Crypto Vesting Schedule
Crypto Vesting Schedule: Gradual Token Release
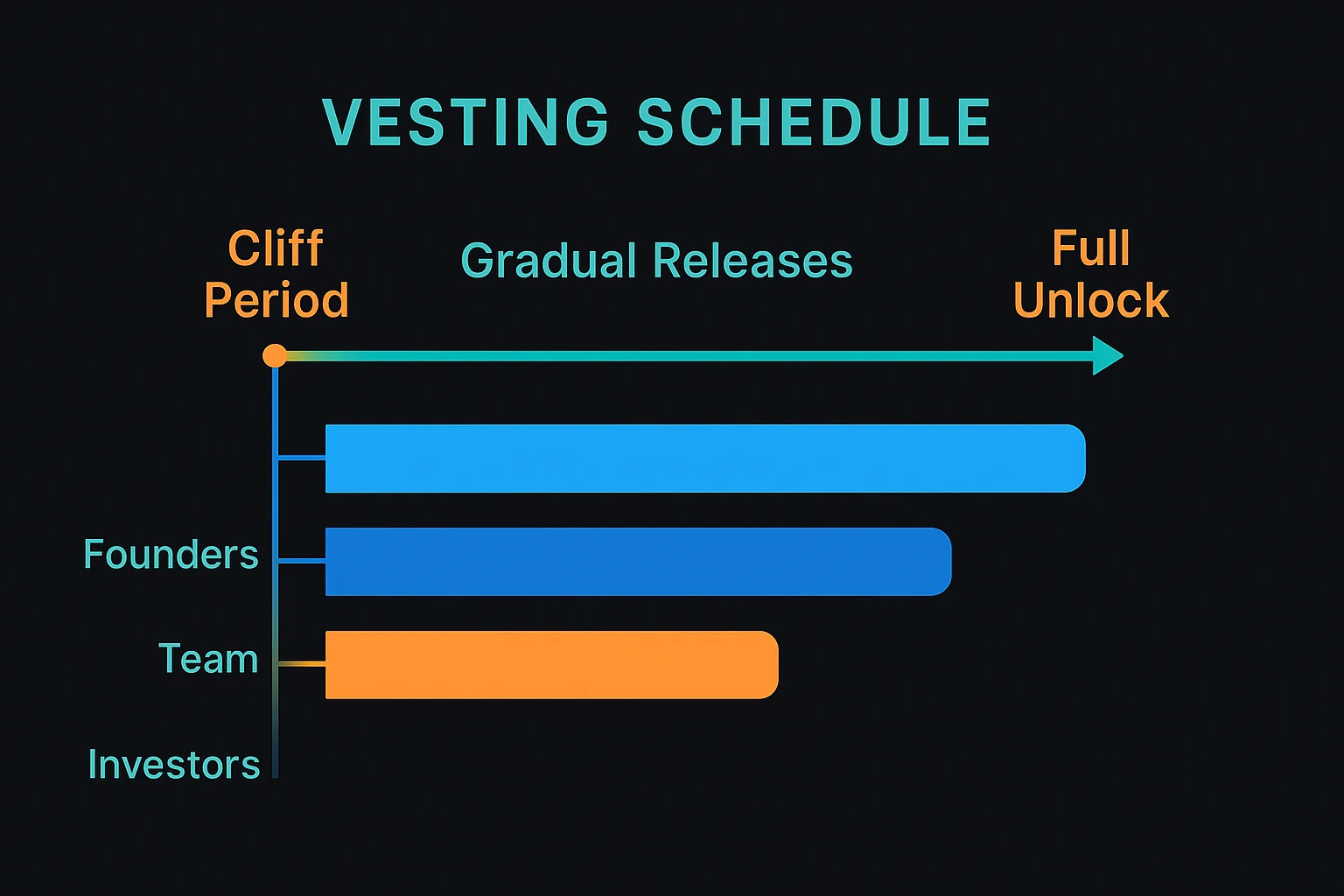
Vesting schedules control when team members, investors, or community members can access their allocated tokens. It’s like having a time-locked savings account that prevents dumping.
A crypto vesting schedule defines when and how allocated tokens become available for use, typically spreading releases over months or years to prevent market dumping. Different stakeholders usually have different vesting terms based on their role and contribution timing.
How Vesting Schedules Work
Time-based releases unlock predetermined percentages of tokens at regular intervals, such as monthly or quarterly distributions over 2-4 years.
Cliff periods require waiting a minimum time before any tokens become available, ensuring initial commitment before any rewards are accessible.
Performance milestones may trigger additional unlocks based on project achievements, user adoption, or revenue targets rather than pure time passage.
Real-World Examples
- Team allocations often have 1-year cliffs with 4-year total vesting to ensure long-term commitment
- Investor tokens may have shorter 6-month cliffs with 2-year vesting periods
- Community rewards sometimes have no cliffs but longer overall vesting to encourage participation
Why Beginners Should Care
Market pressure understanding helps predict potential selling pressure as large token allocations become available for trading.
Team incentives alignment through long vesting periods suggests teams are committed to long-term project success rather than quick exits.
Investment timing considerations around major vesting events that could significantly impact token prices through increased supply.
Related Terms: Token Allocation, Lock-up Period, Team Incentives, Supply Schedule
