Ring Signatures
Ring Signatures: Anonymous Signatures in Groups
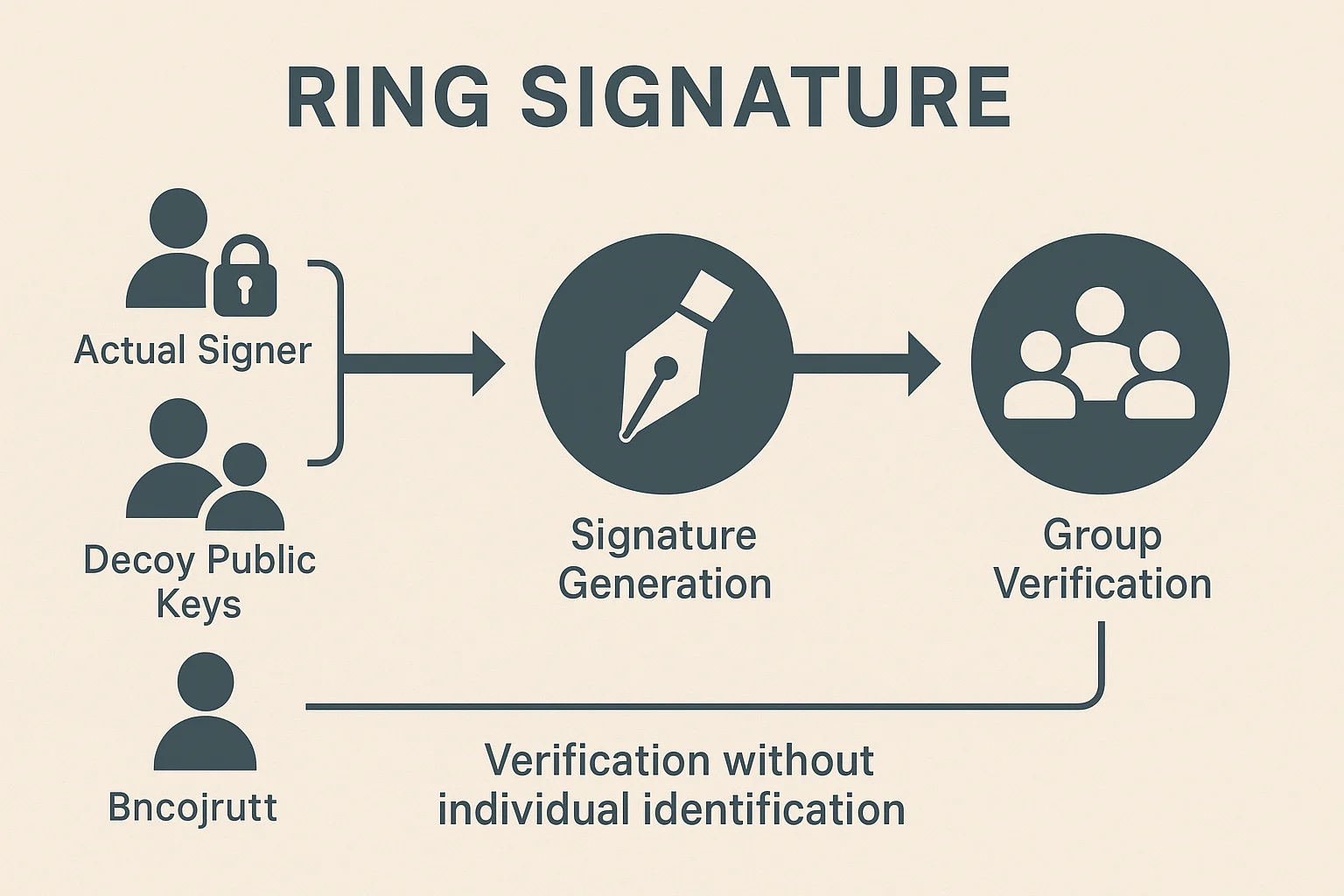
Ring signatures let any member of a group sign a message without revealing which specific member created the signature. It’s like having a family photo where you know someone took it, but can’t tell who.
A ring signature is a cryptographic signature scheme where any member of a group can produce a signature that verifies as coming from the group, but observers cannot determine which specific member signed. It provides anonymity within known sets.
How Ring Signatures Work
Group formation includes the actual signer plus other group members (called “decoys”) whose public keys are used to create the signature without their permission or knowledge.
Mathematical mixing combines the signer’s private key with decoys’ public keys in a way that produces a valid signature that could have been created by any group member.
Verification process confirms the signature came from someone in the group but provides no information about which specific member created it.
Real-World Examples
- Monero transactions use ring signatures to hide which outputs are being spent in each transaction
- Cryptonote protocol family implements ring signatures for privacy-focused cryptocurrencies
- Political dissidents could use ring signatures for anonymous group statements without revealing individual identities
Why Beginners Should Care
Financial privacy benefits from ring signatures by making it impossible to determine which specific wallet outputs were spent in transactions.
Plausible deniability exists since any group member could have created the signature, protecting individual privacy even if group membership is known.
Computational overhead makes ring signatures more expensive than regular signatures, requiring balance between privacy levels and transaction costs.
Related Terms: Privacy Coin, Monero, Mixing, Anonymity Set
