Cross-Chain Messaging
Cross-Chain Messaging: Inter-Blockchain Communication
Cross-chain messaging enables smart contracts on different blockchains to communicate and trigger actions across networks. It’s like having a universal translator for blockchain conversations.
Cross-chain messaging allows smart contracts on different blockchain networks to send data, trigger functions, and coordinate actions across multiple chains. This enables true interoperability beyond simple asset transfers.
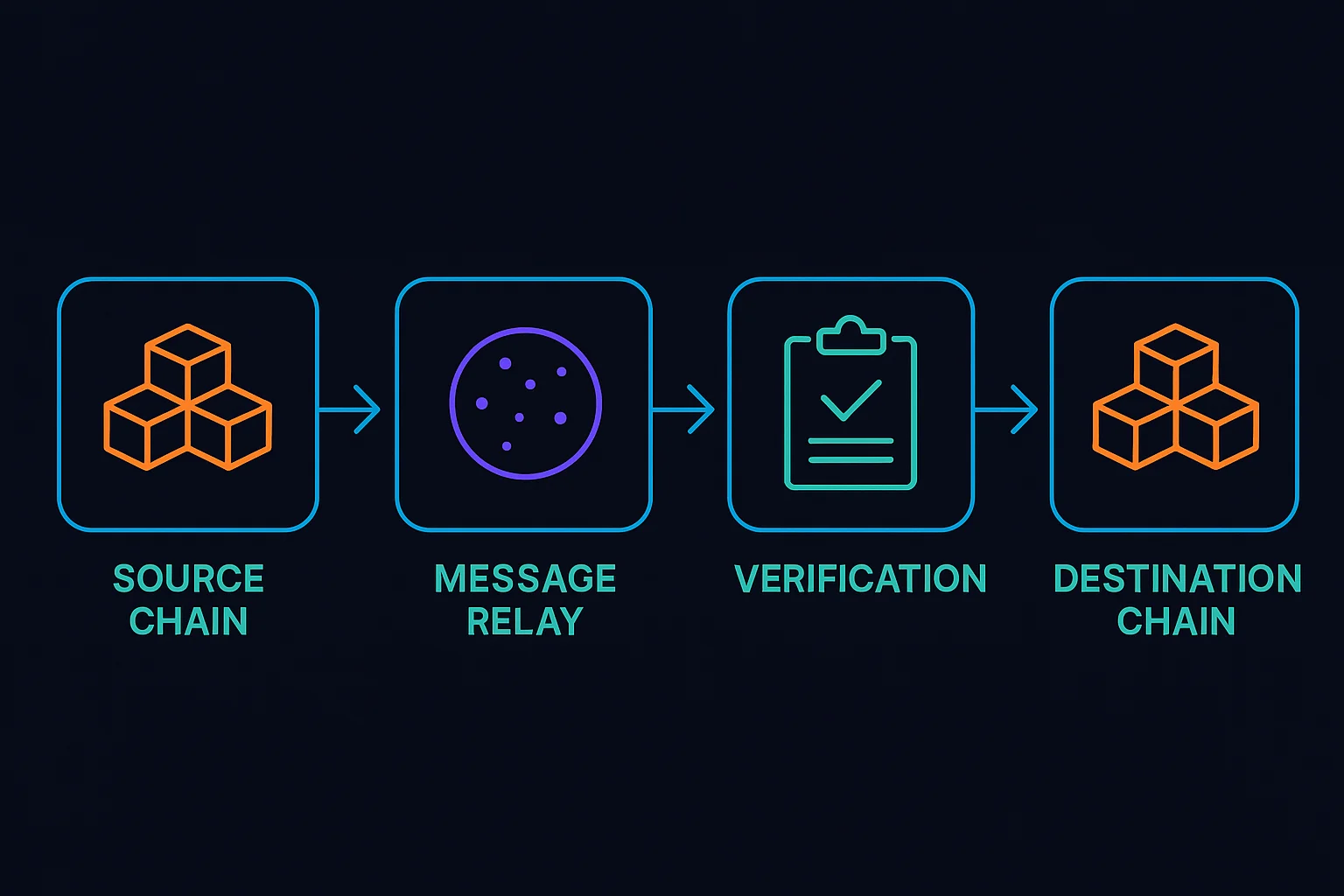
How Cross-Chain Messaging Works
Message protocols standardize how different blockchains can communicate, including data formats, verification methods, and delivery confirmation.
Relay networks transport messages between chains through validators, oracles, or specialized infrastructure that monitors multiple networks.
Verification systems ensure message authenticity and prevent manipulation through cryptographic proofs, multi-signature schemes, or consensus mechanisms.
Real-World Examples
- LayerZero enables omnichain applications through standardized messaging protocols
- Axelar provides secure cross-chain communication with proof-of-stake validation
- IBC (Inter-Blockchain Communication) connects Cosmos ecosystem chains natively
Why Beginners Should Care
Unified experiences enable applications that work seamlessly across multiple blockchains without users managing complex multi-chain interactions.
Expanded possibilities for developers to build applications that leverage the best features of different blockchain networks simultaneously.
Security dependencies on cross-chain infrastructure that could become single points of failure for multi-chain applications.
Related Terms: Interoperability, Cross-Chain Protocol, Omnichain, Message Relay
