Wrapped Token
Wrapped Token: Bringing Assets Cross-Chain
Wrapped tokens let you use Bitcoin on Ethereum, Ethereum on Solana, and any asset on any blockchain. They’re the universal adapters of crypto.
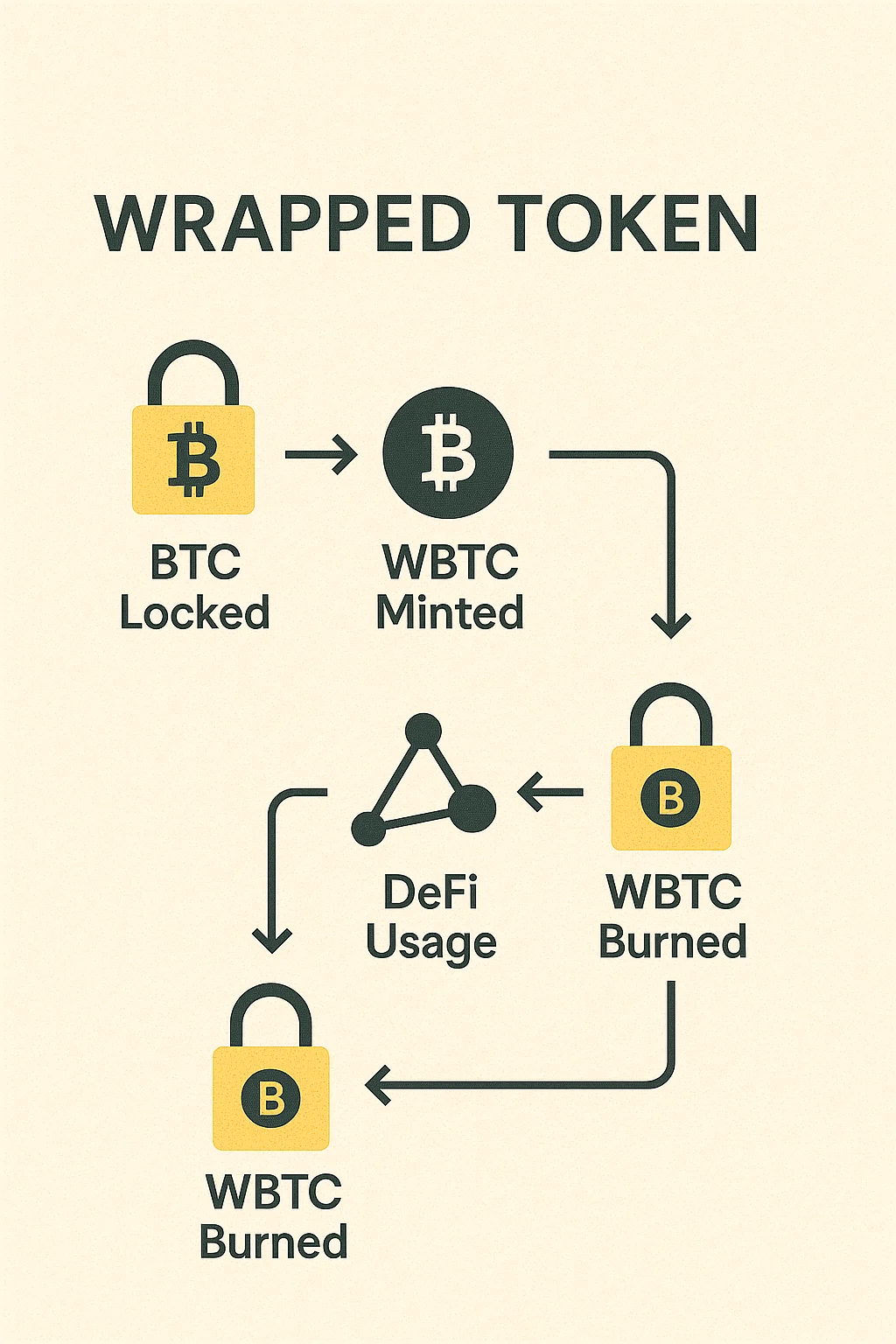
A wrapped token is a cryptocurrency that represents another asset on a different blockchain, maintaining a 1:1 peg through collateralization. The original asset gets locked in a smart contract while an equivalent wrapped version gets minted on the target chain.
How Wrapped Tokens Work
Custodial wrapping involves trusted entities holding the original asset and minting wrapped versions. WBTC uses this model – BitGo holds real Bitcoin while minting wrapped Bitcoin on Ethereum.
Decentralized bridges use smart contracts and multi-signature schemes to lock assets and mint wrapped versions without single custodians. These are more decentralized but also more complex.
Burning and redemption processes allow users to destroy wrapped tokens and receive the underlying asset back, maintaining the 1:1 peg relationship.
Real-World Examples
- Wrapped Bitcoin (WBTC) – Bitcoin usable in Ethereum DeFi with $1+ billion market cap
- Wrapped Ethereum (WETH) – ETH conforming to ERC-20 standards for DeFi compatibility
- Cross-chain bridges creating wrapped versions of tokens across different blockchains
Why Beginners Should Care
Wrapped tokens unlock cross-chain DeFi opportunities. You can earn yield on Bitcoin through Ethereum protocols or use Ethereum assets on faster, cheaper chains.
Trust assumptions vary significantly. Custodial wrapped tokens require trusting centralized entities, while decentralized bridges have smart contract risks.
Depeg risks exist if the backing mechanism fails. Wrapped tokens should trade at 1:1 with underlying assets, but this isn’t guaranteed during extreme market stress.
Related Terms: Bridge, Cross-Chain, DeFi, Smart Contract
