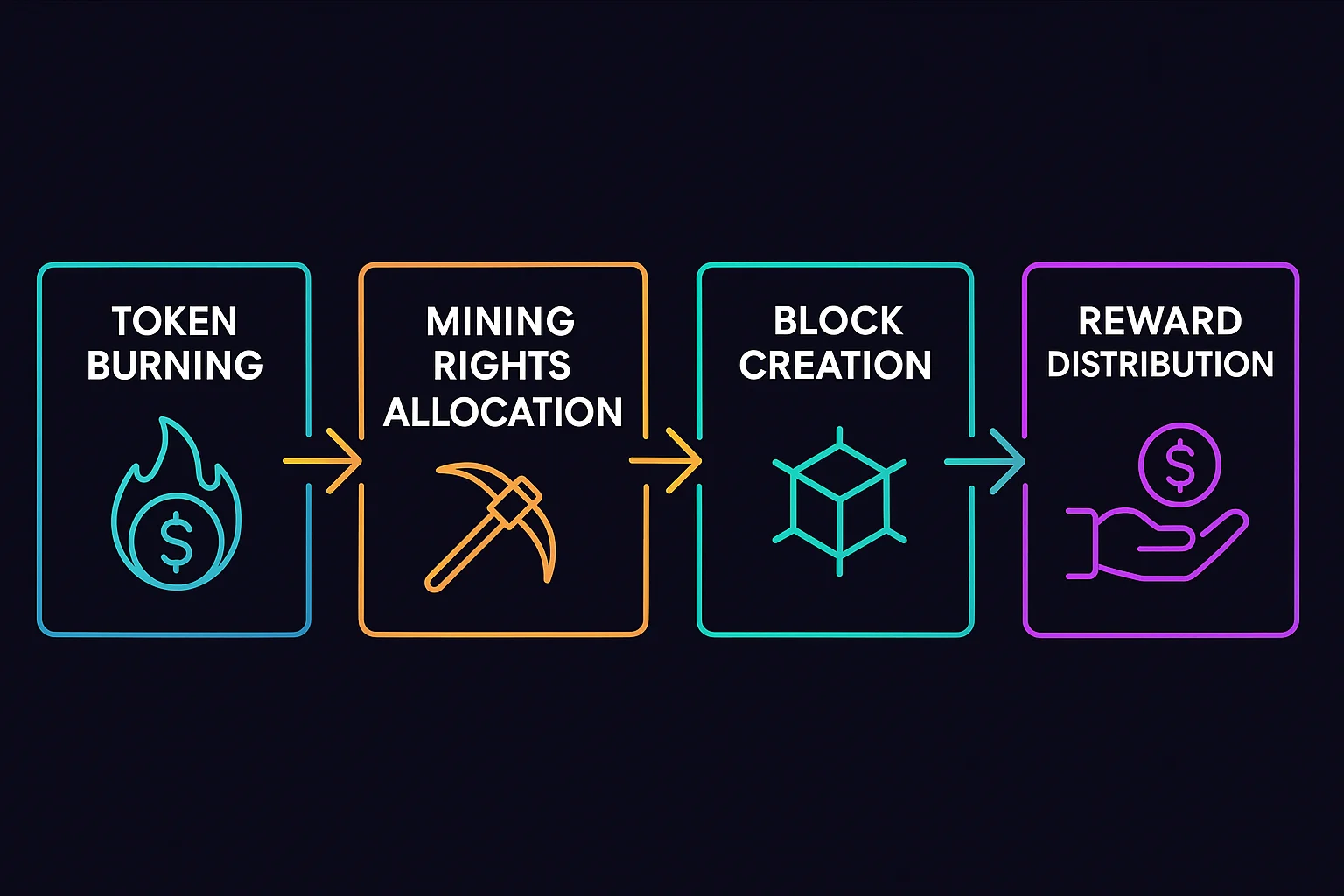
How Proof of Burn Works
Token destruction sends cryptocurrency to addresses with no known private keys, permanently removing it from circulation as proof of economic commitment.
Mining rights are awarded based on the value of recently burned tokens, with more burns providing higher chances of being selected to create blocks.
Economic incentives align participant interests with network security since dishonest behavior would waste the burned tokens without rewards.
Real-World Examples
- Counterparty used Bitcoin burning to distribute XCP tokens during its initial launch
- Slimcoin implements Proof of Burn as part of its hybrid consensus mechanism
- Various token launches have used burning mechanisms to create fair distribution
Why Beginners Should Care
Environmental efficiency compared to Proof of Work since burning doesn’t require ongoing energy consumption for mining operations.
Economic sustainability questions about whether participants will continue burning tokens when rewards don’t justify the costs.
Limited adoption as most networks prefer Proof of Stake or other alternatives that don’t require permanent value destruction.
Related Terms: Consensus Mechanism, Token Burn, Economic Security
