DeFi Aggregator
DeFi Aggregator: Finding the Best Yields
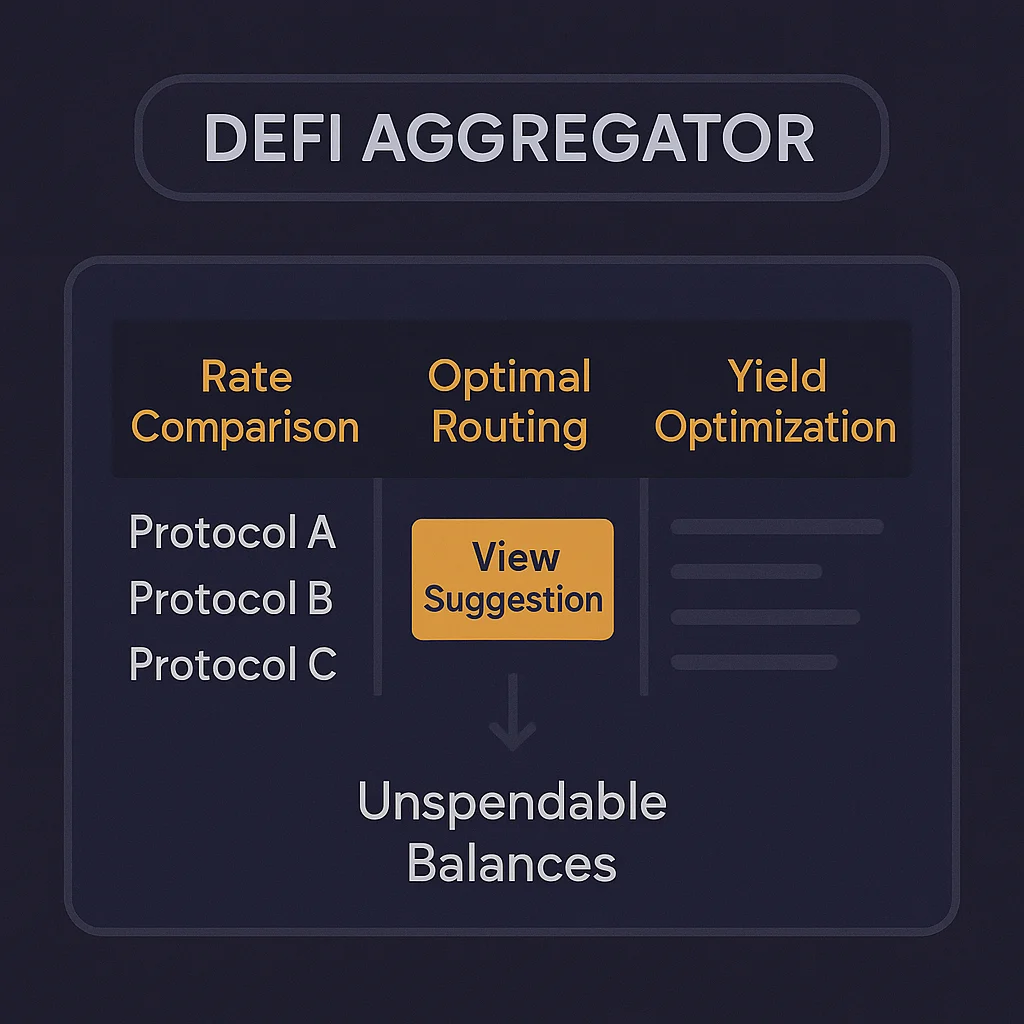
DeFi aggregators automatically find the best rates across multiple protocols for lending, borrowing, or trading. They’re like Expedia for decentralized finance.
A DeFi aggregator is a platform that searches multiple protocols to find the best rates, yields, or liquidity for users’ specific needs. Instead of manually checking dozens of platforms, aggregators do the comparison shopping automatically.
How DeFi Aggregators Work
Rate comparison across lending protocols, DEXs, and yield farming opportunities to identify the highest returns or lowest costs for specific actions.
Smart routing splits large trades across multiple DEXs to minimize slippage and maximize execution efficiency compared to single-platform trades.
Yield optimization automatically moves funds between protocols as rates change, maintaining exposure to the highest available returns.
Real-World Examples
- 1inch aggregates DEX liquidity to find best trading prices across multiple exchanges
- Yearn Finance automatically moves deposited funds to highest-yielding opportunities
- Zapper simplifies complex DeFi interactions through a single interface
Why Beginners Should Care
Time savings from aggregators eliminate the need to manually research and compare rates across dozens of constantly changing DeFi protocols.
Better execution through smart routing and yield optimization can significantly improve returns compared to single-protocol strategies.
Smart contract risk increases when aggregators interact with multiple protocols, as vulnerabilities in any connected platform could affect aggregator users.
Related Terms: Yield Farming, DEX, Slippage, Yield Optimization
