Wallet Signature Spoofing
Wallet Signature Spoofing: Fake Authorization Attacks
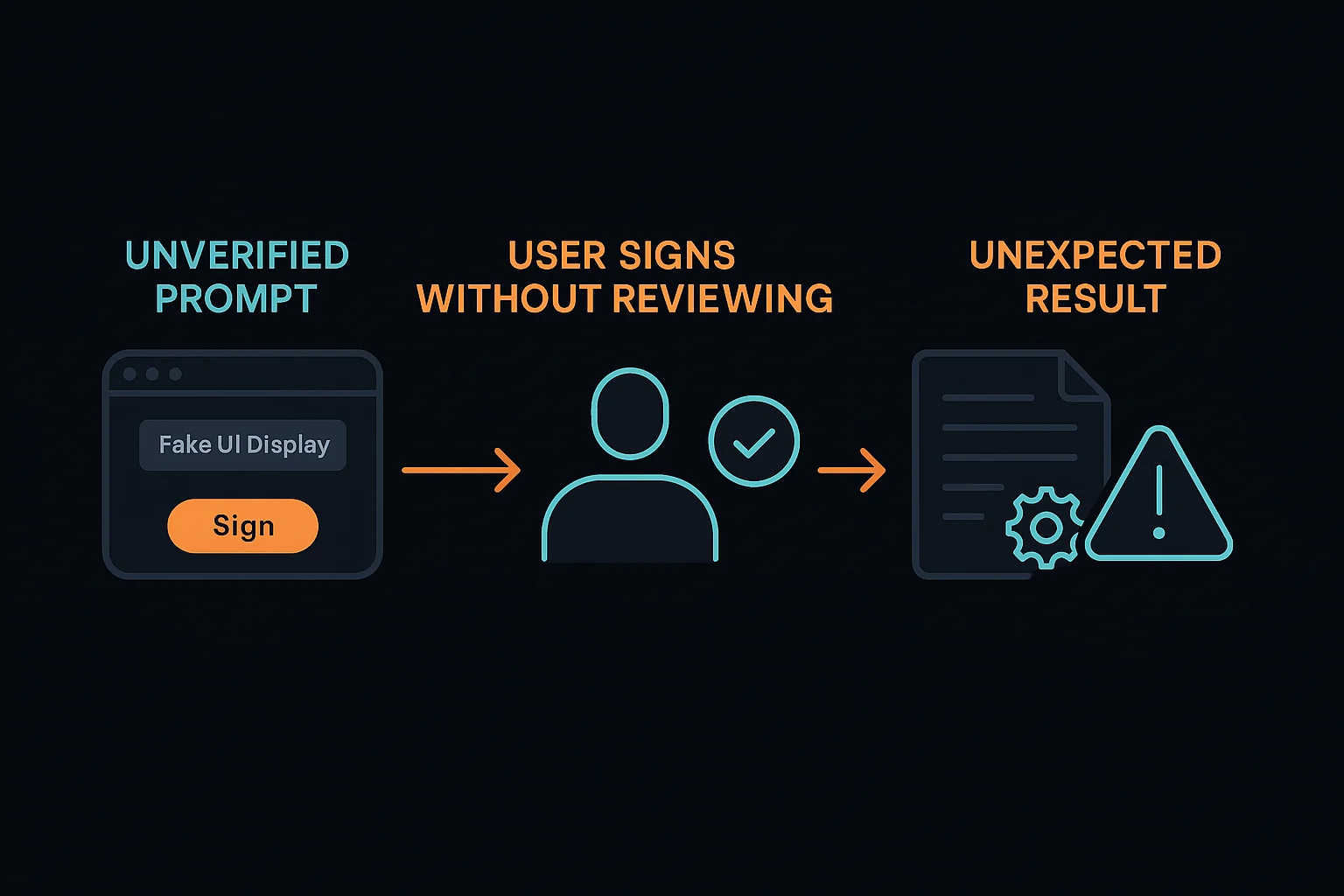
Wallet signature spoofing tricks users into signing malicious transactions that appear legitimate but actually authorize harmful actions. It’s like signing a contract where the fine print changes after you sign.
Wallet signature spoofing involves presenting misleading information about transaction contents to trick users into signing authorizations for unintended actions. Attackers exploit user interface vulnerabilities or social engineering to gain unauthorized access.
How Signature Spoofing Works
UI manipulation displays fake transaction details while the actual signature authorizes completely different actions than what users believe they’re approving.
Contract switching presents legitimate contracts for inspection but substitutes malicious contracts at signature time before users can detect the change.
Social engineering combines technical deception with psychological manipulation to pressure users into quickly signing without careful verification.
Real-World Examples
- Fake NFT marketplace signatures that actually approve unlimited token spending
- Phishing websites that spoof popular DeFi protocols to steal user authorizations
- Malicious browser extensions that modify transaction data after users review but before signing
Why Beginners Should Care
Verification importance requires carefully checking all transaction details, contract addresses, and permissions before signing any wallet transactions.
Hardware wallet benefits provide additional verification steps that make signature spoofing attacks more difficult to execute successfully.
Recovery challenges since spoofed signatures can grant extensive permissions that enable ongoing fund theft until manually revoked.
Related Terms: Phishing Attack, Transaction Verification, Hardware Wallet
