Privacy Coin
Privacy Coin: Digital Cash That Actually Hides
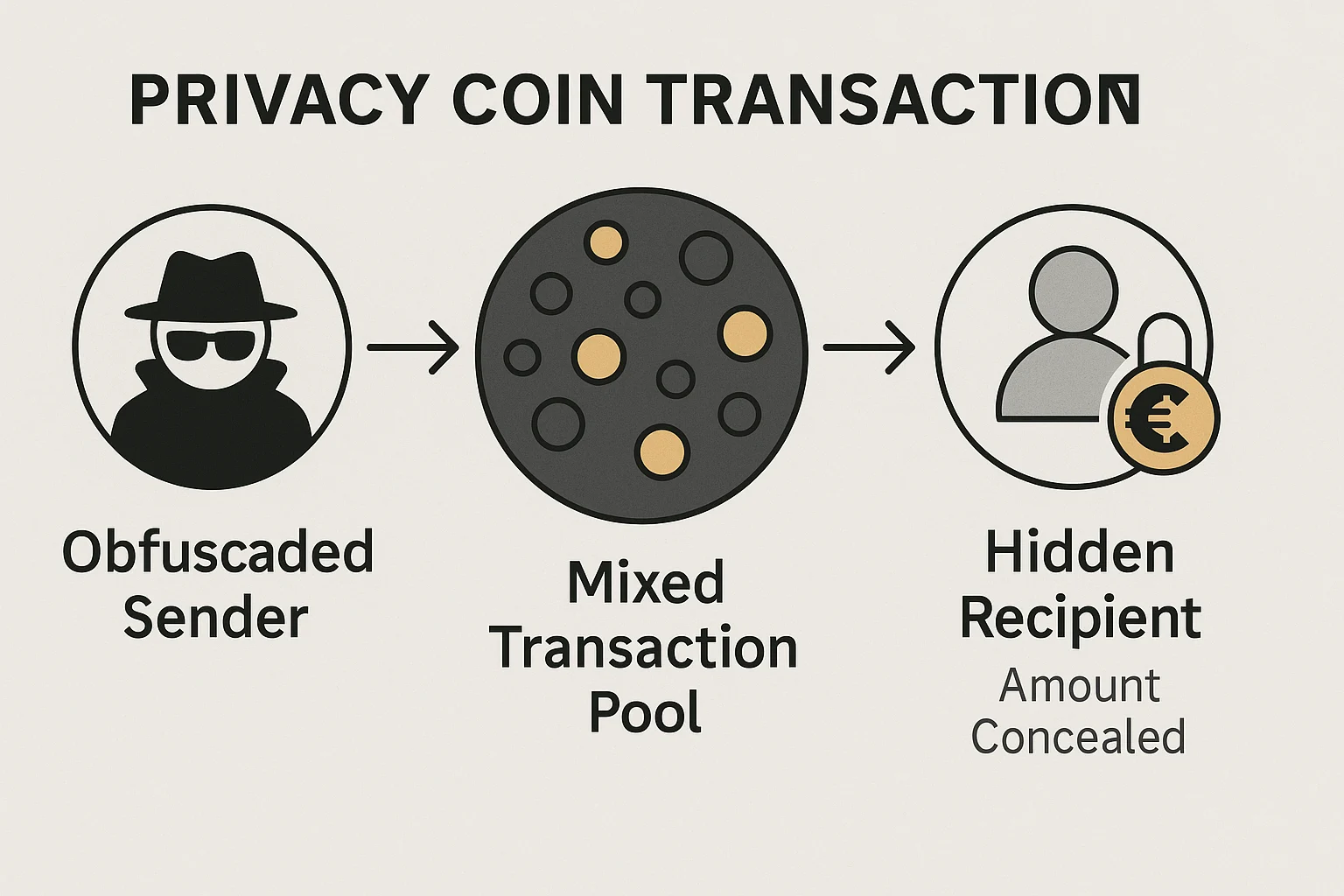
Privacy coins use advanced cryptography to hide transaction details like amounts, senders, and receivers. They’re what Bitcoin was supposed to be before everyone realized blockchain transactions are completely transparent.
Privacy coins are cryptocurrencies designed to provide anonymous or untraceable transactions through advanced cryptographic techniques. Unlike Bitcoin where all transactions are publicly visible, privacy coins obscure transaction details to protect user financial privacy.
How Privacy Coins Work
Ring signatures mix your transaction with others, making it impossible to determine which participant actually sent the funds. It’s like having multiple people sign a document with identical handwriting.
Stealth addresses generate unique one-time addresses for each transaction, preventing outside observers from linking multiple payments to the same recipient.
Zero-knowledge proofs verify transaction validity without revealing amounts, addresses, or other sensitive information to network validators or blockchain observers.
Real-World Examples
- Monero (XMR) – Uses ring signatures, stealth addresses, and RingCT for comprehensive privacy
- Zcash (ZEC) – Offers optional privacy through zero-knowledge proofs called zk-SNARKs
- Dash – Provides mixing services through CoinJoin-style transactions
Why Beginners Should Care
Financial privacy matters for legitimate reasons like preventing targeted theft, business confidentiality, and protection from authoritarian surveillance.
Regulatory pressure has forced many exchanges to delist privacy coins, limiting liquidity and adoption despite growing demand for financial privacy.
Enhanced security protects users from physical attacks since transaction histories can’t be used to identify wealthy targets for robbery or extortion.
Related Terms: Zero-Knowledge Proof, Ring Signatures, Stealth Address, Mixing Service
