Bagholder
Bagholder: Stuck with Worthless Tokens
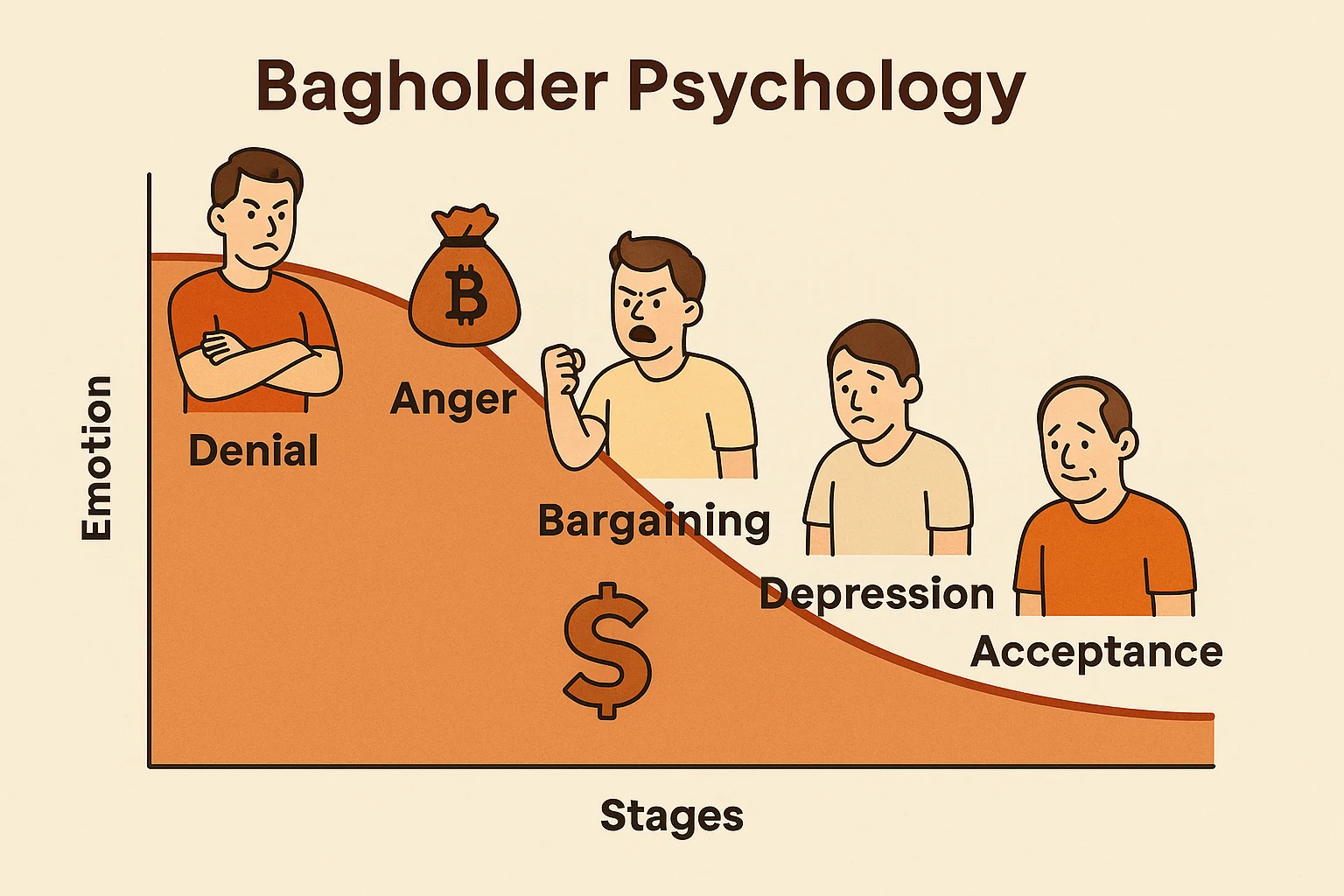
A bagholder is someone stuck holding cryptocurrency that has lost most of its value with little hope of recovery. It’s crypto’s version of being left holding the bag.
A bagholder is an investor who continues holding a cryptocurrency that has significantly decreased in value, often because they’re unable or unwilling to realize the loss. The “bag” represents their depreciating investment that nobody else wants to buy.
How People Become Bagholders
FOMO buying near price peaks leaves investors with positions that immediately move against them as market sentiment shifts and prices crash.
Averaging down on failing investments can turn small losses into large ones as investors throw good money after bad, increasing their position size in declining assets.
Emotional attachment to projects or communities prevents rational selling decisions even when fundamental reasons for holding no longer exist.
Real-World Examples
- ICO token holders from 2017-2018 who bought projects that never delivered working products
- Terra Luna investors who held through the algorithmic stablecoin collapse
- Various DeFi token holders who believed in projects that got abandoned or exploited
Why Beginners Should Care
Cutting losses is often the smart financial decision, but psychological factors make it difficult to admit mistakes and move on to better opportunities.
Opportunity cost of bagholding means missing other investments while holding depreciating assets that may never recover their previous values.
Tax strategies can make bagholding rational in some cases where realizing losses provides tax benefits that offset portfolio optimization concerns.
Related Terms: FOMO, Paper Hands, Sunk Cost, Exit Strategy
