Anti-Sybil Mechanism
Anti-Sybil Mechanism: Preventing Fake Identity Attacks
Anti-Sybil mechanisms prevent individuals from creating multiple fake identities to gain unfair advantages in voting, airdrops, or governance systems. They’re like requiring photo ID to prevent ballot stuffing.
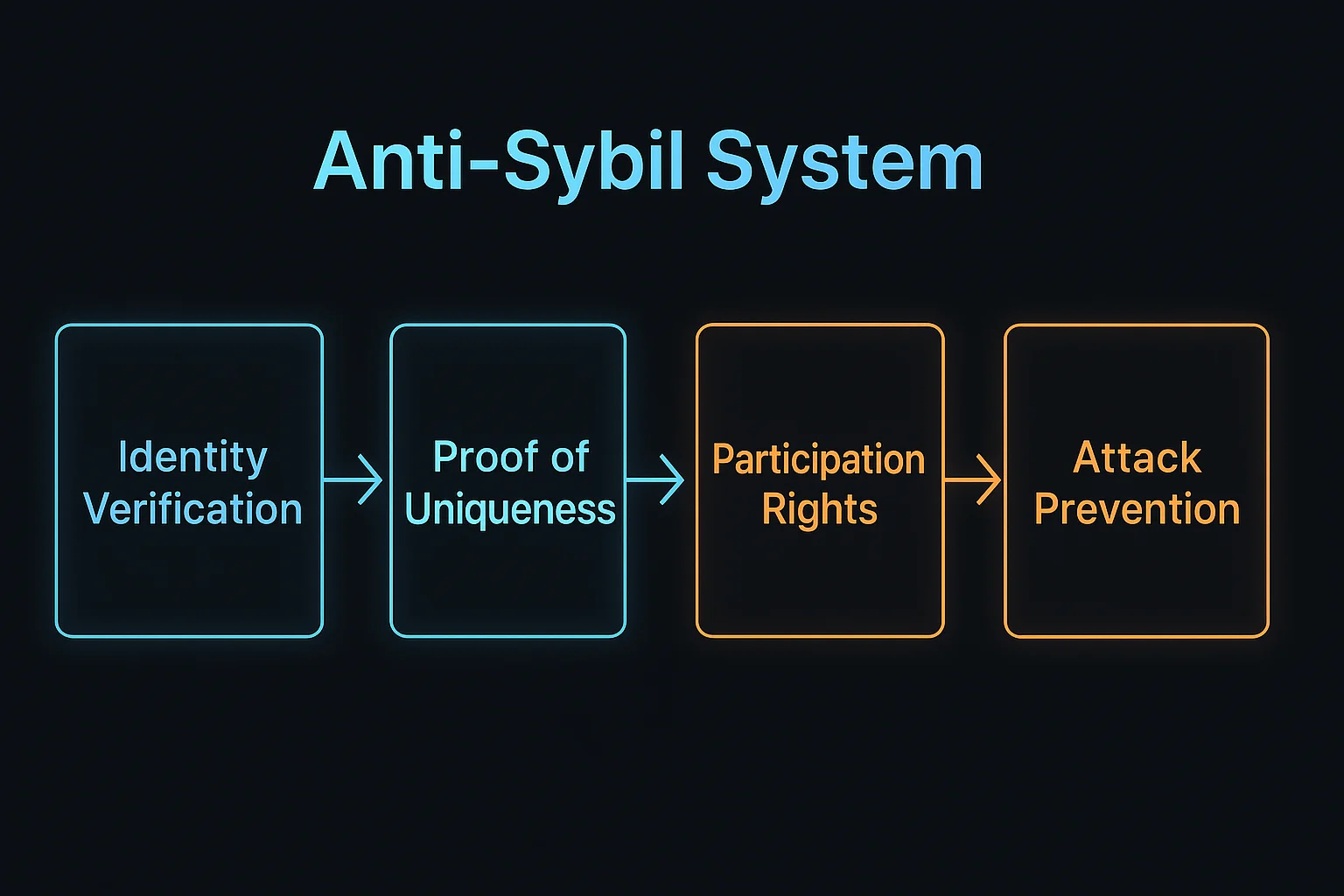
Anti-Sybil mechanisms are systems designed to prevent or detect when single entities create multiple fake identities to manipulate voting, governance, or reward distribution systems. These defenses ensure one person equals one vote or allocation.
How Anti-Sybil Mechanisms Work
Identity verification through various means like social graphs, proof of humanity protocols, or proof of unique human presence that’s difficult to fake.
Economic barriers require significant stake or cost to participate, making it expensive to create multiple identities for attacks.
Behavioral analysis identifies patterns suggesting coordinated fake accounts through timing, transaction history, or interaction patterns.
Real-World Examples
- Gitcoin Grants uses Gitcoin Passport to verify unique human participants in quadratic funding
- Proof of Humanity creates registries of verified unique humans for various applications
- BrightID provides decentralized identity verification through social graph analysis
Why Beginners Should Care
Fair distribution depends on anti-Sybil measures to prevent wealthy actors from claiming multiple shares of airdrops or governance power.
Privacy trade-offs as effective anti-Sybil systems often require revealing personal information or social connections.
System integrity for democratic governance and fair resource allocation across crypto protocols and DAOs.
Related Terms: Sybil Attack, Quadratic Funding, Governance
