Peer-to-Peer (P2P)
Peer-to-Peer (P2P): Direct Network Communication
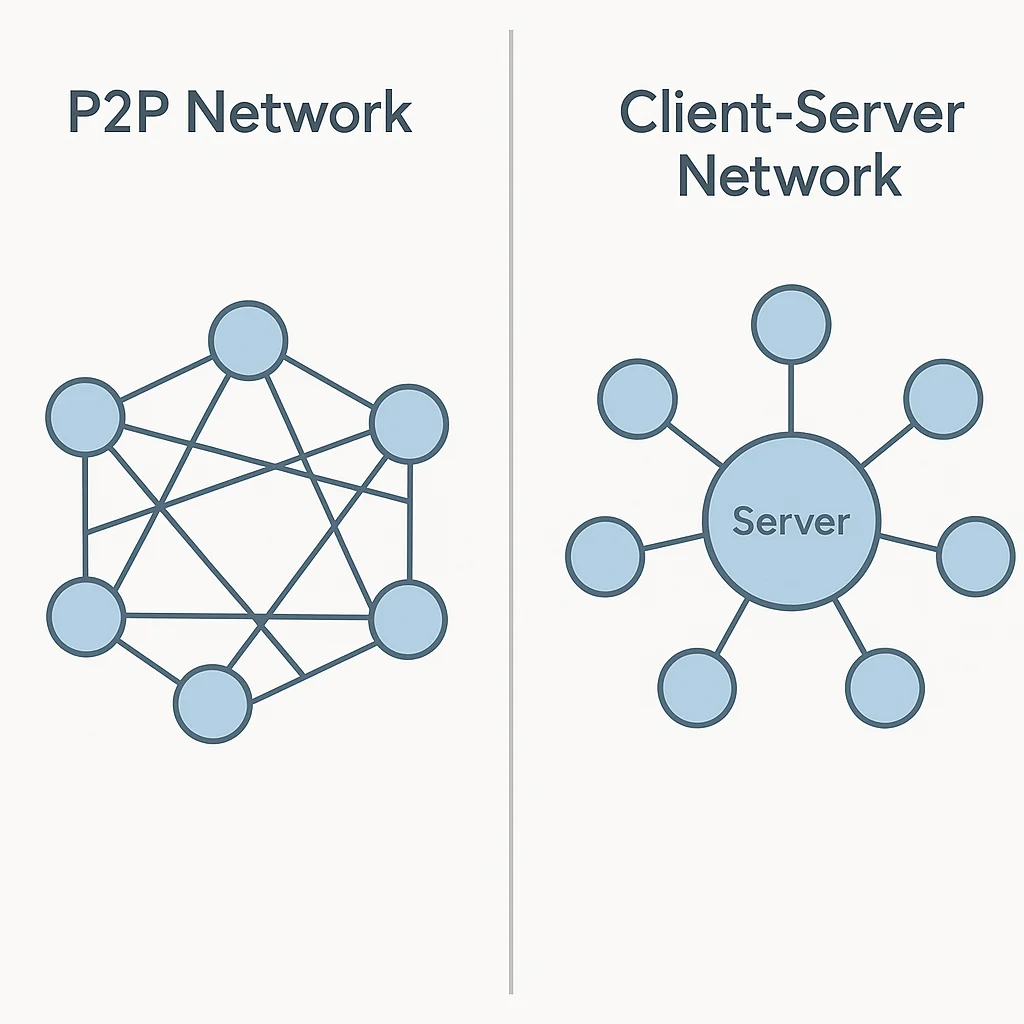
Peer-to-peer networks enable direct communication between participants without central intermediaries. It’s like having a telephone system where everyone connects directly instead of going through switchboard operators.
Peer-to-peer (P2P) refers to network architectures where participants communicate directly with each other rather than through centralized servers or intermediaries. This creates decentralized systems that are more resistant to censorship and single points of failure.
How P2P Networks Work
Direct connections enable participants to communicate, share data, and transact directly without requiring permission from central authorities.
Distributed architecture spreads network functions across many participants rather than concentrating them in centralized infrastructure.
Redundancy benefits ensure network operation continues even if some participants go offline, creating robust and resilient systems.
Real-World Examples
- Bitcoin network uses P2P architecture for transaction broadcasting and block propagation
- BitTorrent enables file sharing through direct connections between users
- Lightning Network creates P2P payment channels for instant Bitcoin transactions
Why Beginners Should Care
Censorship resistance as P2P networks can operate without central authorities that could block or restrict access.
Reduced dependencies on centralized infrastructure that could fail, be shut down, or impose restrictions on users.
Privacy benefits from direct communication that doesn’t require revealing activity to central monitoring systems.
Related Terms: Decentralization, Node,
