Decentralized Identity (DID)
Decentralized Identity (DID): Self-Sovereign Digital Identity
DIDs give users control over their digital identity without relying on centralized authorities like governments or tech companies. It’s like having a passport that you issue and control yourself.
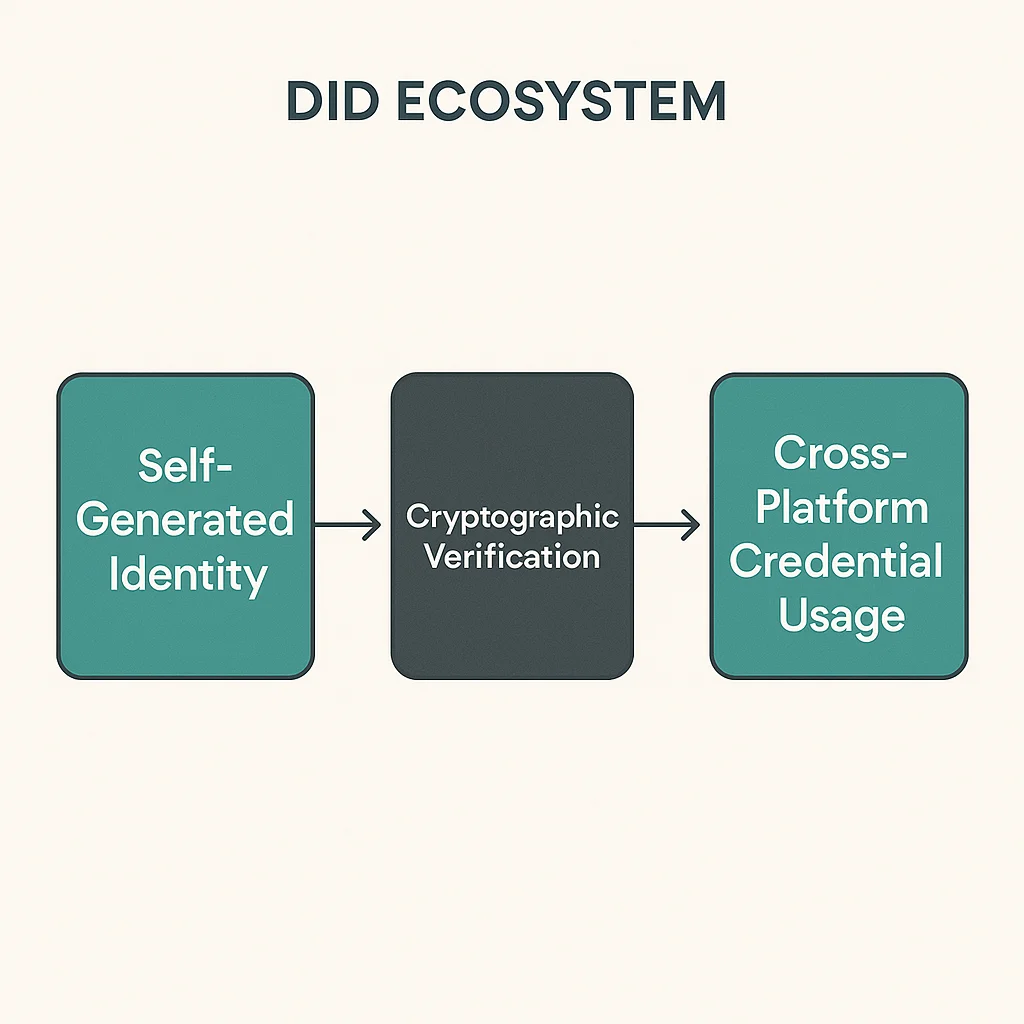
Decentralized Identity (DID) is a digital identity framework that gives individuals control over their personal data and identity verification without central authorities. Users can prove who they are and what credentials they hold without depending on third-party identity providers.
How DIDs Work
Self-sovereign control means users generate and manage their own identity credentials rather than relying on institutions to vouch for their identity.
Cryptographic verification enables proving identity ownership through digital signatures without revealing underlying personal information.
Interoperability standards allow DID credentials to work across different platforms and services that support the decentralized identity framework.
Real-World Examples
- ENS domains provide basic decentralized identity through blockchain-based naming
- Ceramic Network enables composable identity and reputation across Web3 applications
- Microsoft ION builds enterprise DID solutions on Bitcoin’s blockchain
Why Beginners Should Care
Privacy control over personal data sharing, allowing selective disclosure of only necessary information for specific use cases.
Reduced platform dependence eliminates risks of losing digital identity when centralized platforms ban accounts or shut down.
Credential portability enables taking verified achievements, reputation, and identity across different platforms and services.
Related Terms: Self-Sovereign Identity, ENS, Verifiable Credentials, Web3
