Hash Rate
Hash Rate: Network Security Measurement
Hash rate measures how much computational power secures a blockchain network. Higher hash rates mean stronger security against attacks and manipulation.
Hash rate is the total computational power used by miners to process transactions and secure a proof-of-work blockchain network. It’s measured in hashes per second – calculations attempting to solve the cryptographic puzzle for each block.
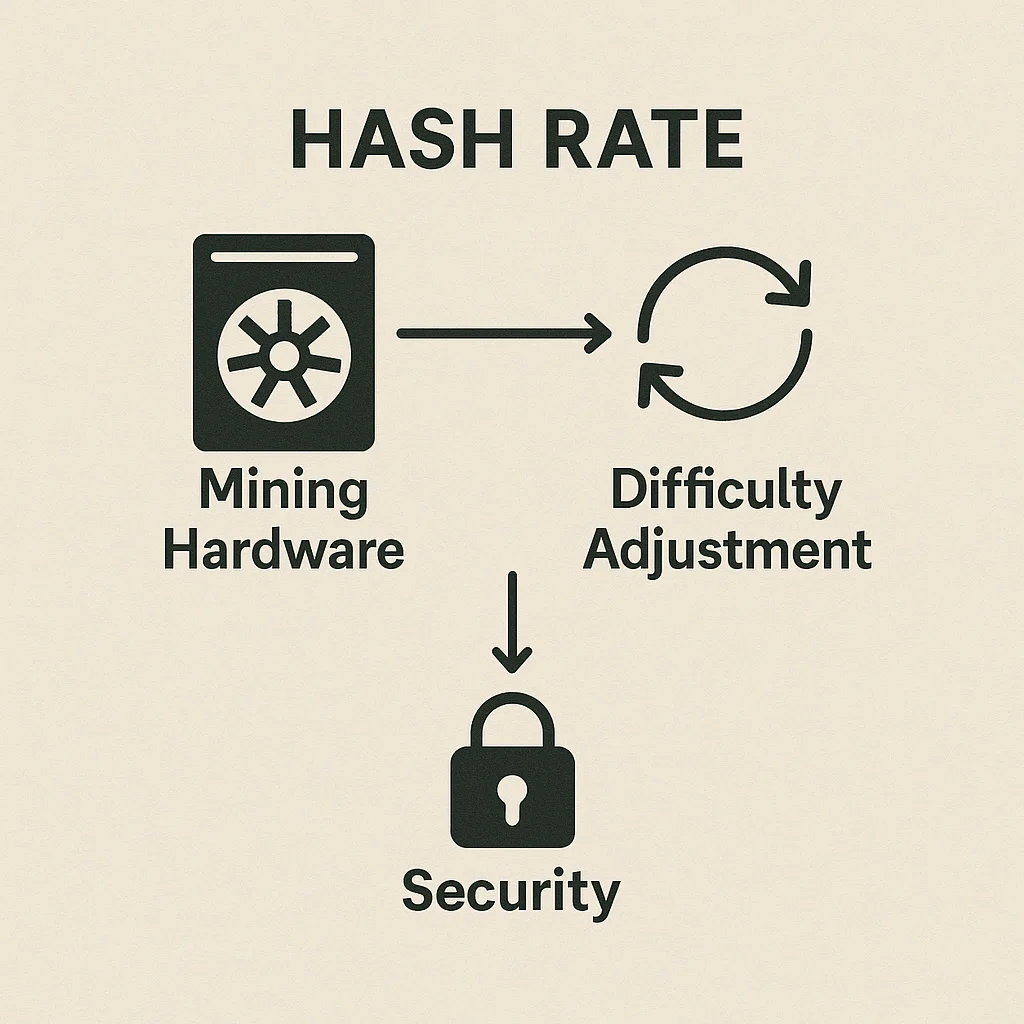
How Hash Rate Works
Mining competition drives hash rate as miners add computational power to increase their chances of earning block rewards. More miners mean higher total hash rate.
Difficulty adjustment maintains consistent block times as hash rate changes. If hash rate doubles, difficulty increases to keep block times steady at target intervals.
Security correlation exists between hash rate and network security. Higher hash rates make 51% attacks more expensive and practically impossible for major networks.
Real-World Examples
- Bitcoin hash rate exceeded 500 exahashes per second at peak – more computing power than all global supercomputers combined
- Hash rate crashes during miner capitulation events can temporarily reduce network security
- Geographic distribution of hash rate affects decentralization and regulatory risks
Why Beginners Should Care
Hash rate trends indicate miner confidence in long-term profitability. Sustained hash rate growth suggests healthy network fundamentals and security.
Network security depends on hash rate distribution. Concentrated hash rate in single locations or entities creates centralization risks and potential attack vectors.
Mining bans or regulatory crackdowns can cause temporary hash rate drops, affecting transaction processing times until difficulty adjusts downward.
Related Terms: Mining, Proof of Work, Difficulty, 51% Attack
