Liquid Restaking
Liquid Restaking: Flexible High-Yield Staking
Liquid restaking combines the capital efficiency of liquid staking with additional yield from securing multiple networks. It’s like having your cake and eating it too, but with slashing risks.
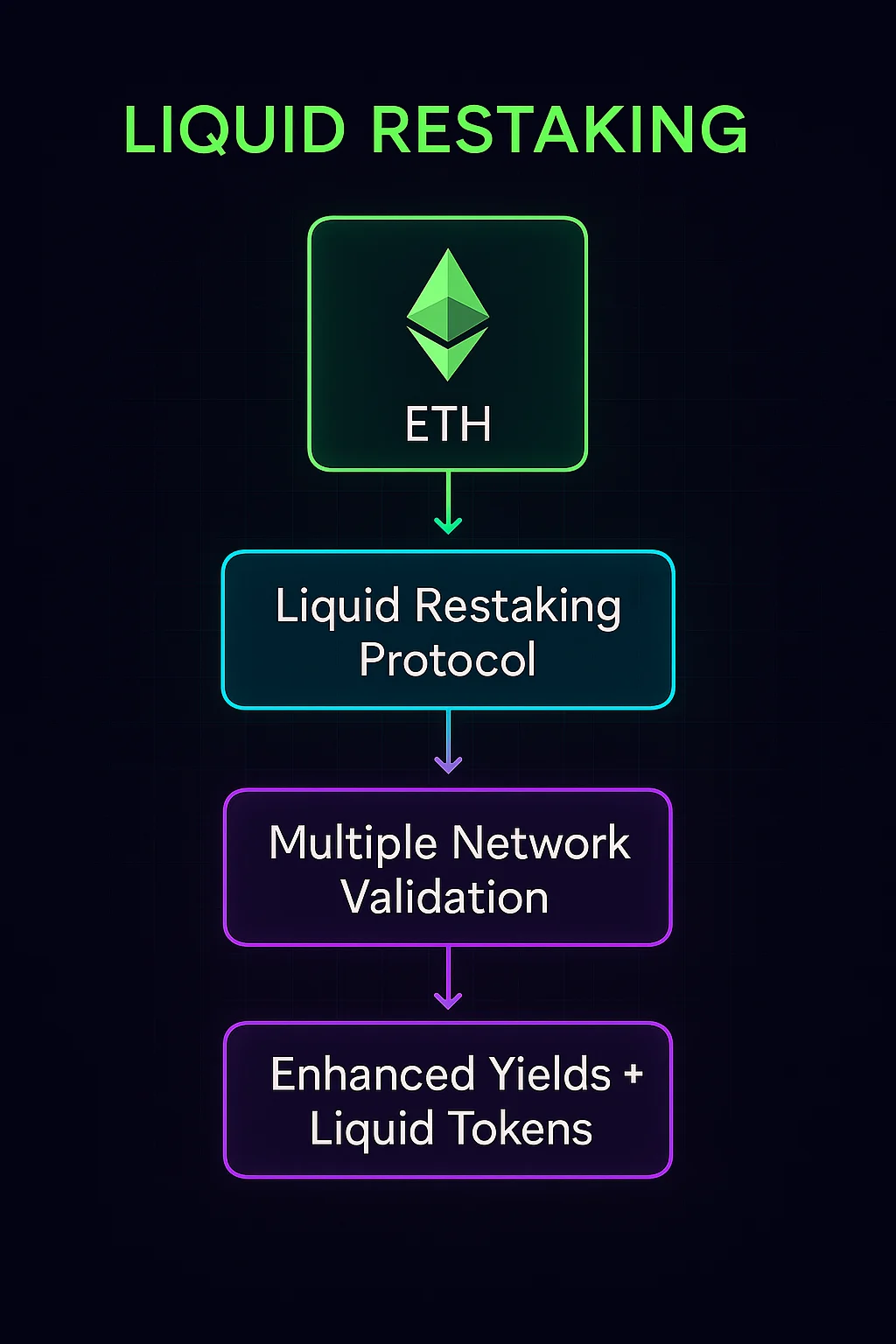
Liquid restaking allows staked assets to secure additional protocols while remaining liquid through tokenized representations. Users can earn enhanced yields from multiple sources while maintaining the ability to trade or use their staked positions.
How Liquid Restaking Works
Multiple validation enables staked assets to simultaneously secure the base layer and additional protocols or middleware services.
Liquid tokens represent restaked positions, allowing users to trade or use their staked assets in DeFi while earning enhanced rewards.
Operator delegation lets users choose professional operators to handle the technical complexity of running multiple validation services.
Real-World Examples
- EigenLayer enables ETH restaking for additional protocol security and yields
- Liquid restaking protocols build on EigenLayer to provide tokenized restaking positions
- Professional operators manage restaking infrastructure for delegated stake
Why Beginners Should Care
Enhanced yields from multiple revenue sources can significantly outperform traditional single-protocol staking returns.
Increased complexity and slashing risks from multiple protocols make liquid restaking suitable for more sophisticated users willing to accept additional risks.
Capital efficiency maximizes the productive use of staked assets rather than having them earn only base layer rewards.
Related Terms: Restaking, Liquid Staking, EigenLayer, Slashing
