Rollups
Rollups: Scaling Through Bundling
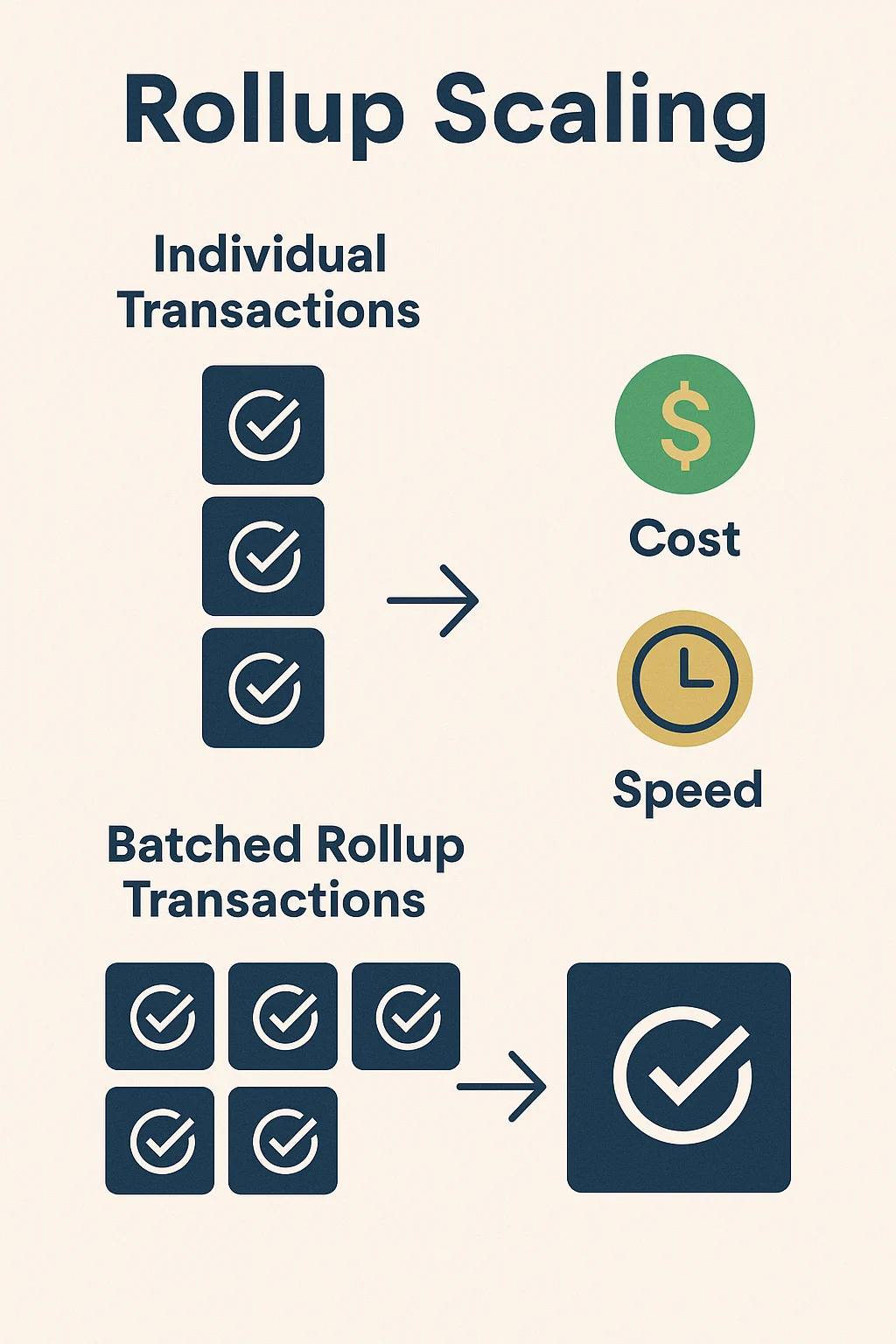
Rollups process hundreds of transactions off-chain then bundle the results into single on-chain transactions. It’s like carpooling for blockchain transactions – everyone shares the gas costs.
Rollups are Layer 2 scaling solutions that execute transactions off the main blockchain but post transaction data on-chain for security. They inherit the security of the main chain while dramatically reducing costs and increasing throughput.
How Rollups Work
Batch processing combines hundreds of transactions into cryptographic proofs or compressed data that gets submitted to the main chain as a single transaction.
Two main types exist: Optimistic rollups assume transactions are valid unless challenged, while Zero-Knowledge rollups use cryptographic proofs to guarantee validity.
Data availability ensures anyone can reconstruct rollup state from main chain data, maintaining decentralization and enabling independent verification of rollup operators.
Real-World Examples
- Arbitrum – Popular optimistic rollup with major DeFi protocols and lower fees
- Optimism – Ethereum scaling solution with retroactive public goods funding
- StarkNet – Zero-knowledge rollup using STARK proofs for scalability
Why Beginners Should Care
Massive fee savings make DeFi accessible to smaller users who were priced out by high Ethereum mainnet transaction costs during peak usage.
Security inheritance from Ethereum mainnet provides stronger guarantees than sidechains or independent Layer 1 blockchains with smaller validator sets.
Growing ecosystem sees major protocols launching on rollups, making them increasingly necessary for accessing the latest DeFi innovations and competitive yields.
Related Terms: Layer 2, Optimistic Rollup, zk-Rollup, Scaling
