Decentralized Exchange (DEX)
Decentralized Exchange (DEX): Trading Without Middlemen
DEXs are what happens when you remove the corporate overlords from crypto trading. No account required, no permission needed – just you, your wallet, and the market.
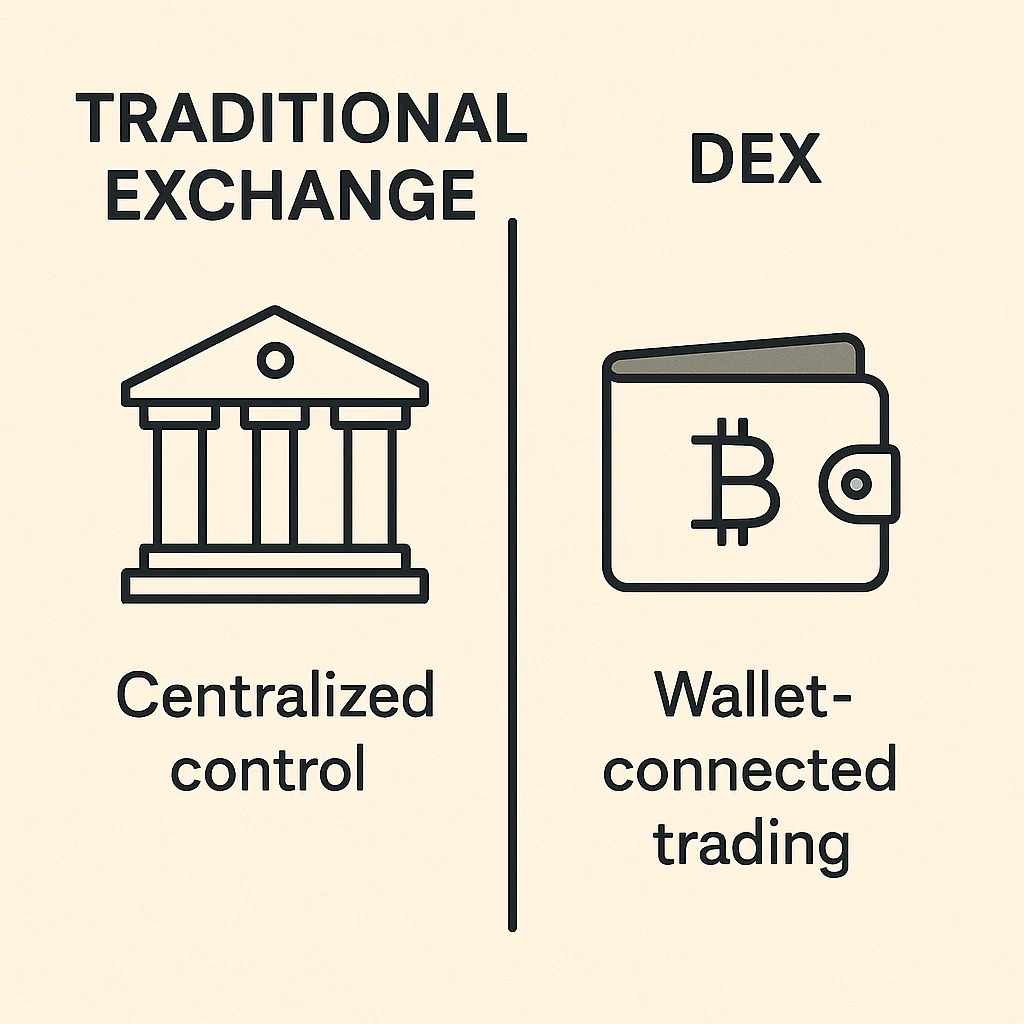
A decentralized exchange (DEX) is a cryptocurrency trading platform that operates without a central authority controlling user funds. You trade directly from your wallet using smart contracts that automatically execute trades when conditions are met.
How DEXs Work
Instead of depositing funds into an exchange account, you connect your wallet directly to the DEX. Smart contracts hold the trading logic and automatically swap tokens when you make a trade.
Liquidity pools replace traditional order books. Users deposit token pairs into pools, earning fees when others trade against their liquidity. No market makers, no trading desks – just code and math.
Your funds never leave your control until the exact moment of the trade. No KYC forms, no account freezes, no “maintenance” that locks you out during market crashes.
Real-World Examples
- Uniswap – Largest DEX on Ethereum with billions in trading volume
- PancakeSwap – Popular DEX on Binance Smart Chain with lower fees
- SushiSwap – Community-owned DEX with governance tokens
Why Beginners Should Care
DEXs give you true financial sovereignty. No exchange can freeze your account, require additional verification, or shut down withdrawals when markets get volatile.
The trade-off is complexity – DEX interfaces assume you understand gas fees, slippage, and wallet management. Start small and practice before committing serious money.
Related Terms: Smart Contract, Liquidity Pool, Gas Fees, Exchange
