Gas Limit
Gas Limit: Setting Your Transaction Budget
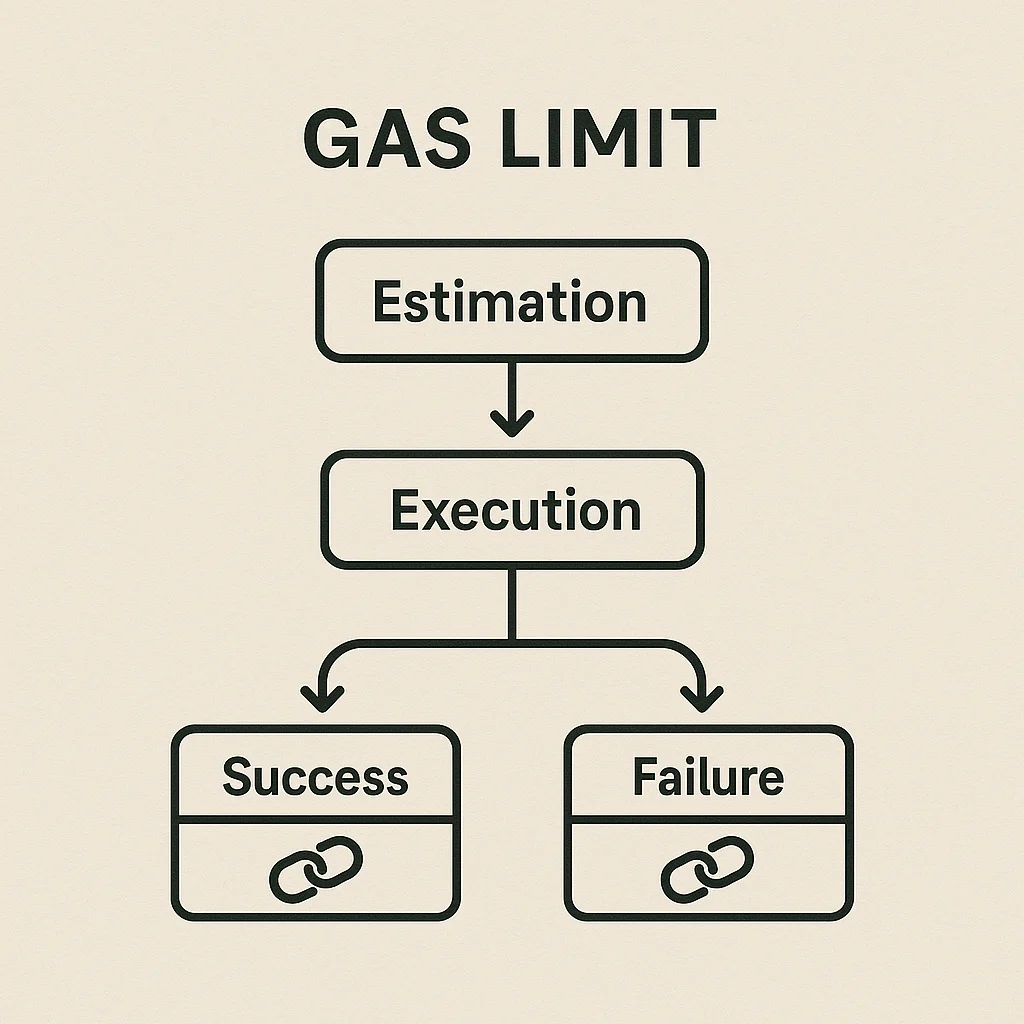
Gas limit is the maximum amount of gas you’re willing to spend on a transaction. Set it too low and your transaction fails. Set it too high and you overpay for simple operations.
Gas limit is the maximum amount of computational work (measured in gas units) that a user is willing to pay for when submitting a transaction to the Ethereum network. It acts as a safety mechanism preventing runaway smart contracts from draining your wallet.
How Gas Limit Works
Computational budgeting ensures transactions can’t consume unlimited resources. Each operation in smart contracts has a predefined gas cost, and the total can’t exceed your set limit.
Transaction failure occurs if operations require more gas than your limit allows. You still pay for gas consumed up to the failure point, but the transaction doesn’t complete.
Estimation tools in wallets automatically suggest appropriate gas limits based on transaction complexity, though users can adjust these recommendations manually.
Real-World Examples
- Simple ETH transfers typically need 21,000 gas limit
- DEX swaps might require 150,000-300,000 gas depending on complexity
- Complex DeFi operations can need 500,000+ gas for multi-step transactions
Why Beginners Should Care
Failed transactions still cost money if they run out of gas, so understanding appropriate limits prevents wasted fees on unsuccessful operations.
Overpaying happens when gas limits are set much higher than needed. Unused gas gets refunded, but setting reasonable limits prevents tying up excess funds.
Network congestion affects optimal gas limit strategies. During high demand, slightly higher limits can prevent failures when network conditions change between submission and execution.
Related Terms: Gas Fees, Gas Price, Smart Contract, Transaction
