Flashbots
Flashbots: MEV Infrastructure
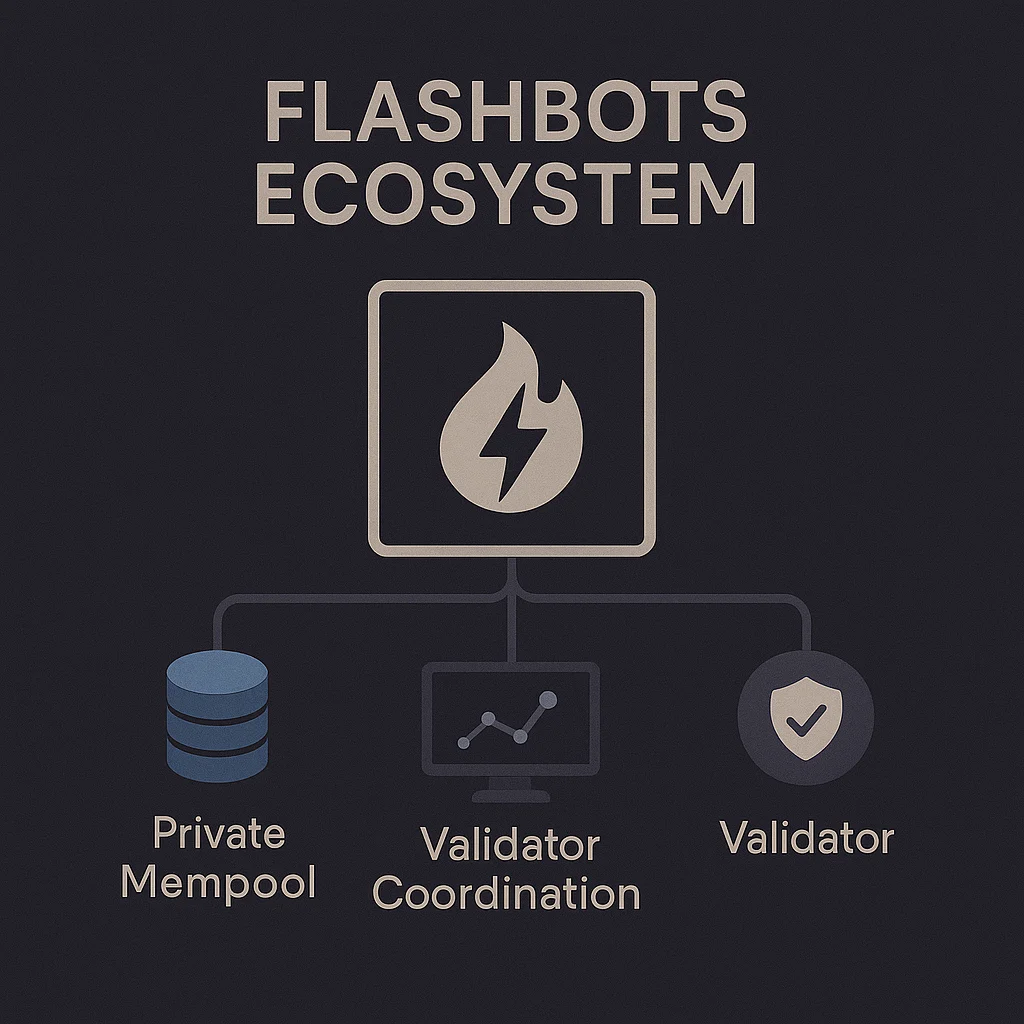
Flashbots is a research and development organization that builds infrastructure to mitigate the negative externalities of MEV. They’re trying to make the blockchain economy more fair and transparent.
Flashbots develops tools and infrastructure to democratize MEV extraction and reduce its harmful effects on regular users. Their products include private mempools, MEV-protected transaction ordering, and research into fair value extraction mechanisms.
How Flashbots Works
Private mempools allow users to submit transactions without revealing them publicly until inclusion, preventing front-running and sandwich attacks.
MEV-Boost enables Ethereum validators to maximize their revenue from block production while maintaining network decentralization and censorship resistance.
Research initiatives study MEV’s impact on network security, user experience, and economic fairness to guide development of better solutions.
Real-World Examples
- Ethereum block building uses Flashbots infrastructure for over 90% of blocks since the Merge
- MEV protection services route transactions through Flashbots to reduce user exploitation
- Academic research on MEV economics and mitigation strategies guides protocol development
Why Beginners Should Care
User protection from Flashbots infrastructure reduces the hidden tax of MEV extraction that affects almost every DeFi transaction.
Democratization efforts aim to make MEV benefits available to regular users rather than only sophisticated bots and institutional actors.
Centralization concerns arise as Flashbots infrastructure becomes critical to Ethereum’s operation, raising questions about single points of failure.
Related Terms: MEV, Private Mempool, Block Building, Front-Running
