Metaverse
Metaverse: Digital Worlds Meet Real Money
The metaverse promises persistent digital worlds where your avatar’s clothes cost more than your real ones. It’s part virtual reality, part speculation, part genuine innovation.
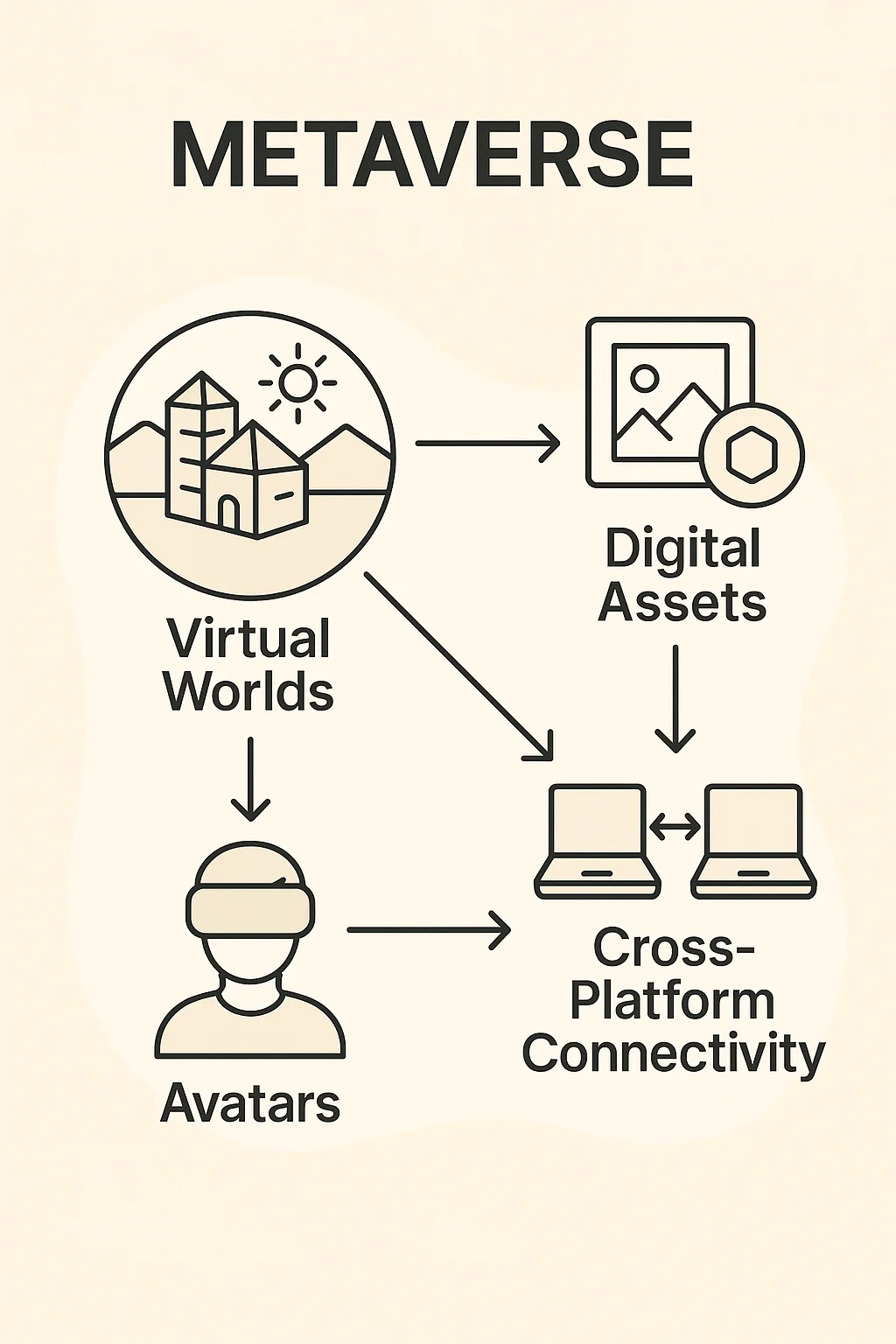
The metaverse refers to interconnected virtual worlds where users can work, play, socialize, and own digital assets through avatars and blockchain-based economies. Think Ready Player One, but with NFT sneakers and play-to-earn jobs.
How the Metaverse Works
Virtual real estate gets bought and sold as NFTs, with prime locations near popular areas commanding premium prices. Some virtual land parcels have sold for millions of dollars.
Digital economies use cryptocurrency for transactions, enabling real income from virtual activities like creating content, providing services, or trading digital goods.
Interoperability goals aim to let users move avatars, items, and identities between different virtual worlds, though technical and business challenges remain significant.
Real-World Examples
- Decentraland – Ethereum-based virtual world with user-owned land and experiences
- The Sandbox – Gaming-focused metaverse with creation tools and SAND token economy
- Horizon Worlds – Meta’s VR social platform (though not crypto-native)
Why Beginners Should Care
Metaverse investments are highly speculative. Virtual land and digital assets have no intrinsic value beyond what others will pay for them in these specific virtual environments.
Early adoption opportunities exist for creators who build audiences and businesses in virtual worlds before mainstream adoption arrives.
Technical limitations including VR hardware costs, internet bandwidth requirements, and user experience challenges still prevent mass adoption.
Related Terms: NFT, Virtual Real Estate, Play-to-Earn, Avatar
