Chain Reorg (Reorganization)
Chain Reorg (Reorganization): Blockchain History Changes
Chain reorgs occur when a blockchain adopts a different version of transaction history, potentially reversing confirmed transactions. It’s like time travel, but messier and more expensive.
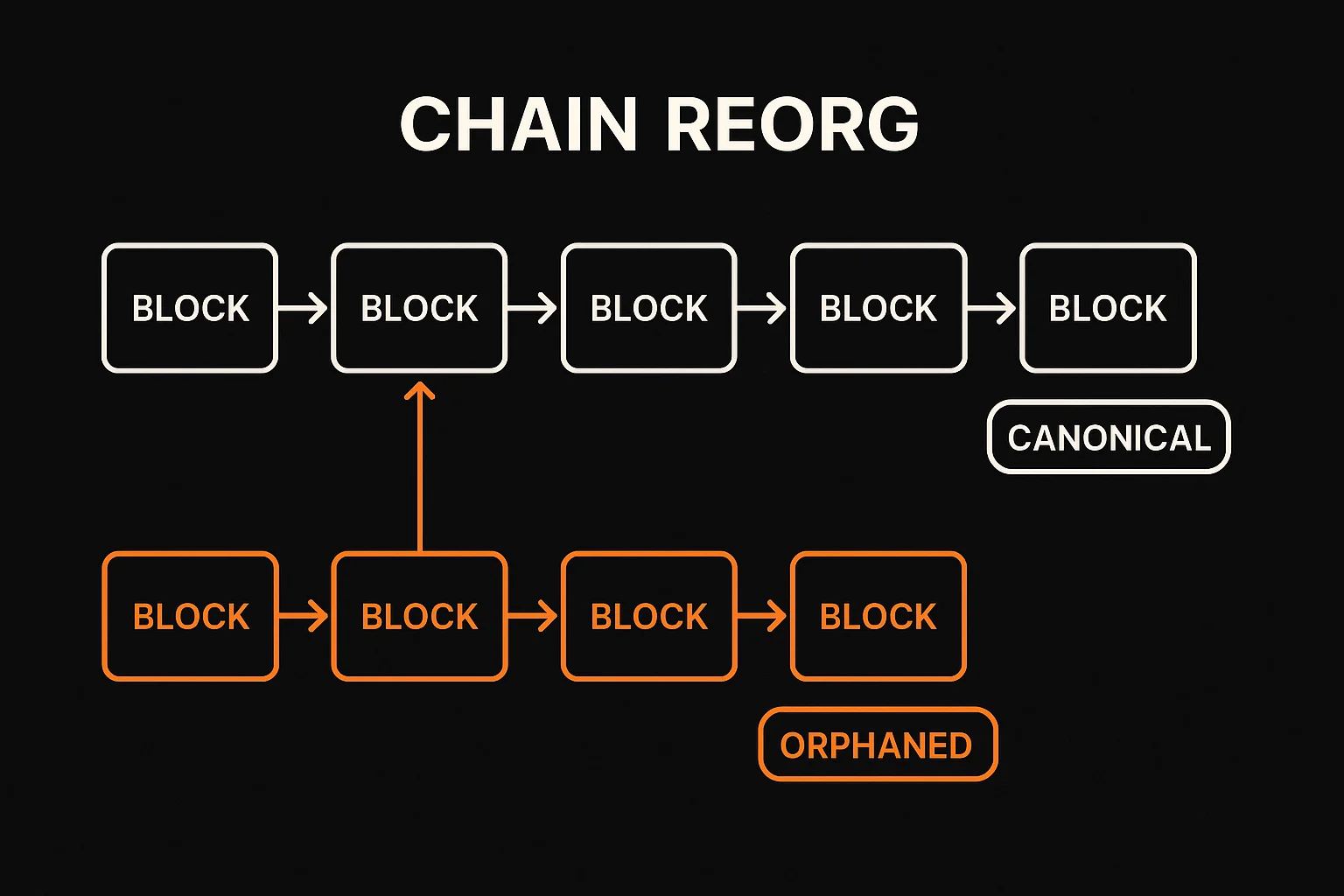
A chain reorganization (reorg) happens when a blockchain network adopts an alternative chain of blocks as the canonical history, potentially reversing previously confirmed transactions. This can occur due to network splits, competing miners, or consensus failures.
How Chain Reorgs Work
Competing chains develop when different groups of miners or validators work on different versions of blockchain history simultaneously.
Longest chain rule (or other consensus mechanisms) eventually determines which chain becomes official, potentially orphaning blocks from the alternative chain.
Transaction reversal affects any transactions that were included in orphaned blocks, requiring them to be re-confirmed in the new canonical chain.
Real-World Examples
- Ethereum Classic experienced deep reorgs during 51% attacks that reversed thousands of blocks
- Bitcoin Cash has had several reorgs during periods of hash rate instability
- Polygon faced a 157-block reorg in 2023 due to infrastructure issues
Why Beginners Should Care
Confirmation security requires waiting for multiple block confirmations to reduce the risk of transaction reversal from reorgs.
Exchange impacts as platforms may halt deposits/withdrawals during suspected reorgs to prevent double-spending attacks.
Network stability indicators include reorg frequency and depth, which signal overall blockchain health and security.
Related Terms: 51% Attack, Block Confirmation, Consensus Mechanism, Double Spending
