Tornado Cash
Tornado Cash: The Controversial Privacy Protocol
Tornado Cash was Ethereum’s most popular mixing service until U.S. sanctions shut it down. It used zero-knowledge proofs to enable private transactions on a transparent blockchain.
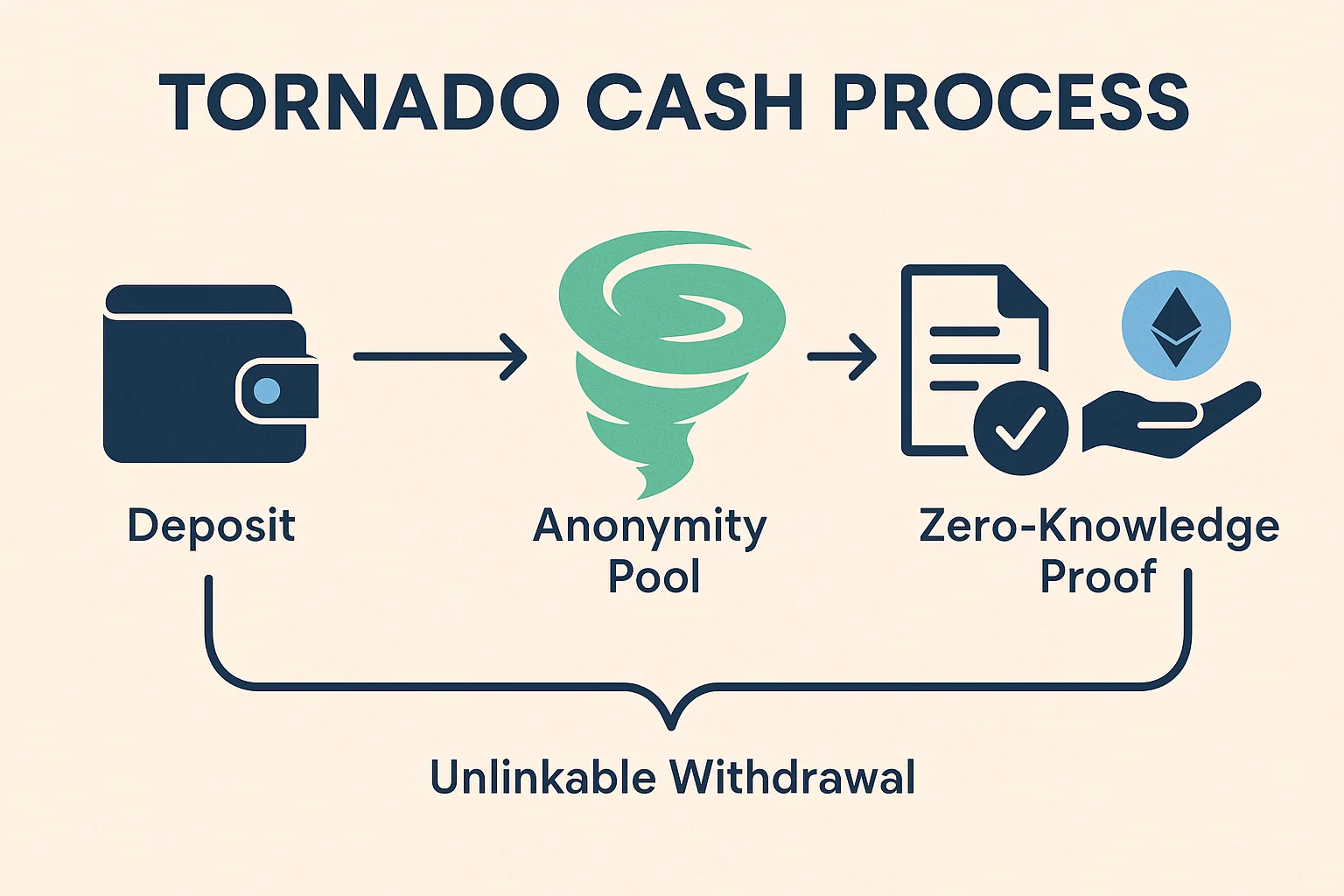
Tornado Cash was a decentralized mixing protocol on Ethereum that used zero-knowledge proofs to enable private transactions by breaking the link between sender and receiver addresses. Users could deposit ETH or tokens and later withdraw equivalent amounts from different addresses.
How Tornado Cash Worked
Smart contract pools held deposits of fixed amounts (0.1, 1, 10, or 100 ETH) where users could deposit funds and receive cryptographic commitments proving their deposit without revealing identity.
Zero-knowledge proofs allowed users to prove they had made a valid deposit without revealing which specific deposit was theirs, enabling private withdrawals to fresh addresses.
Anonymity sets grew larger with more users, improving privacy as it became harder to correlate deposits and withdrawals through timing or amount analysis.
Real-World Examples
- Privacy-conscious users mixed legitimate funds to prevent transaction surveillance and protect financial privacy
- Criminal activity also used the service, leading to regulatory scrutiny and eventual sanctions
- North Korean hackers reportedly used Tornado Cash to launder stolen cryptocurrency
Why Beginners Should Care
Regulatory precedent from Tornado Cash sanctions affects the entire crypto privacy space, potentially criminalizing privacy-enhancing technologies regardless of legitimate use cases.
Code vs. usage debates center on whether privacy tools themselves should be banned or only their illegal applications should be prosecuted.
Chilling effects on privacy development may result as developers avoid creating tools that could face similar regulatory action, reducing financial privacy options for law-abiding users.
Related Terms: Mixing Service, Zero-Knowledge Proof, Privacy Coin, Sanctions
