Ledger
Ledger: Hardware Wallet Security Leader
Ledger is a leading hardware wallet company that provides secure offline storage for cryptocurrency private keys. They’re like the Fort Knox of crypto storage devices.
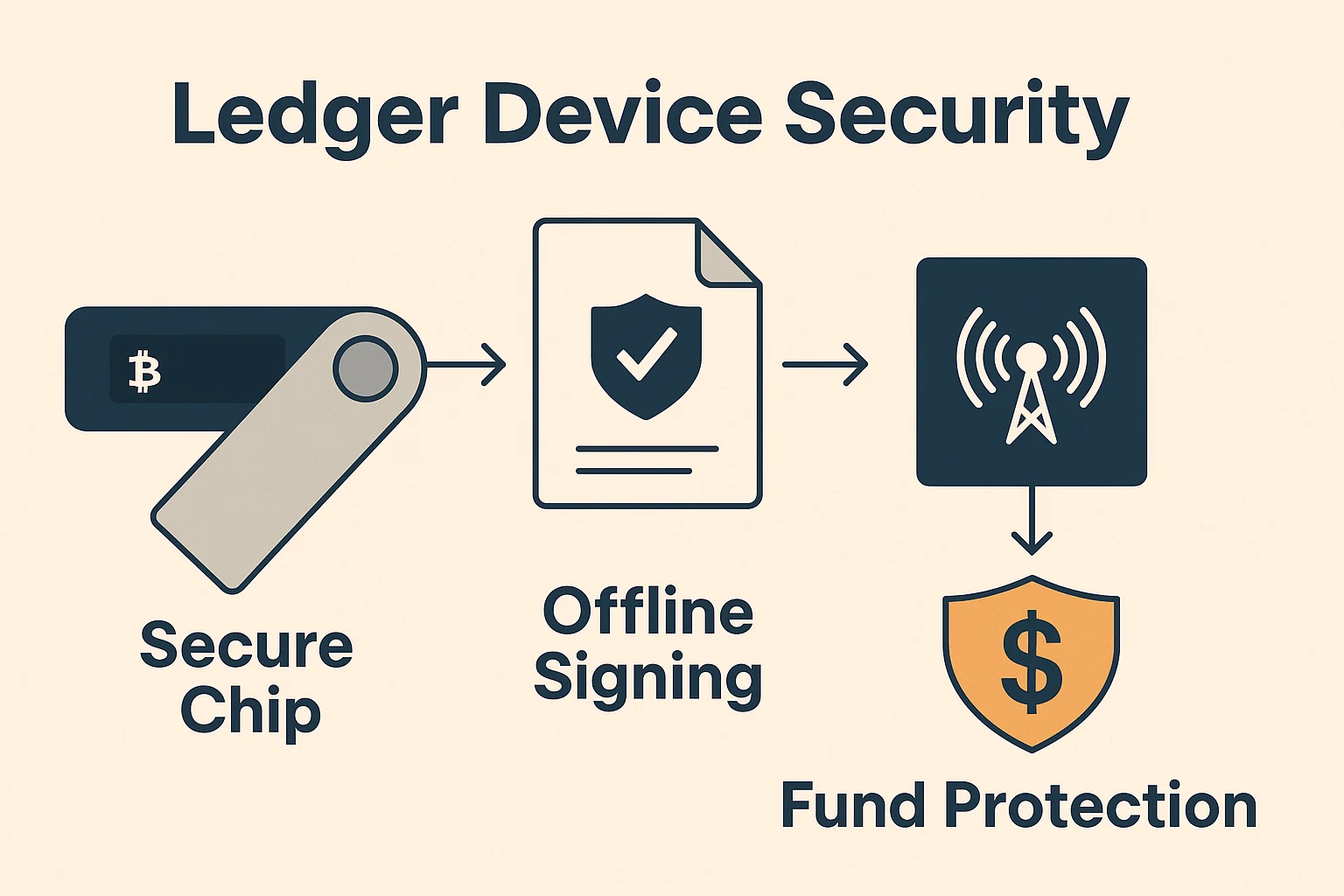
Ledger is a hardware wallet manufacturer that creates secure devices for storing cryptocurrency private keys offline, protecting them from online threats and hacking attempts. These devices enable secure transaction signing without exposing sensitive information.
How Ledger Devices Work
Secure element chips store private keys in tamper-resistant hardware that prevents extraction even with physical access to the device.
Offline transaction signing enables authorizing cryptocurrency transactions without connecting private keys to internet-connected computers.
Recovery mechanisms through seed phrases allow restoring wallet access if the hardware device is lost, stolen, or damaged.
Real-World Examples
- Ledger Nano S Plus provides affordable cold storage for multiple cryptocurrencies
- Ledger Nano X offers Bluetooth connectivity for mobile device integration
- Ledger Stax features advanced display and user interface capabilities
Why Beginners Should Care
Security enhancement over software wallets by keeping private keys offline and away from potential malware or hacking attempts.
Multi-currency support enables storing various cryptocurrencies on a single device with official wallet applications.
Industry reputation as Ledger devices are widely trusted by both beginners and institutional users for secure cryptocurrency storage.
Related Terms: Hardware Wallet, Cold Storage, Private Key, Secure Element
