Sniper Bot
Sniper Bot: Automated MEV Extraction
Sniper bots automatically execute trades ahead of other users to capture arbitrage opportunities and extract MEV. They’re the high-frequency traders of DeFi, but without regulatory oversight.
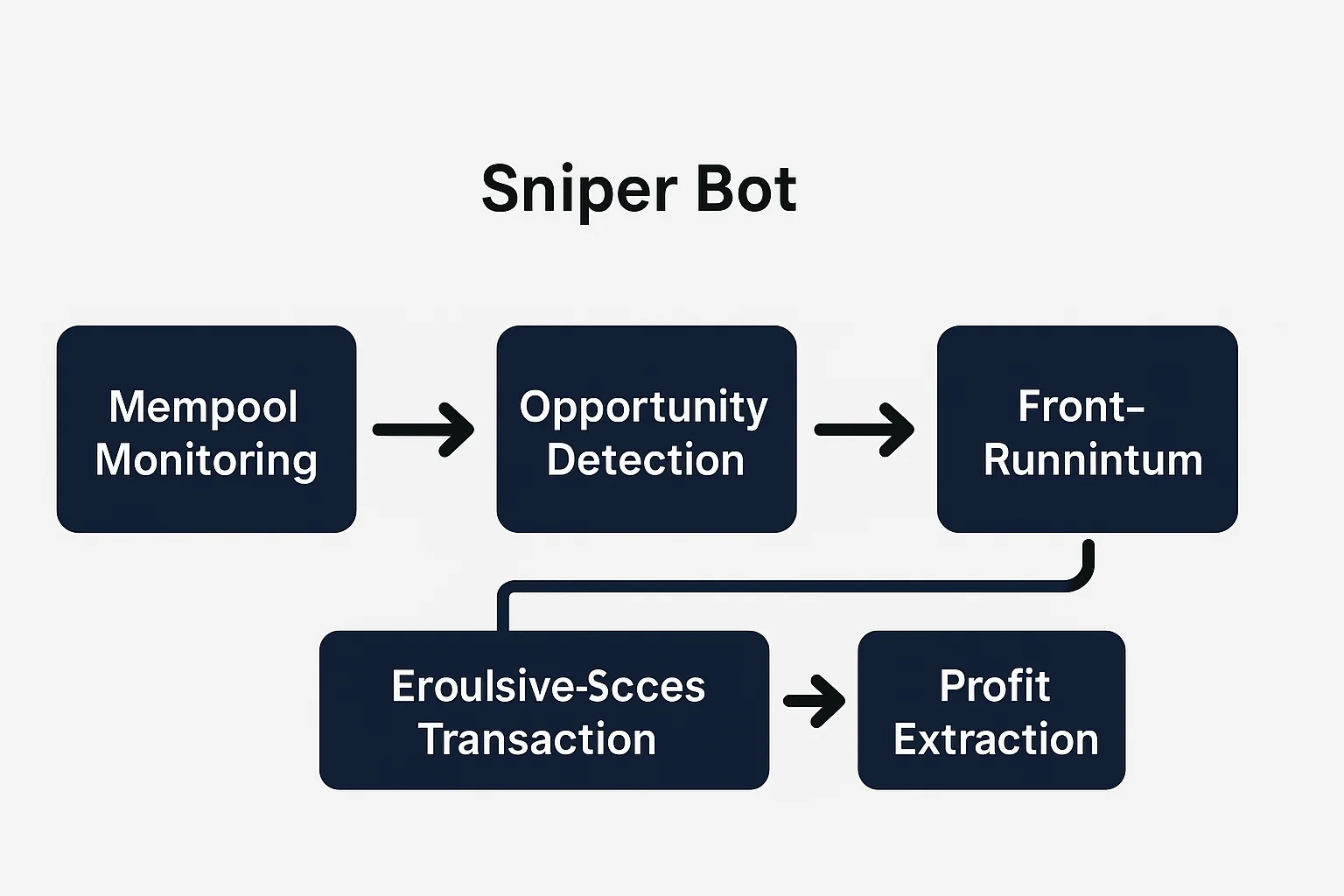
A sniper bot is an automated program that monitors blockchain mempools for profitable trading opportunities and executes transactions faster than human traders. These bots specialize in front-running, arbitrage, and MEV extraction across DeFi protocols.
How Sniper Bots Work
Mempool monitoring tracks pending transactions before they’re included in blocks, identifying profitable opportunities like large trades that will move prices.
Gas price optimization ensures bot transactions get prioritized by miners through higher fees, often paying 10-100x normal gas prices for speed advantages.
Atomic execution combines multiple trades into single transactions that either complete entirely or fail completely, eliminating partial execution risks.
Real-World Examples
- DEX arbitrage bots exploit price differences between Uniswap, SushiSwap, and other exchanges
- Liquidation bots compete to liquidate undercollateralized positions for profit
- NFT sniping involves bots purchasing underpriced NFTs milliseconds after listing
Why Beginners Should Care
Hidden tax on regular users as sniper bots extract value from almost every large DeFi transaction through increased slippage and worse execution prices.
Technical arms race makes it nearly impossible for manual traders to compete with sophisticated bots that can execute trades in milliseconds.
Protocol responses include MEV-protected RPCs, private mempools, and fair sequencing services that aim to reduce bot advantages.
Related Terms: MEV, Front-Running, Arbitrage, Gas Price
