Hot Wallet
Hot Wallet: Convenience Over Security
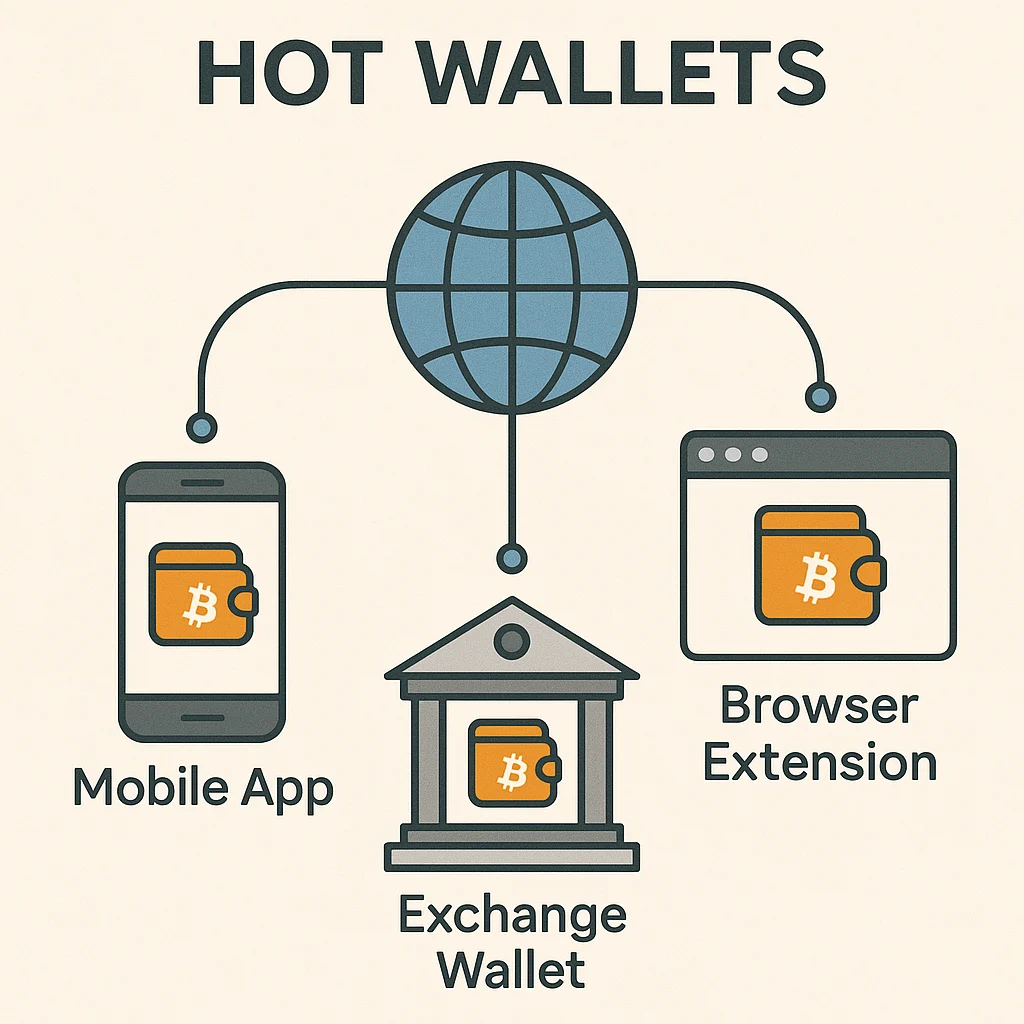
Hot wallets are your everyday crypto spending accounts. They’re connected to the internet for easy access, but that convenience comes with security trade-offs.
A hot wallet is a cryptocurrency wallet that maintains an active internet connection, allowing for quick and easy transactions. Think of it as your crypto checking account – convenient for daily use but not where you store your life savings.
How Hot Wallets Work
Software wallets on your phone or computer are the most common hot wallets. Apps like MetaMask, Trust Wallet, and Coinbase Wallet connect to the internet for seamless DeFi interactions.
Exchange wallets are also hot wallets, though you don’t control the private keys. The exchange manages the wallet infrastructure while you access funds through their interface.
Browser extensions like MetaMask inject wallet functionality into websites, enabling one-click connections to DeFi protocols and NFT marketplaces.
Real-World Examples
- MetaMask – Most popular browser extension wallet for Ethereum DeFi
- Trust Wallet – Mobile-first wallet supporting multiple blockchains
- Phantom – Leading Solana ecosystem hot wallet
Why Beginners Should Care
Hot wallets make crypto usable for daily transactions and DeFi interactions. Without them, every transaction would require connecting hardware wallets – tedious for active trading.
Security trade-offs are real. Hot wallets are vulnerable to malware, phishing attacks, and device theft. Never store large amounts in hot wallets long-term.
Best practice: Use hot wallets for small amounts and active trading, cold storage for long-term holdings. It’s like carrying spending money in your physical wallet while keeping savings in the bank.
Related Terms: Cold Wallet, MetaMask, Private Key, DeFi
