Account Abstraction
Account Abstraction: Smart Contract Wallets
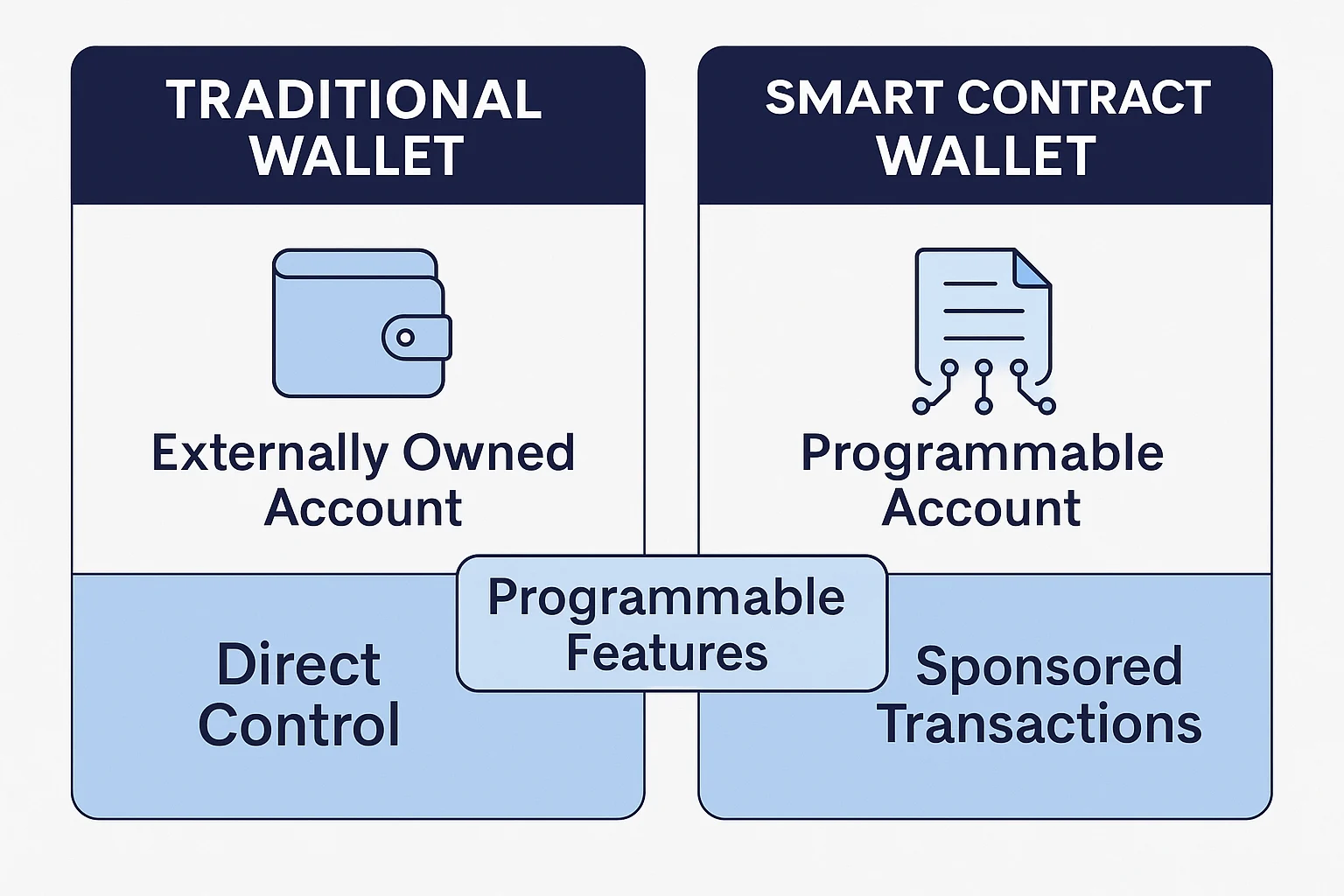
Account abstraction turns wallets into programmable smart contracts with custom logic for transaction validation. It’s like upgrading from a basic calculator to a full computer.
Account abstraction allows user accounts to be controlled by smart contract code rather than simple private key signatures. This enables programmable wallets with custom authentication, automatic payments, social recovery, and other advanced features impossible with traditional accounts.
How Account Abstraction Works
Custom validation logic replaces standard signature checks with programmable rules like multi-signature requirements, time-based restrictions, or biometric authentication.
Sponsored transactions enable third parties to pay gas fees for users, removing the need to hold native tokens for transaction costs.
Bundled operations combine multiple actions into single transactions, like approving and swapping tokens in one step rather than separate transactions.
Real-World Examples
- Safe (formerly Gnosis Safe) provides multisig smart contract wallets with recovery features
- Argent offers mobile wallets with social recovery and gasless transactions
- EIP-4337 standardizes account abstraction implementation across Ethereum
Why Beginners Should Care
Better user experience eliminates many crypto UX pain points like gas fee management, seed phrase backup, and irreversible transaction mistakes.
Enhanced security through programmable rules like spending limits, trusted contacts for recovery, and automatic fraud detection that goes beyond simple private key protection.
Mass adoption potential as account abstraction makes crypto wallets behave more like traditional banking apps that mainstream users already understand.
Related Terms: Smart Contract, Multi-Signature, Social Recovery, Gas Fees
