Multi-Signature (Multisig)
Multi-Signature (Multisig): Shared Control for Enhanced Security
Multisig wallets require multiple signatures to authorize transactions. It’s like requiring multiple keys to open a safe – no single person can move funds alone.
Multi-signature (multisig) is a wallet configuration that requires signatures from multiple private keys to authorize transactions. Common setups include 2-of-3 (any 2 signatures from 3 possible) or 3-of-5 configurations.
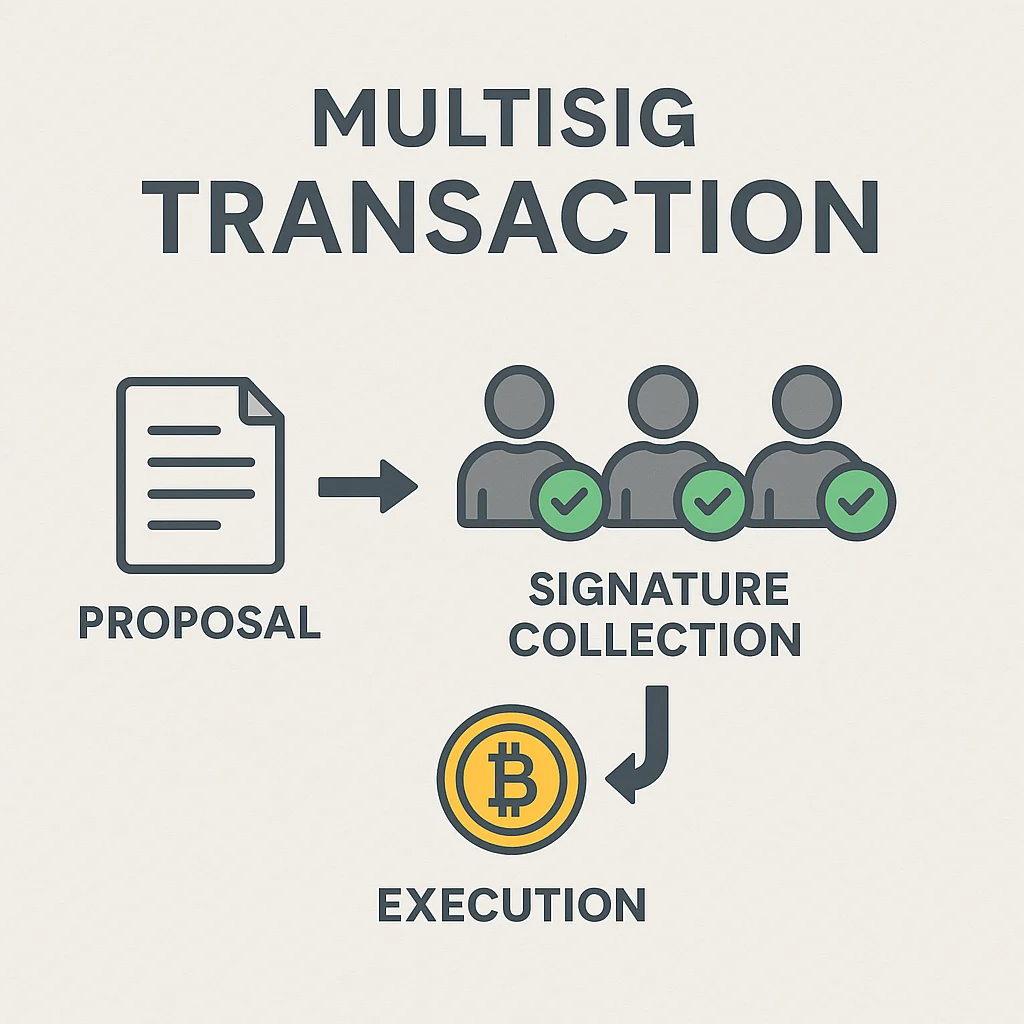
How Multisig Works
Smart contracts enforce the signature requirements. When someone initiates a transaction, the contract waits for the required number of valid signatures before executing.
Key distribution among trusted parties or devices prevents single points of failure. Even if one key is compromised, attackers can’t steal funds without additional signatures.
Business applications use multisig for treasury management, requiring approval from multiple executives before spending company funds.
Real-World Examples
- Gnosis Safe – Popular multisig platform managing billions in DeFi treasuries
- Corporate treasuries often require 3-of-5 signatures from board members
- Personal security setups with keys split between hardware wallets and trusted contacts
Why Beginners Should Care
Multisig eliminates single points of failure that plague most crypto security. If you lose one key or device, you can still access funds with remaining signatures.
Setup complexity requires technical knowledge and coordination between signers. Losing too many keys simultaneously can permanently lock funds.
For large holdings, multisig provides institutional-grade security that exceeds what most individuals can achieve with single-signature wallets.
Related Terms: Hardware Wallet, Smart Contract, Private Key, Cold Storage
