Yield Farming
Yield Farming: Crypto’s High-Risk, High-Reward Game
Yield farming is DeFi’s answer to traditional investing – except the yields are higher, the risks are bigger, and the game changes daily.
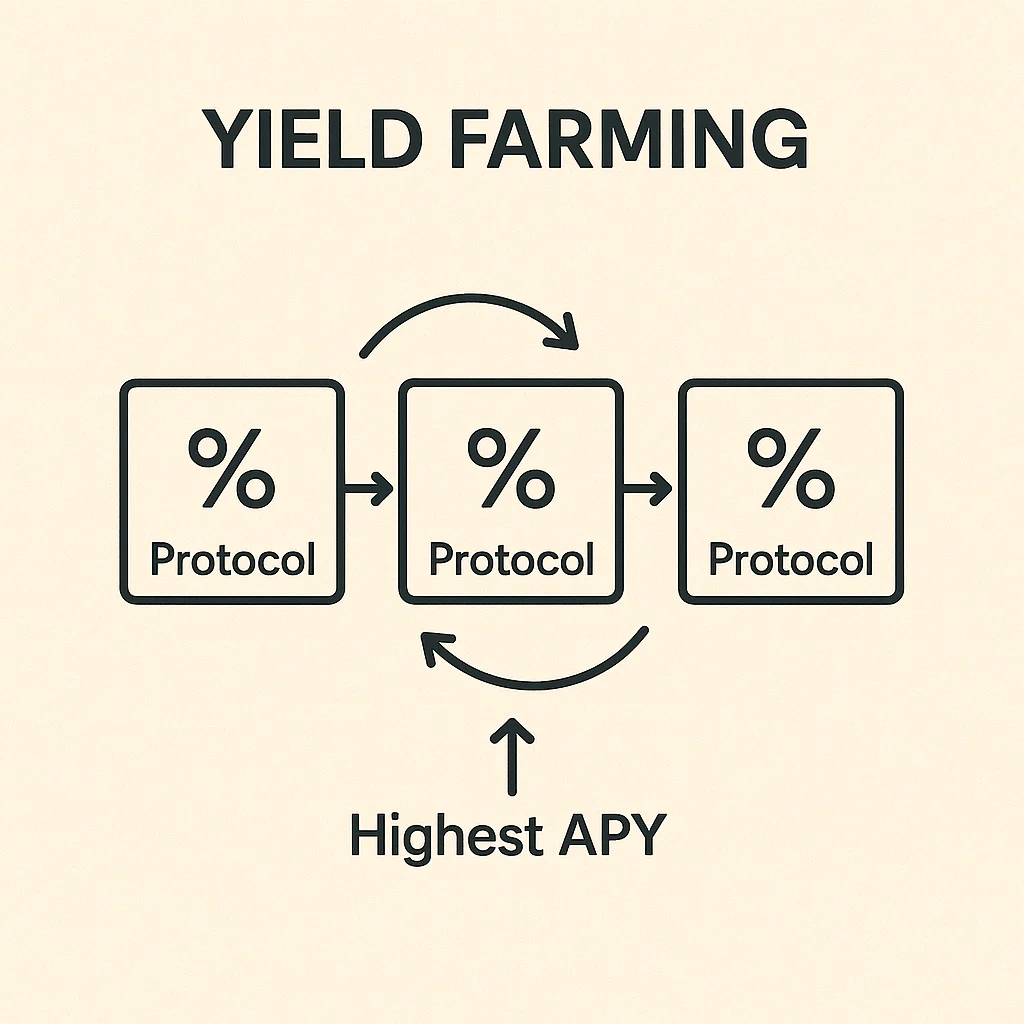
Yield farming is the practice of lending, staking, or providing liquidity with your cryptocurrency to earn maximum returns across multiple DeFi protocols. It’s like playing musical chairs with your money, constantly moving to wherever yields are highest.
How Yield Farming Works
Farmers deploy capital across different DeFi protocols to maximize returns. This might involve providing liquidity to DEXs, lending on money markets, or staking governance tokens.
Strategy matters. Smart farmers compound their rewards, reinvesting earnings to grow their positions. They also chase new opportunities as yields shift between protocols.
Advanced farmers use leverage, borrowing against collateral to increase their farming positions. This amplifies both gains and losses dramatically.
Real-World Examples
- Compound – Lend USDC at 5% APY, earn COMP tokens worth another 3%
- Curve – Provide stablecoin liquidity for 8% base APY plus CRV rewards
- Convex – Boost Curve yields through optimized staking strategies
Why Beginners Should Care
Yield farming can generate impressive returns – 20-100%+ APY isn’t uncommon during bull markets. But these protocols are experimental and uninsured.
Smart contracts can have bugs. Tokens can lose value overnight. Regulations can change. Only farm with money you can afford to lose completely.
Related Terms: Liquidity Pool, Staking, DeFi, Impermanent Loss
