Liquidity Sniping
Liquidity Sniping: Front-Running New Pools
Liquidity sniping involves immediately buying tokens when new liquidity pools are created, often using bots to front-run regular users. It’s like cutting in line at the grand opening sale.
Liquidity sniping is the practice of using automated systems to immediately purchase tokens as soon as new liquidity pools go live, taking advantage of low initial prices before regular users can react. This often involves MEV extraction and front-running techniques.
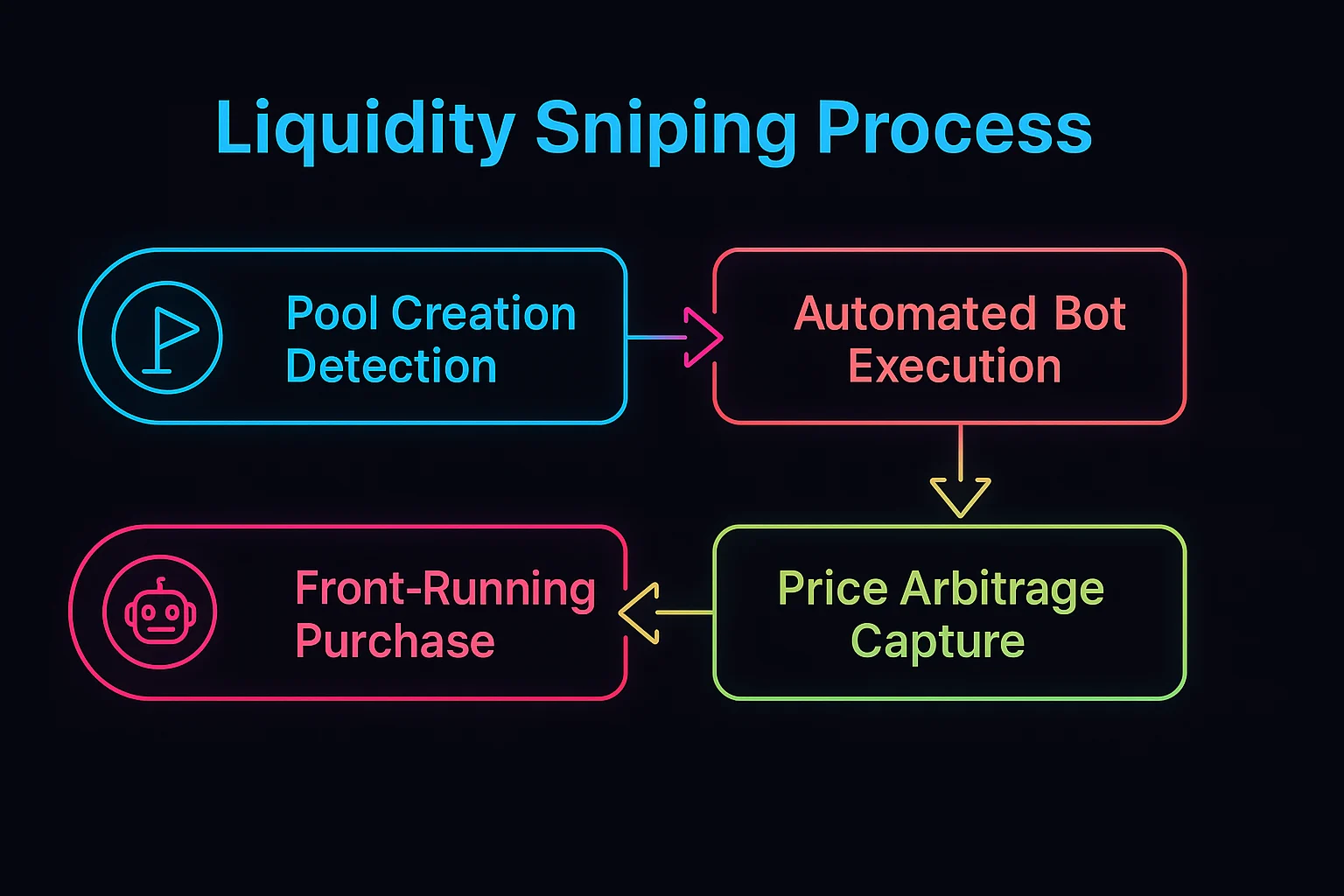
How Liquidity Sniping Works
Pool monitoring tracks new token launches and liquidity additions across decentralized exchanges to identify sniping opportunities.
Automated execution uses bots with high gas prices to ensure transactions get included immediately when new pools become active.
Price arbitrage captures value from initial price inefficiencies before markets reach equilibrium through normal trading activity.
Real-World Examples
- New token launches on Uniswap frequently face sniping bots that buy tokens within the same block
- Sandwich attacks during pool creation that manipulate prices for sniping profits
- MEV bot networks specialized in detecting and exploiting new liquidity opportunities
Why Beginners Should Care
Unfair advantages for sophisticated actors with automated systems over retail users trying to participate in new token launches.
Price impact from sniping can dramatically affect initial token prices and distribution fairness for legitimate users.
Protection strategies include using private mempools, delayed launches, or anti-MEV mechanisms to reduce sniping effectiveness.
Related Terms: MEV, Front-Running, Liquidity Pool, Bot Trading
