Two-Factor Authentication (2FA)
Two-Factor Authentication (2FA): Your Crypto’s Second Lock
2FA is the minimum security standard for any crypto account worth protecting. If you’re not using it, you’re basically leaving your front door unlocked.
Two-factor authentication (2FA) requires two different verification methods to access your account – typically something you know (password) plus something you have (phone or hardware token). It dramatically reduces the risk of account takeovers even if your password is compromised.
How 2FA Works
SMS 2FA sends codes to your phone, but this method is vulnerable to SIM swapping attacks where scammers take control of your phone number.
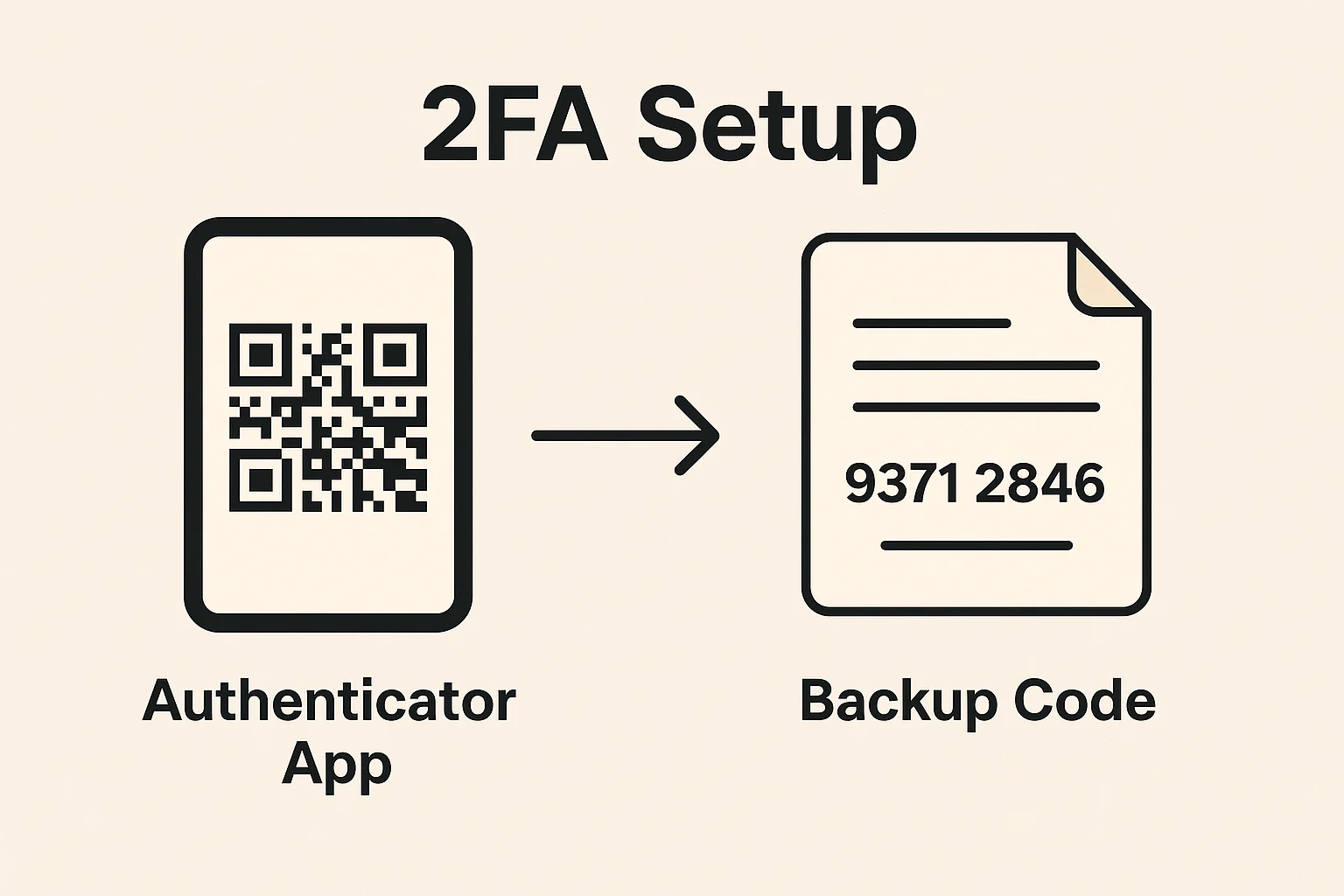
Authenticator apps like Google Authenticator or Authy generate time-based codes that change every 30 seconds. These are much more secure than SMS since they don’t rely on phone networks.
Hardware tokens like YubiKey provide the highest security by requiring physical possession of the device to generate authentication codes.
Real-World Examples
- Exchange accounts – Kraken, Coinbase, and Binance all support multiple 2FA methods
- Wallet apps – MetaMask and other wallets offer 2FA for additional protection
- DeFi platforms – Some protocols now support 2FA for administrative functions
Why Beginners Should Care
Password breaches happen constantly. If your exchange password gets leaked and you don’t have 2FA enabled, scammers can drain your account in minutes.
Use authenticator apps instead of SMS whenever possible. For high-value accounts, consider hardware keys like YubiKey for maximum security.
Always save your 2FA backup codes in a secure location – if you lose your phone without backups, you could be permanently locked out of your accounts.
Related Terms: Phishing Attack, Hardware Wallet, Exchange, Security
