Node Operator
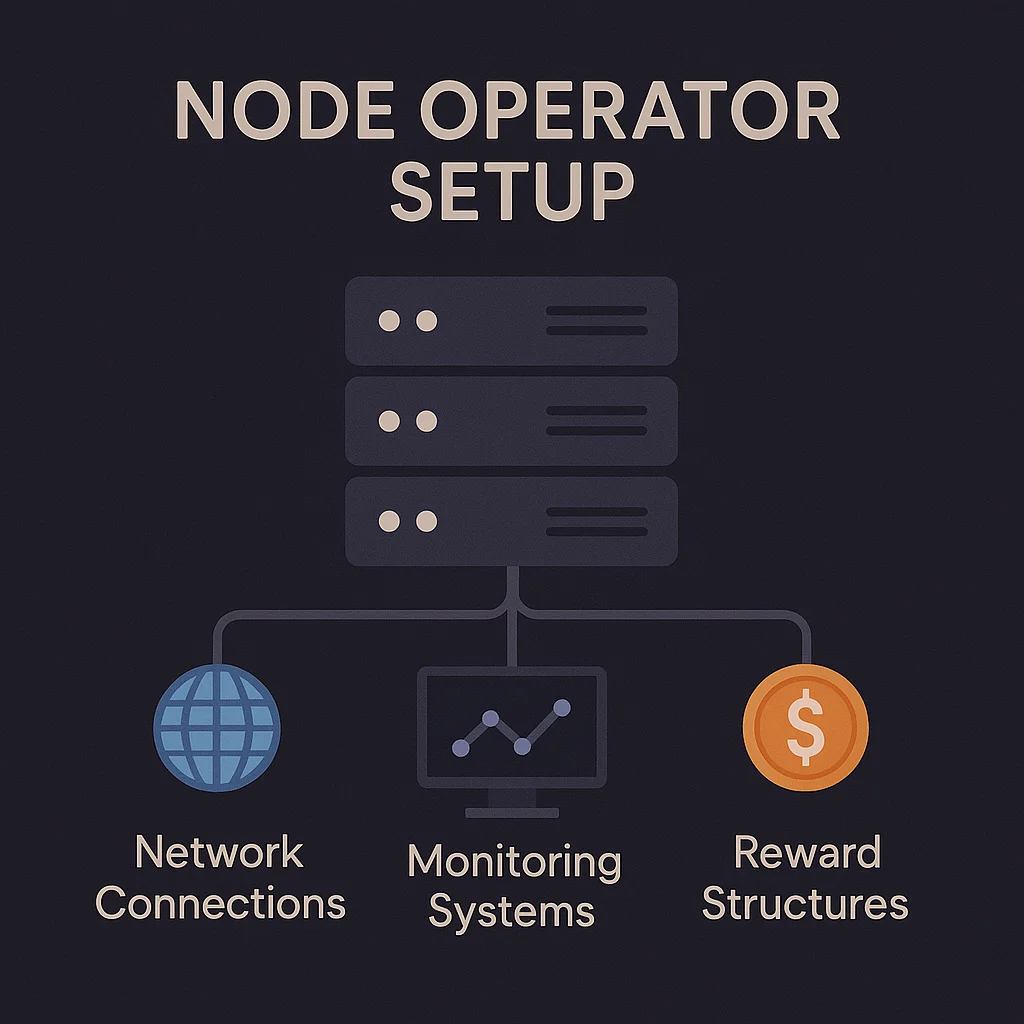
Node Operator: Network Infrastructure Providers
Node operators run the computers that power blockchain networks. They’re the internet service providers of crypto – invisible but essential infrastructure.
A node operator is an individual or organization that runs blockchain network infrastructure by maintaining nodes that validate transactions, store data, and relay information. They provide the computational backbone that keeps decentralized networks running.
How Node Operations Work
Hardware requirements vary by network but typically include reliable internet, adequate storage, and sufficient processing power to handle network demands.
Uptime responsibility requires 24/7 operation with backup systems and monitoring to ensure consistent network participation and avoid penalties.
Economic incentives reward node operators through block rewards, transaction fees, or token emissions, though costs must be balanced against rewards.
Real-World Examples
- Ethereum validators run nodes that require 32 ETH stakes and earn ~6% annual rewards
- Bitcoin full nodes provide network security and validation without direct rewards
- Chainlink oracle nodes earn LINK tokens for providing external data to smart contracts
Why Beginners Should Care
Network decentralization depends on having many independent node operators rather than concentration among a few large entities or cloud providers.
Investment opportunity exists for those with technical skills and capital to earn rewards by providing network infrastructure services.
Technical barriers make node operation challenging for most users, leading to delegation services and node-as-a-service providers.
