Autonomous World (AW)
Autonomous World (AW): Persistent Virtual Realities
Autonomous worlds are persistent virtual environments that continue existing and evolving even when no players are actively participating. They’re like having a Minecraft world that keeps running and changing forever.
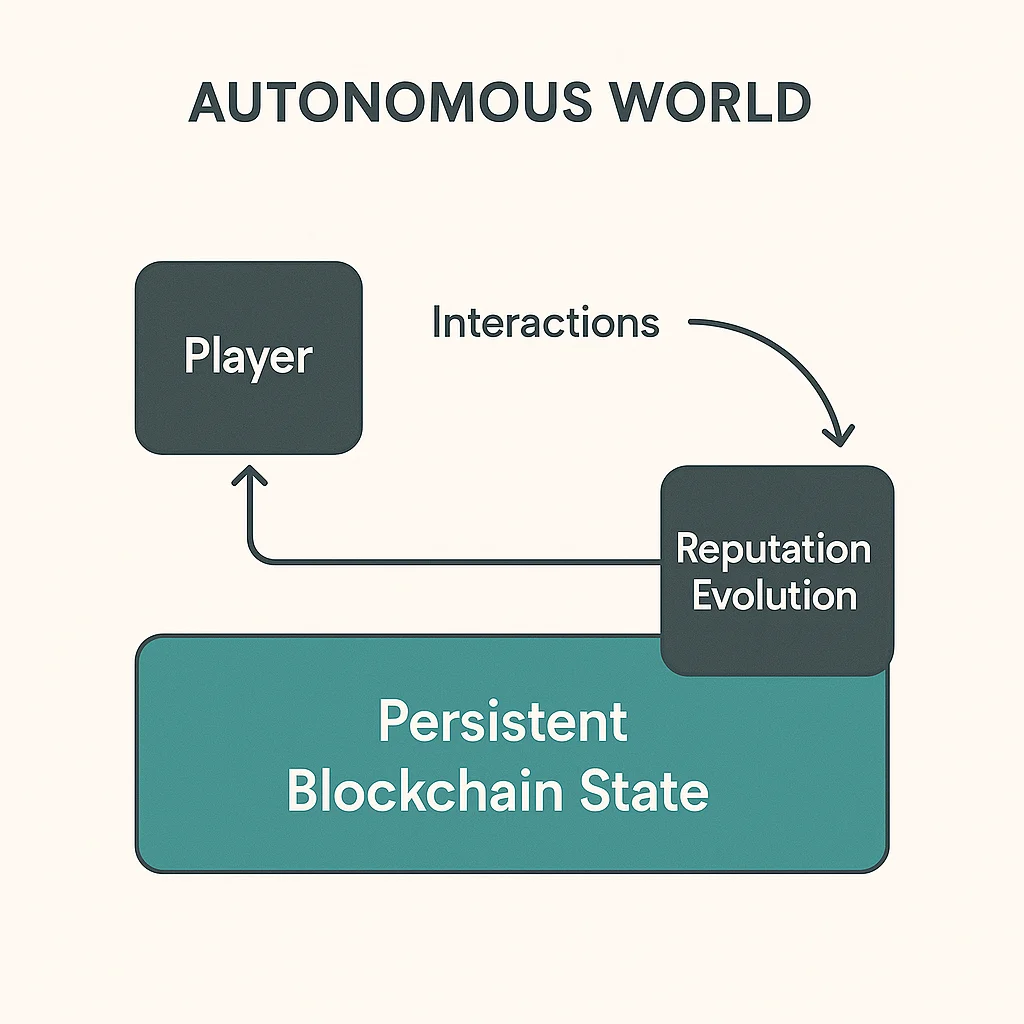
An Autonomous World (AW) is a virtual environment that operates independently through blockchain infrastructure, maintaining state and enabling interactions without requiring central servers or active management. These worlds persist and evolve according to their programmed rules.
How Autonomous Worlds Work
Blockchain persistence ensures the virtual world continues existing as long as the underlying blockchain operates, independent of any company or server infrastructure.
Player-driven evolution allows inhabitants to modify the world through their actions, with changes permanently recorded on-chain.
Economic sovereignty enables native economies with real value exchange, ownership rights, and governance systems controlled by world inhabitants.
Real-World Examples
- Dark Forest – Space exploration game that runs entirely on-chain with hidden information
- Loot derivatives creating persistent fantasy worlds based on text-based NFTs
- MUD engine provides infrastructure for building complex autonomous worlds
Why Beginners Should Care
True ownership of virtual assets and land that can’t be taken away by game companies going out of business or changing policies.
Persistent value creation where time and effort invested in virtual worlds retains value indefinitely through blockchain permanence.
Experimental economics as autonomous worlds become laboratories for testing new forms of governance, economics, and social organization.
Related Terms: Metaverse, On-Chain Gaming, Virtual Real Estate, Persistence
