Web3
Web3: The Decentralized Internet Dream
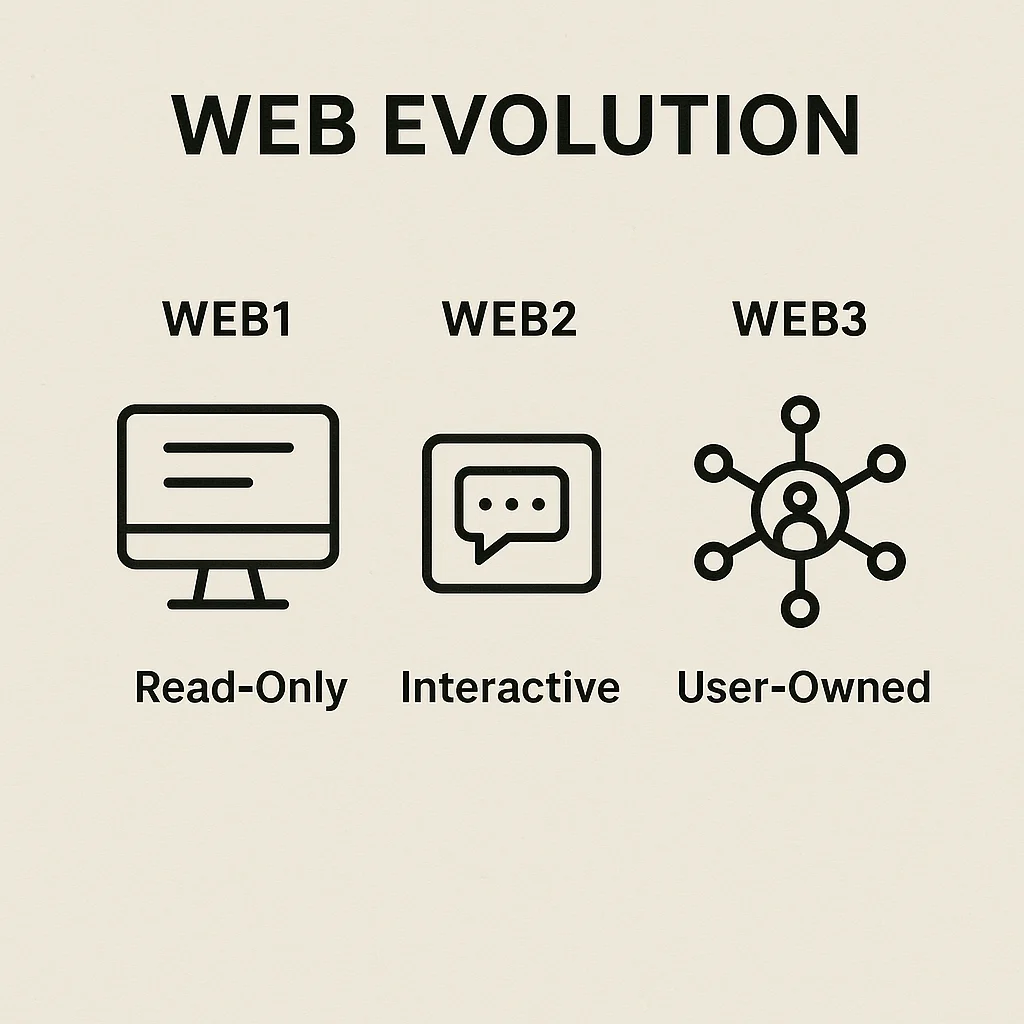
Web3 promises an internet where users own their data, identity, and digital assets instead of tech giants controlling everything. It’s part vision, part reality, part marketing buzzword.
Web3 refers to a decentralized version of the internet built on blockchain technology where users control their own data, identity, and assets rather than relying on centralized platforms. It aims to replace Web2’s platform monopolies with user-owned networks.
How Web3 Works
Decentralized applications (dApps) run on blockchain networks instead of centralized servers, making them censorship-resistant and user-controlled rather than platform-controlled.
Self-sovereign identity lets users control their digital identity across platforms without relying on Google, Facebook, or other centralized identity providers.
Token-based incentives align user and network interests by giving users ownership stakes in the platforms they use, rather than just being unpaid data sources.
Real-World Examples
- ENS domains (.eth addresses) provide decentralized, user-owned website and identity systems
- IPFS storage offers decentralized file storage resistant to censorship and platform shutdowns
- DeFi protocols enable financial services without traditional banking intermediaries
Why Beginners Should Care
Web3 adoption remains early-stage with significant user experience challenges compared to polished Web2 applications. Most users aren’t ready to manage private keys for every online interaction.
Decentralization benefits include censorship resistance, platform independence, and user ownership of data and assets created online.
Investment opportunities exist in Web3 infrastructure, but many projects are experimental with uncertain long-term viability and regulatory challenges.
Related Terms: dApp, Decentralization, Self-Sovereign Identity, Token Economy
