Bitcoin (BTC)
Bitcoin (BTC): Digital Money That Banks Can’t Control
Bitcoin isn’t just another investment – it’s the financial revolution that started it all. When traditional banks failed us in 2008, Bitcoin emerged as the answer.
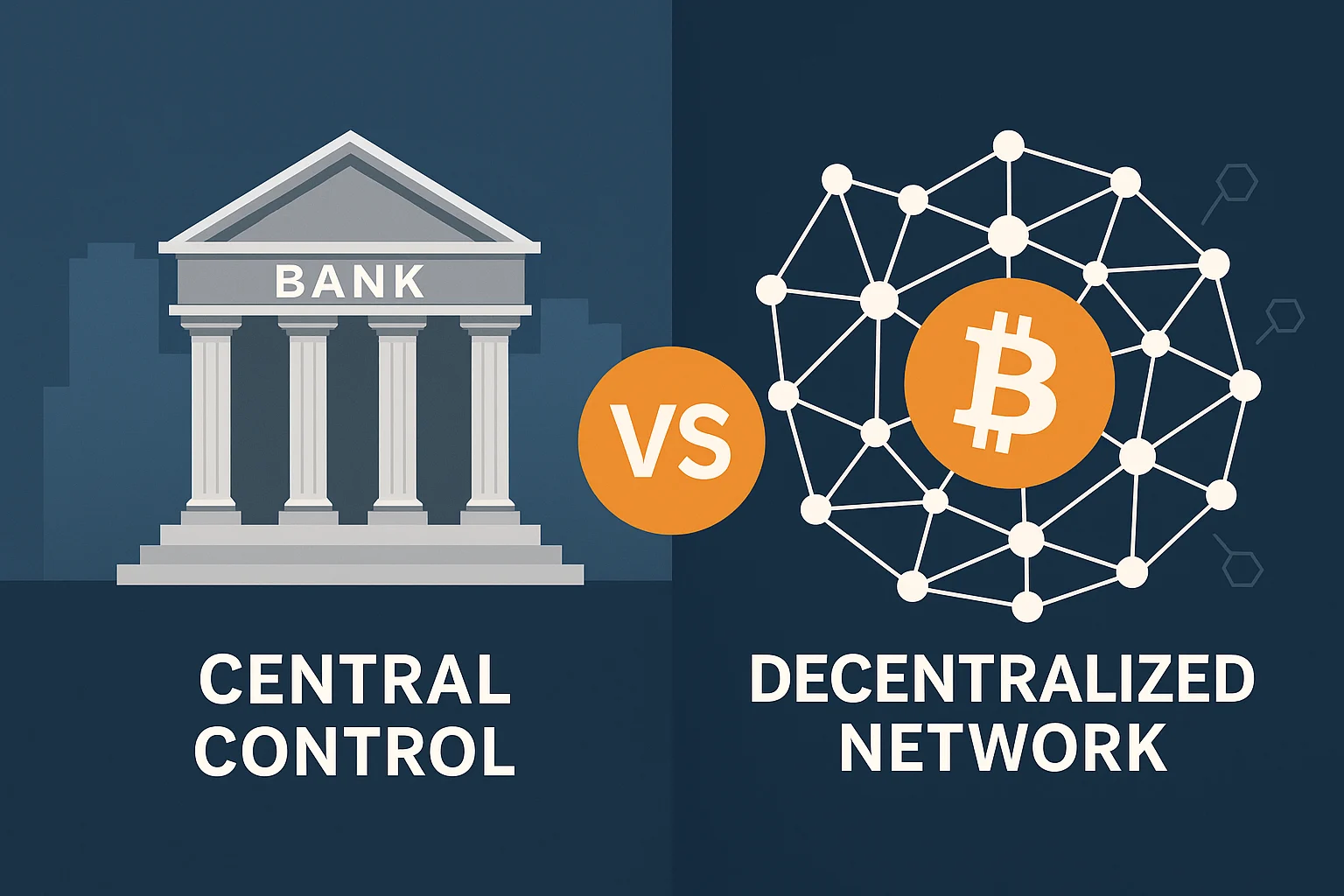
Bitcoin is digital money that operates without banks, governments, or middlemen controlling it. Think of it as cash for the internet age, but with a twist – every transaction is recorded on a public ledger that no single entity can manipulate.
How Bitcoin Works
Bitcoin runs on a network of computers worldwide. Each computer keeps a copy of every Bitcoin transaction ever made. When you send Bitcoin, the network validates your transaction and adds it to this permanent record.
No central bank prints more Bitcoin whenever they feel like it. There will only ever be 21 million Bitcoin – period. This scarcity is built into the code.
Real-World Examples
- El Salvador made Bitcoin legal tender in 2021
- MicroStrategy holds over 190,000 Bitcoin on their balance sheet
- Lightning Network enables instant Bitcoin payments for coffee or small purchases
Why Beginners Should Care
Bitcoin solved a problem that plagued digital money for decades – the double-spending problem. Before Bitcoin, digital files could be copied infinitely. Bitcoin proved that digital scarcity was possible without a trusted third party.
Whether you buy $10 or $10,000 worth, you’re participating in a monetary system that operates by mathematical rules, not political whims.
Related Terms: Blockchain, Private Key, Mining, Satoshi
