Proof of History
Proof of History: Solana’s Time Innovation
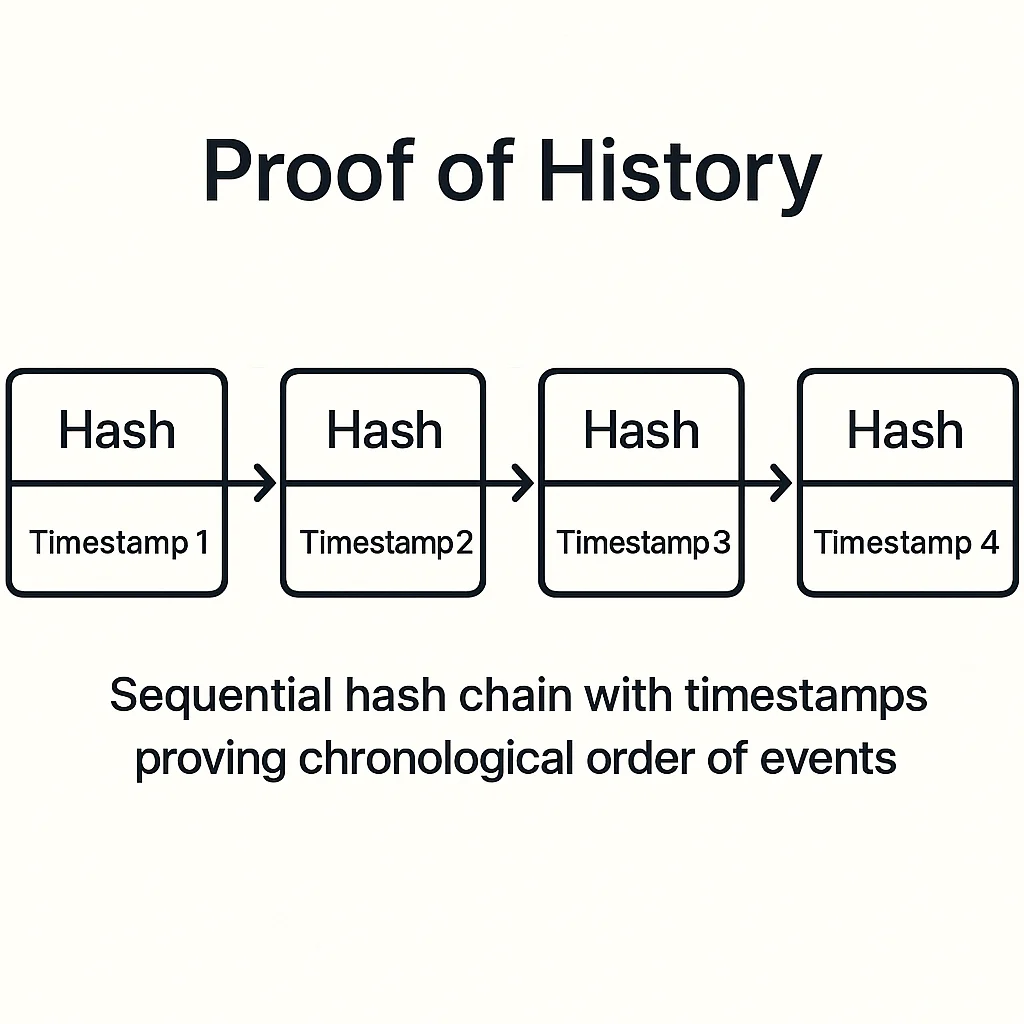
Proof of History creates a cryptographic timestamp that proves events occurred in a specific sequence. It’s like having an unforgeable clock built into the blockchain.
Proof of History (PoH) is a consensus mechanism that creates a historical record proving that events occurred at specific moments in time. It uses cryptographic functions to generate verifiable timestamps without relying on external time sources.
How Proof of History Works
Sequential hashing creates a chain of cryptographic proofs that demonstrate the passage of time. Each hash includes the previous hash, creating an unbreakable chronological sequence.
Verifiable delay functions ensure the time sequence cannot be generated faster than real time, preventing validators from creating fake historical records.
Parallel processing becomes possible when all nodes agree on the timing of events, enabling higher throughput than traditional consensus mechanisms.
Real-World Examples
- Solana blockchain uses PoH as its primary innovation for achieving high transaction throughput
- Validator synchronization relies on PoH timestamps to coordinate network operations
- Transaction ordering uses PoH to eliminate disputes about event sequence
Why Beginners Should Care
Speed advantages from PoH enable Solana to process thousands of transactions per second with low fees, making it competitive with traditional payment systems.
Centralization concerns arise since PoH requires powerful hardware and reliable network connections, potentially limiting validator participation.
Novel approach makes PoH unproven at scale compared to battle-tested consensus mechanisms like Proof of Work or Proof of Stake.
Related Terms: Consensus Mechanism, Solana, Validator, Throughput
