Governance Token
Governance Token: Voting Rights in Digital Form
Governance tokens turn users into stakeholders with voting power over protocol decisions. It’s democracy meets DeFi, with mixed results.
A governance token grants holders voting rights on protocol decisions like parameter changes, upgrade proposals, treasury spending, and strategic direction. Token weight typically determines voting power – more tokens mean stronger influence.
How Governance Tokens Work
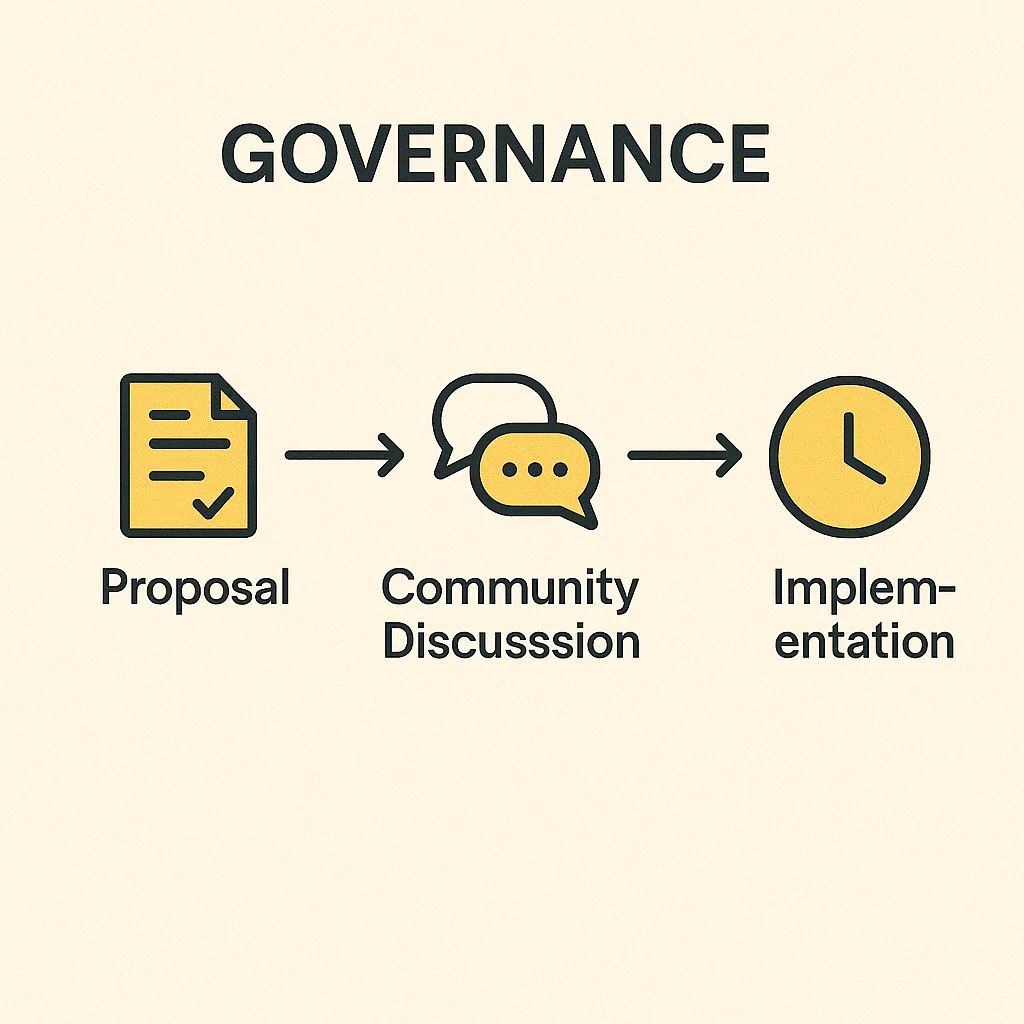
Proposal systems allow token holders to suggest changes to protocols. Proposals typically require minimum token thresholds to prevent spam and ensure serious consideration.
Voting mechanisms vary from simple majority rules to complex systems requiring different quorum levels for different decision types. Some protocols implement time delays before executing approved changes.
Delegation options let smaller holders combine their voting power by delegating to trusted community members who actively participate in governance decisions.
Real-World Examples
- UNI tokens govern Uniswap protocol fees, treasury allocation, and partnership decisions
- COMP tokens control Compound lending protocol interest rates and collateral factors
- MKR tokens manage the MakerDAO system backing the DAI stablecoin
Why Beginners Should Care
Governance participation can be profitable when protocols vote to distribute treasury funds or change fee structures that benefit token holders.
Whale dominance is common – large holders often control governance outcomes regardless of smaller holder preferences. True decentralization remains elusive for most protocols.
Regulatory uncertainty surrounds governance tokens. Some might be classified as securities, affecting their legal status and exchange listings.
Related Terms: DAO, Voting, Tokenomics, Decentralization
