Delegated Proof of Stake (DPoS)
Delegated Proof of Stake (DPoS): Democratic Validation
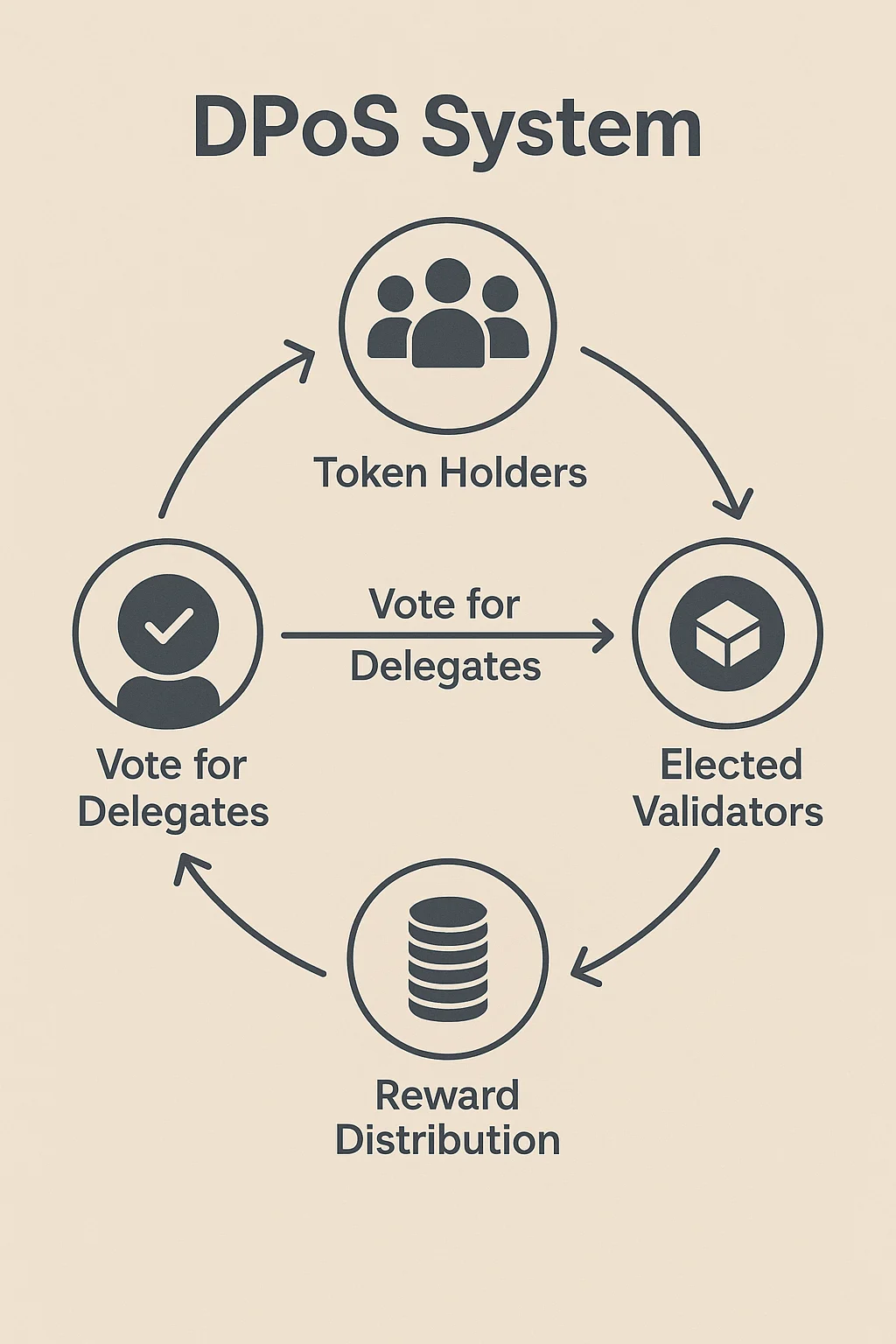
DPoS lets token holders vote for validators who secure the network on their behalf. It’s like electing representatives to Congress, but for blockchain consensus.
Delegated Proof of Stake (DPoS) is a consensus mechanism where token holders vote for a limited number of delegates who validate transactions and secure the network. This creates a more scalable system than pure Proof of Stake while maintaining democratic participation.
How DPoS Works
Voting power corresponds to token holdings, allowing larger stakeholders to have more influence over delegate selection while still enabling smaller holders to participate.
Fixed validator sets typically include 21-101 elected delegates who take turns producing blocks, creating faster consensus than systems with thousands of validators.
Continuous elections let token holders change their votes at any time, removing poorly performing delegates and encouraging good behavior through threat of replacement.
Real-World Examples
- EOS blockchain uses 21 elected block producers chosen by token holder voting
- Tron (TRX) employs 27 Super Representatives elected through continuous voting
- Lisk uses 101 delegates selected by stakeholder voting for network validation
Why Beginners Should Care
Faster transactions result from smaller validator sets that can reach consensus more quickly than systems requiring agreement from thousands of nodes.
Political dynamics emerge as delegates campaign for votes, form alliances, and compete for positions, sometimes leading to centralization concerns.
Voter apathy can concentrate power among a few large stakeholders if smaller token holders don’t actively participate in delegate selection.
Related Terms: Proof of Stake, Validator, Consensus Mechanism, Governance
