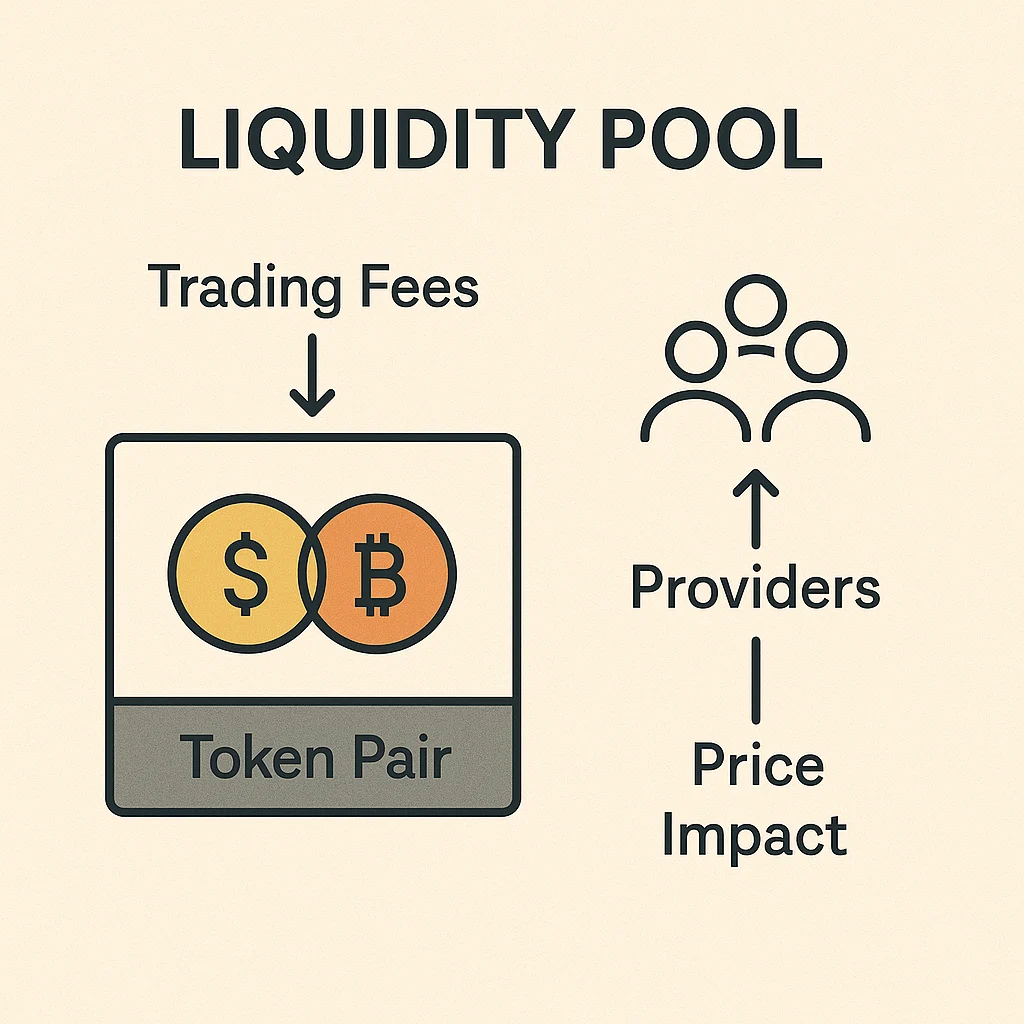
Liquidity Pool
Liquidity Pool: The Fuel That Powers DEX Trading
Liquidity pools are why decentralized exchanges work. They’re shared pots of tokens that enable trading without traditional buyers and sellers.
A liquidity pool is a collection of tokens locked in a smart contract that provides liquidity for decentralized trading. Instead of matching buy and sell orders, traders swap against these pools using automated market maker (AMM) algorithms.
How Liquidity Pools Work
Liquidity providers deposit equal values of two tokens (like ETH and USDC) into a pool. When traders want to swap ETH for USDC, they trade against this pool rather than with another person.
The pool maintains balance using mathematical formulas. As one token gets scarce, its price automatically increases to encourage arbitrageurs to rebalance the pool.
Liquidity providers earn trading fees proportional to their share of the pool. More trading volume means more fees for providers.
Real-World Examples
- ETH/USDC pools on Uniswap earn steady fees from high trading volume
- Stablecoin pools offer lower risk but smaller returns
- New token pools can be highly profitable but extremely risky
Why Beginners Should Care
Liquidity pools let you earn passive income from your crypto holdings. Instead of holding tokens that do nothing, you can put them to work earning trading fees.
But understand impermanent loss first – if token prices diverge significantly, you might end up with less value than just holding the tokens separately.
Related Terms: DEX, Impermanent Loss, Yield Farming, AMM
