Liquidation Bot
Liquidation Bot: Automated Debt Collection
Liquidation bots monitor lending protocols for undercollateralized positions and automatically liquidate them for profit. They’re like repo men but for DeFi loans.
A liquidation bot is an automated program that monitors DeFi lending protocols for loans that fall below required collateral ratios and triggers liquidations to earn rewards. These bots help maintain protocol solvency while capturing liquidation bonuses.
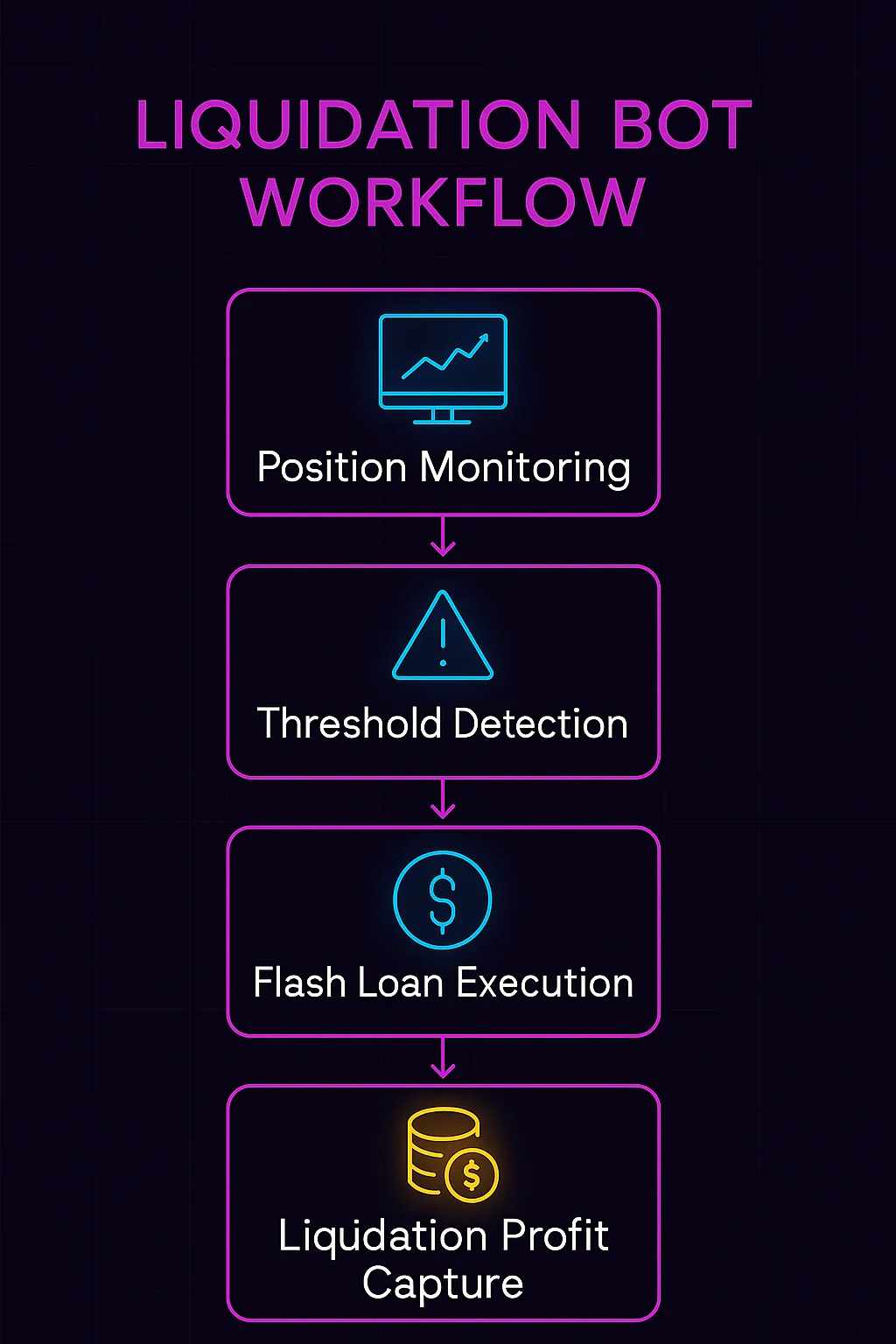
How Liquidation Bots Work
Continuous monitoring tracks collateral ratios across lending platforms, identifying positions approaching liquidation thresholds as asset prices fluctuate.
Flash loan capital enables bots to liquidate large positions without holding significant capital upfront, borrowing funds for liquidation then repaying from proceeds.
Gas competition involves bots bidding higher gas prices to ensure their liquidation transactions get processed first when multiple bots target the same position.
Real-World Examples
- Compound liquidations during market crashes can generate millions in bot profits as leveraged positions get liquidated en masse
- Aave liquidation bonuses typically range from 5-15% of liquidated collateral value
- MakerDAO liquidations use auction mechanisms that bots participate in to acquire discounted collateral
Why Beginners Should Care
Market efficiency from liquidation bots helps maintain lending protocol solvency by quickly removing bad debt before it becomes unrecoverable.
Borrower risks increase during volatile markets when liquidation bots aggressively target positions near liquidation thresholds.
Technical barriers make running competitive liquidation bots challenging for individuals due to infrastructure and capital requirements.
Related Terms: Liquidation, Flash Loan, Collateral Ratio, DeFi Lending
