Impermanent Loss
Impermanent Loss: The Hidden Cost of Liquidity Providing
Impermanent loss is the sneaky tax on liquidity providers. Your tokens can lose value even when the pool is profitable. It’s math, not magic – but it feels like getting robbed.
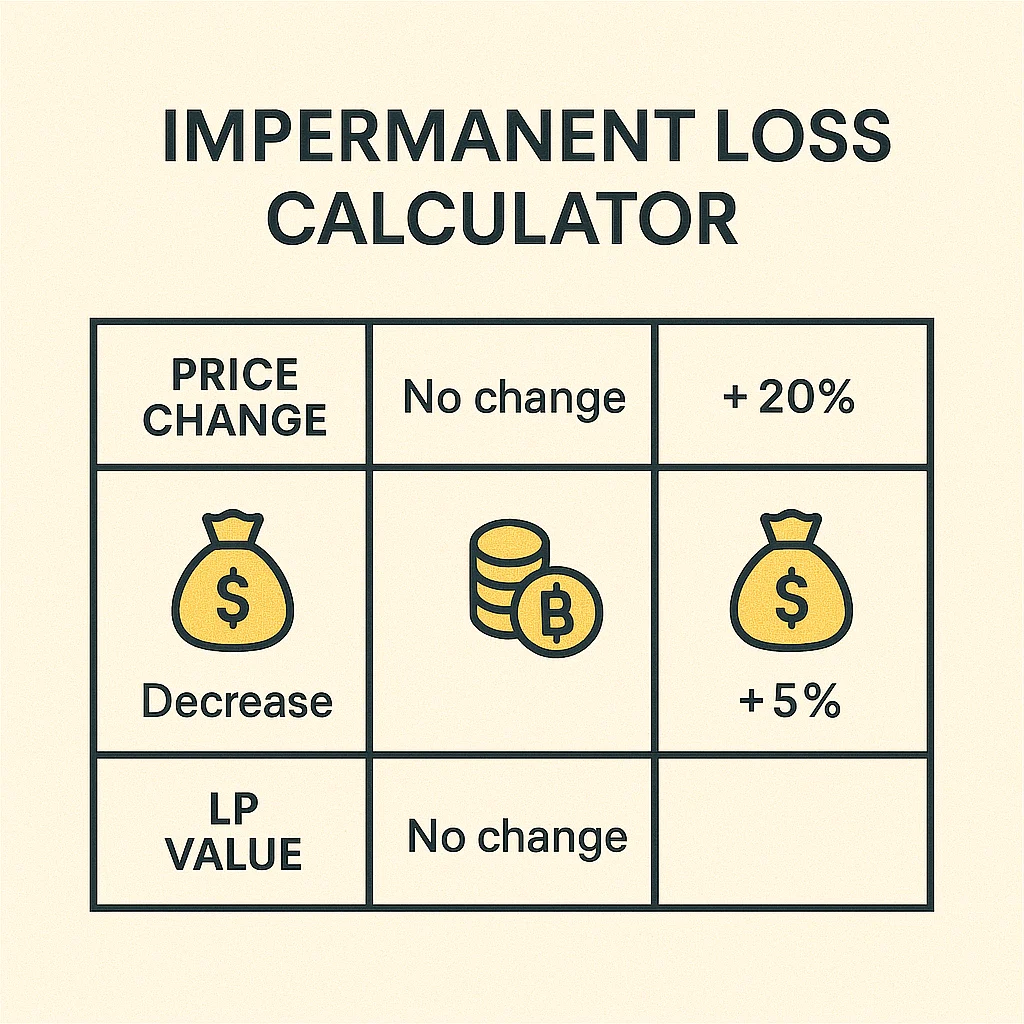
Impermanent loss occurs when the price ratio of tokens in a liquidity pool changes compared to when you deposited them. You end up with less value than if you had simply held the tokens separately, even though you earned trading fees.
How Impermanent Loss Works
Automated Market Makers maintain token ratios through arbitrage. When one token’s price increases, arbitrageurs buy it from the pool until the price matches external markets.
You’re selling winners and buying losers automatically. If ETH pumps 50% against USDC, the pool sells your ETH for USDC to maintain balance, giving you less ETH than you started with.
The loss is “impermanent” because if prices return to original ratios, the loss disappears. But if price divergence persists, the loss becomes very real.
Real-World Examples
- ETH/USDC pool during ETH bull run – you miss some ETH gains but earn trading fees
- Stablecoin pools have minimal impermanent loss but lower fee returns
- Volatile pairs can create severe impermanent loss that exceeds fee earnings
Why Beginners Should Care
Many new DeFi users discover impermanent loss after the fact, wondering why their “profitable” liquidity position lost money compared to holding tokens.
Calculate the trade-off before providing liquidity. High-fee pools might compensate for impermanent loss, while low-fee pools might not justify the risk.
Stablecoin pairs minimize impermanent loss risk while still earning yield from trading fees and liquidity mining rewards.
Related Terms: Liquidity Pool, Yield Farming, AMM, DEX
